by Scott Muniz | Aug 16, 2021 | Security, Technology
This article is contributed. See the original author and article here.
23andme — yamale
|
23andMe Yamale before 3.0.8 allows remote attackers to execute arbitrary code via a crafted schema file. The schema parser uses eval as part of its processing, and tries to protect from malicious expressions by limiting the builtins that are passed to the eval. When processing the schema, each line is run through Python’s eval function to make the validator available. A well-constructed string within the schema rules can execute system commands; thus, by exploiting the vulnerability, an attacker can run arbitrary code on the image that invokes Yamale. |
2021-08-09 |
not yet calculated |
CVE-2021-38305
MISC
MISC |
2n_access_unit — multiple_devices
|
On 2N Access Unit 2.0 2.31.0.40.5 devices, an attacker can pose as the web relay for a man-in-the-middle attack. |
2021-08-13 |
not yet calculated |
CVE-2021-31399
MISC
MISC |
| 711cms — 711cms |
Cross Site Request Forgery (CSRF) vulnerability exists in 711cms v1.0.7 that can add an admin account via admin.php?c=Admin&m=content. |
2021-08-12 |
not yet calculated |
CVE-2020-18460
MISC |
acronis — cyber_protect15
|
Reflected cross-site scripting (XSS) was possible on the login page in Acronis Cyber Protect 15 prior to build 27009. |
2021-08-12 |
not yet calculated |
CVE-2021-38087
MISC |
acronis — cyber_protect15
|
Acronis Cyber Protect 15 for Windows prior to build 27009 allowed local privilege escalation via binary hijacking. |
2021-08-12 |
not yet calculated |
CVE-2021-38088
MISC |
acronis — cyber_protect15
|
Acronis Cyber Protect 15 for Windows prior to build 27009 and Acronis Agent for Windows prior to build 26226 allowed local privilege escalation via DLL hijacking. |
2021-08-12 |
not yet calculated |
CVE-2021-38086
MISC |
advantech — scada
|
UserExcelOut.asp within WebAccess/SCADA is vulnerable to cross-site scripting (XSS), which could allow an attacker to send malicious JavaScript code. This could result in hijacking of cookie/session tokens, redirection to a malicious webpage, and unintended browser action on the WebAccess/SCADA (WebAccess/SCADA versions prior to 8.4.5, WebAccess/SCADA versions prior to 9.0.1). |
2021-08-10 |
not yet calculated |
CVE-2021-22676
MISC |
advantech — scada
|
The affected product is vulnerable to a relative path traversal condition, which may allow an attacker access to unauthorized files and directories on the WebAccess/SCADA (WebAccess/SCADA versions prior to 8.4.5, WebAccess/SCADA versions prior to 9.0.1). |
2021-08-10 |
not yet calculated |
CVE-2021-22674
MISC |
agora — flat_server
|
The remove API in v1/controller/cloudStorage/alibabaCloud/remove/index.ts in netless Agora Flat Server before 2021-07-30 mishandles file ownership. |
2021-08-13 |
not yet calculated |
CVE-2021-38621
MISC |
aikcms — aikcms
|
File Upload vulnerabilty in AikCms v2.0.0 in poster_edit.php because the background file management office does not verify the uploaded file. |
2021-08-12 |
not yet calculated |
CVE-2020-18462
MISC |
aikcms — aikcms
|
Cross Site Request Forgery (CSRF) vulnerability exists in v2.0.0 in video_list.php, which can let a malicious user delete a video message. |
2021-08-12 |
not yet calculated |
CVE-2020-18463
MISC |
aikcms — aikcms
|
Cross Site Request Forgery (CSRF) vulnerability in AikCms 2.0.0 in video_list.php, which can let a malicious user delete movie information. |
2021-08-12 |
not yet calculated |
CVE-2020-18464
MISC |
aimanager — aimanager
|
AIMANAGER before B115 on MONITORAPP Application Insight Web Application Firewall (AIWAF) devices with Manager 2.1.0 has Improper Authentication. An attacker can gain administrative access by modifying the response to an authentication check request. |
2021-08-12 |
not yet calculated |
CVE-2021-36921
MISC
MISC
CONFIRM |
aimanager — aimanger
|
AIMANAGER before B115 on MONITORAPP Application Insight Web Application Firewall (AIWAF) devices with Manager 2.1.0 allows OS Command Injection because of missing input validation on one of the parameters of an HTTP request. |
2021-08-12 |
not yet calculated |
CVE-2021-36982
MISC
MISC
CONFIRM |
alpine — alpine
|
In Alpine through 2.24, untagged responses from an IMAP server are accepted before STARTTLS. |
2021-08-10 |
not yet calculated |
CVE-2021-38370
MISC
MISC |
altova — mobiletogether_server
|
Altova MobileTogether Server before 7.3 SP1 allows XXE attacks, such as an InfoSetChanges/Changes attack against /workflowmanagement, or reading mobiletogetherserver.cfg and then reading the certificate and private key. |
2021-08-10 |
not yet calculated |
CVE-2021-37425
MISC
MISC
MISC
MISC |
altova — mobiletogether_server
|
Altova MobileTogether Server before 7.3 SP1 allows XML exponential entity expansion, a different vulnerability than CVE-2021-37425. |
2021-08-10 |
not yet calculated |
CVE-2021-38490
MISC |
amazon — aws
|
Amazon AWS CloudFront TLSv1.2_2019 allows TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256 and TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384, which some entities consider to be weak ciphers. |
2021-08-12 |
not yet calculated |
CVE-2020-36363
MISC
MISC |
asyncapi — asyncapi
|
@asyncapi/java-spring-cloud-stream-template generates a Spring Cloud Stream (SCSt) microservice. In versions prior to 0.7.0 arbitrary code injection was possible when an attacker controls the AsyncAPI document. An example is provided in GHSA-xj6r-2jpm-qvxp. There are no mitigations available and all users are advised to update. |
2021-08-11 |
not yet calculated |
CVE-2021-37694
CONFIRM |
| at&t_labs — xmill |
A stack-based buffer overflow vulnerability exists in the command-line-parsing HandleFileArg functionality of AT&T Labs’ Xmill 0.7. Within the function HandleFileArg the argument filepattern is under control of the user who passes it in from the command line. filepattern is passed directly to strcpy copying the path provided by the user into a static sized buffer without any length checks resulting in a stack-buffer overflow. An attacker can provide malicious input to trigger these vulnerabilities. |
2021-08-13 |
not yet calculated |
CVE-2021-21812
MISC |
at&t_labs — xmill
|
A heap-based buffer overflow vulnerability exists in the XML Decompression EnumerationUncompressor::UncompressItem functionality of AT&T Labs’ Xmill 0.7. A specially crafted XMI file can lead to remote code execution. An attacker can provide a malicious file to trigger this vulnerability. |
2021-08-13 |
not yet calculated |
CVE-2021-21829
MISC |
at&t_labs — xmill
|
Within the function HandleFileArg the argument filepattern is under control of the user who passes it in from the command line. filepattern is passed directly to strlen to determine the ending location of the char* passed in by the user, no checks are done to see if the passed in char* is longer than the staticly sized buffer data is memcpy‘d into, but after the memcpy a null byte is written to what is assumed to be the end of the buffer to terminate the char*, but without length checks, this null write occurs at an arbitrary offset from the buffer. An attacker can provide malicious input to trigger this vulnerability. |
2021-08-13 |
not yet calculated |
CVE-2021-21814
MISC |
at&t_labs — xmill
|
Within the function HandleFileArg the argument filepattern is under control of the user who passes it in from the command line. filepattern is passed directly to memcpy copying the path provided by the user into a staticly sized buffer without any length checks resulting in a stack-buffer overflow. |
2021-08-13 |
not yet calculated |
CVE-2021-21813
MISC |
at&t_labs — xmill
|
A heap-based buffer overflow vulnerability exists in the XML Decompression LabelDict::Load functionality of AT&T Labs’ Xmill 0.7. A specially crafted XMI file can lead to remote code execution. An attacker can provide a malicious file to trigger this vulnerability. |
2021-08-13 |
not yet calculated |
CVE-2021-21830
MISC |
at&t_labs — xmill
|
A stack-based buffer overflow vulnerability exists in the command-line-parsing HandleFileArg functionality of AT&T Labs’ Xmill 0.7. Within the function HandleFileArg the argument filepattern is under control of the user who passes it in from the command line. filepattern is passed directly to strcpy copying the path provided by the user into a staticly sized buffer without any length checks resulting in a stack-buffer overflow. An attacker can provide malicious input to trigger this vulnerability. |
2021-08-13 |
not yet calculated |
CVE-2021-21815
MISC |
azure — cyclecloud
|
Azure CycleCloud Elevation of Privilege Vulnerability This CVE ID is unique from CVE-2021-36943. |
2021-08-12 |
not yet calculated |
CVE-2021-33762
N/A |
belledonne — belle-sip
|
Belledonne Belle-sip before 4.5.20, as used in Linphone and other products, can crash via an invalid From header in a SIP message. |
2021-08-12 |
not yet calculated |
CVE-2021-33056
MISC
CONFIRM |
bento4 — bento4
|
An issue was discovered in Bento4 v1.5.1.0. There is a heap-buffer-overflow in AP4_Dec3Atom::AP4_Dec3Atom at Ap4Dec3Atom.cpp, leading to a denial of service (program crash), as demonstrated by mp42aac. |
2021-08-13 |
not yet calculated |
CVE-2020-21066
MISC |
bento4 — bento4
|
A buffer-overflow vulnerability in the AP4_RtpAtom::AP4_RtpAtom function in Ap4RtpAtom.cpp of Bento4 1.5.1.0 allows attackers to cause a denial of service. |
2021-08-13 |
not yet calculated |
CVE-2020-21064
MISC |
bootloader — bootloader
|
Bootloader contains a vulnerability in the NV3P server where any user with physical access through USB can trigger an incorrect bounds check, which may lead to buffer overflow, resulting in limited information disclosure, limited data integrity, and information disclosure across all components. |
2021-08-11 |
not yet calculated |
CVE-2021-1111
MISC |
brocade — fabric_os
|
The command “ipfilter” in Brocade Fabric OS before Brocade Fabric OS v.9.0.1a, v8.2.3, and v8.2.0_CBN4, and v7.4.2h uses unsafe string function to process user input. Authenticated attackers can abuse this vulnerability to exploit stack-based buffer overflows, allowing execution of arbitrary code as the root user account. |
2021-08-12 |
not yet calculated |
CVE-2021-27790
MISC |
brocade — fabric_os
|
The command “ipfilter” in Brocade Fabric OS before Brocade Fabric OS v.9.0.1a, v8.2.3, and v8.2.0_CBN4, and v7.4.2h uses unsafe string function to process user input. Authenticated attackers can abuse this vulnerability to exploit stack-based buffer overflows, allowing execution of arbitrary code as the root user account. |
2021-08-12 |
not yet calculated |
CVE-2021-27792
MISC |
brocade — fabric_os
|
The function that is used to parse the Authentication header in Brocade Fabric OS Web application service before Brocade Fabric OS v9.0.1a and v8.2.3a fails to properly process a malformed authentication header from the client, resulting in reading memory addresses outside the intended range. An unauthenticated attacker could discover a request, which could bypass the authentication process. |
2021-08-12 |
not yet calculated |
CVE-2021-27791
MISC |
brocade — fabric_os
|
ntermittent authorization failure in aaa tacacs+ with Brocade Fabric OS versions before Brocade Fabric OS v9.0.1b and after 9.0.0, also in Brocade Fabric OS before Brocade Fabric OS v8.2.3a and after v8.2.0 could cause a user with a valid account to be unable to log into the switch. |
2021-08-12 |
not yet calculated |
CVE-2021-27793
MISC |
brocade — fabric_os
|
A vulnerability in the authentication mechanism of Brocade Fabric OS versions before Brocade Fabric OS v.9.0.1a, v8.2.3a and v7.4.2h could allow a user to Login with empty password, and invalid password through telnet, ssh and REST. |
2021-08-12 |
not yet calculated |
CVE-2021-27794
MISC |
btrbk — btrbk
|
Btrbk before 0.31.2 allows command execution because of the mishandling of remote hosts filtering SSH commands using ssh_filter_btrbk.sh in authorized_keys. |
2021-08-07 |
not yet calculated |
CVE-2021-38173
MISC
CONFIRM |
bycms — bycms
|
Cross Site Request Forgery (CSRF) vulnerability in bycms v1.3 via admin.php/systems/index/module_id/70/group_id/1.html. |
2021-08-12 |
not yet calculated |
CVE-2020-18454
MISC |
bycms — bycms
|
Cross Site Request Forgery (CSRF) vulnerability exists in bycms v1.3.0 that can add an admin account via admin.php/ucenter/add.html. |
2021-08-12 |
not yet calculated |
CVE-2020-18457
MISC |
bycms — bycms
|
Cross Site Scripting (XSS) vulnerability exists in bycms v3.0.4 via the title parameter in the edit function in Document.php. |
2021-08-12 |
not yet calculated |
CVE-2020-18455
MISC |
canon — tr150
|
The Canon TR150 print driver through 3.71.2.10 is vulnerable to a privilege escalation issue. During the add printer process, a local attacker can overwrite CNMurGE.dll and, if timed properly, the overwritten DLL will be loaded into a SYSTEM process resulting in escalation of privileges. This occurs because the driver drops a world-writable DLL into a CanonBJ %PROGRAMDATA% location that gets loaded by printisolationhost (a system process). |
2021-08-11 |
not yet calculated |
CVE-2021-38085
MISC
MISC |
chamilo — lms
|
A user without privileges in Chamilo LMS 1.11.14 can send an invitation message to another user, e.g., the administrator, through main/social/search.php, main/inc/lib/social.lib.php and steal cookies or execute arbitrary code on the administration side via a stored XSS vulnerability via social network the send invitation feature. |
2021-08-10 |
not yet calculated |
CVE-2021-37391
MISC |
chamilo — lms
|
A Chamilo LMS 1.11.14 reflected XSS vulnerability exists in main/social/search.php=q URI (social network search feature). |
2021-08-10 |
not yet calculated |
CVE-2021-37390
MISC
MISC |
chamilo — lms
|
Chamilo 1.11.14 allows stored XSS via main/install/index.php and main/install/ajax.php through the port parameter. |
2021-08-10 |
not yet calculated |
CVE-2021-37389
MISC
MISC |
ckeditor — ckeditor
|
ckeditor is an open source WYSIWYG HTML editor with rich content support. A vulnerability has been discovered in the clipboard Widget plugin if used alongside the undo feature. The vulnerability allows a user to abuse undo functionality using malformed widget HTML, which could result in executing JavaScript code. It affects all users using the CKEditor 4 plugins listed above at version >= 4.13.0. The problem has been recognized and patched. The fix will be available in version 4.16.2. |
2021-08-12 |
not yet calculated |
CVE-2021-32808
CONFIRM
MISC |
ckeditor — ckeditor
|
ckeditor is an open source WYSIWYG HTML editor with rich content support. A potential vulnerability has been discovered in CKEditor 4 [Clipboard](https://ckeditor.com/cke4/addon/clipboard) package. The vulnerability allowed to abuse paste functionality using malformed HTML, which could result in injecting arbitrary HTML into the editor. It affects all users using the CKEditor 4 plugins listed above at version >= 4.5.2. The problem has been recognized and patched. The fix will be available in version 4.16.2. |
2021-08-12 |
not yet calculated |
CVE-2021-32809
CONFIRM |
ckeditor — ckeditor
|
ckeditor is an open source WYSIWYG HTML editor with rich content support. A potential vulnerability has been discovered in CKEditor 4 [Fake Objects](https://ckeditor.com/cke4/addon/fakeobjects) package. The vulnerability allowed to inject malformed Fake Objects HTML, which could result in executing JavaScript code. It affects all users using the CKEditor 4 plugins listed above at version < 4.16.2. The problem has been recognized and patched. The fix will be available in version 4.16.2. |
2021-08-13 |
not yet calculated |
CVE-2021-37695
MISC
CONFIRM |
| contao — contao |
Contao is an open source CMS that allows you to create websites and scalable web applications. In affected versions it is possible to load PHP files by entering insert tags in the Contao back end. Installations are only affected if they have untrusted back end users who have the rights to modify fields that are shown in the front end. Update to Contao 4.4.56, 4.9.18 or 4.11.7 to resolve. If you cannot update then disable the login for untrusted back end users. |
2021-08-11 |
not yet calculated |
CVE-2021-37626
MISC
CONFIRM |
contao — contao
|
Contao is an open source CMS that allows creation of websites and scalable web applications. In affected versions it is possible to gain privileged rights in the Contao back end. Installations are only affected if they have untrusted back end users who have access to the form generator. All users are advised to update to Contao 4.4.56, 4.9.18 or 4.11.7. As a workaround users may disable the form generator or disable the login for untrusted back end users. |
2021-08-11 |
not yet calculated |
CVE-2021-37627
CONFIRM
MISC |
contao — contao
|
Contao >=4.0.0 allows backend XSS via HTML attributes to an HTML field. Fixed in 4.4.56, 4.9.18, 4.11.7. |
2021-08-12 |
not yet calculated |
CVE-2021-35955
MISC
MISC |
| contiki — contiki |
In Contiki 3.0, a buffer overflow in the Telnet service allows remote attackers to cause a denial of service because the ls command is mishandled when a directory has many files with long names. |
2021-08-10 |
not yet calculated |
CVE-2021-38386
MISC |
contiki — contiki
|
In Contiki 3.0, a Telnet server that silently quits (before disconnection with clients) leads to connected clients entering an infinite loop and waiting forever, which may cause excessive CPU consumption. |
2021-08-10 |
not yet calculated |
CVE-2021-38387
MISC |
contiki — contiki
|
In Contiki 3.0, potential nonterminating acknowledgment loops exist in the Telnet service. When the negotiated options are already disabled, servers still respond to DONT and WONT requests with WONT or DONT commands, which may lead to infinite acknowledgment loops, denial of service, and excessive CPU consumption. |
2021-08-09 |
not yet calculated |
CVE-2021-38311
MISC |
| cpanel — cpanel |
In cPanel before 98.0.1, /scripts/cpan_config performs unsafe operations on files (SEC-589). |
2021-08-11 |
not yet calculated |
CVE-2021-38586
MISC |
| cpanel — cpanel |
In cPanel before 96.0.13, scripts/fix-cpanel-perl mishandles the creation of temporary files (SEC-586). |
2021-08-11 |
not yet calculated |
CVE-2021-38587
MISC |
cpanel — cpanel
|
The WHM Locale Upload feature in cPanel before 98.0.1 allows unserialization attacks (SEC-585). |
2021-08-11 |
not yet calculated |
CVE-2021-38585
MISC |
cpanel — cpanel
|
The WHM Locale Upload feature in cPanel before 98.0.1 allows XXE attacks (SEC-585). |
2021-08-11 |
not yet calculated |
CVE-2021-38584
MISC |
cpanel — cpanel
|
In cPanel before 96.0.8, weak permissions on web stats can lead to information disclosure (SEC-584). |
2021-08-11 |
not yet calculated |
CVE-2021-38590
MISC |
cpanel — cpanel
|
In cPanel before 96.0.13, fix_cpanel_perl lacks verification of the integrity of downloads (SEC-587). |
2021-08-11 |
not yet calculated |
CVE-2021-38588
MISC |
cpanel — cpanel
|
In cPanel before 96.0.13, scripts/fix-cpanel-perl does not properly restrict the overwriting of files (SEC-588). |
2021-08-11 |
not yet calculated |
CVE-2021-38589
MISC |
creative — pebble_devices
|
CREATIVE Pebble devices through 2021-08-09 allow remote attackers to recover speech signals from an LED on the device, via a telescope and an electro-optical sensor, aka a “Glowworm” attack. The power indicator LED of the speakers is connected directly to the power line, as a result, the intensity of a device’s power indicator LED is correlative to the power consumption. The sound played by the speakers affects their power consumption and as a result is also correlative to the light intensity of the LEDs. By analyzing measurements obtained from an electro-optical sensor directed at the power indicator LEDs of the speakers, we can recover the sound played by them. |
2021-08-11 |
not yet calculated |
CVE-2021-38546
MISC |
d-link — dir-825
|
** UNSUPPORTED WHEN ASSIGNED **Null Pointer Dereference vulnerability in D-Link DIR-825 2.10b02, which could let a remote malicious user cause a denial of service. The vulnerability could be triggered by sending an HTTP request with URL /vct_wan; the sbin/httpd would invoke the strchr function and take NULL as a first argument, which finally leads to the segmentation fault. NOTE: The DIR-825 and all hardware revisions is considered End of Life and as such this issue will not be patched. |
2021-08-10 |
not yet calculated |
CVE-2021-29296
MISC
MISC |
d-link — dsl-274or
|
** UNSUPPORTED WHEN ASSIGNED ** Null Pointer Dereference vulnerability exists in D-Link DSL-2740R UK_1.01, which could let a remove malicious user cause a denial of service via the send_hnap_unauthorized function. It could be triggered by sending crafted POST request to /HNAP1/. NOTE: The DSL-2740R and all hardware revisions are considered End of Life and as such this issue will not be patched. |
2021-08-10 |
not yet calculated |
CVE-2021-29294
MISC
MISC |
d-link — dsp-w215
|
** UNSUPPORTED WHEN ASSIGNED **Null Pointer Dereference vulnerability exists in D-Link DSP-W215 1.10, which could let a remote malicious user cause a denial of servie via usr/bin/lighttpd. It could be triggered by sending an HTTP request without URL in the start line directly to the device. NOTE: The DSP-W215 and all hardware revisions is considered End of Life and as such this issue will not be patched. |
2021-08-10 |
not yet calculated |
CVE-2021-29295
MISC
MISC |
| d-link — multiple_devices |
Null Pointer Dereference vulnerability exists in D-Link DAP-2310 2.07.RC031, DAP-2330 1.07.RC028, DAP-2360 2.07.RC043, DAP-2553 3.06.RC027, DAP-2660 1.13.RC074, DAP-2690 3.16.RC100, DAP-2695 1.17.RC063, DAP-3320 1.01.RC014 and DAP-3662 1.01.RC022 in the upload_certificate function of sbin/httpd binary. When the binary handle the specific HTTP GET request, the strrchr in the upload_certificate function would take NULL as first argument, and incur the NULL pointer dereference vulnerability. |
2021-08-10 |
not yet calculated |
CVE-2021-28839
MISC
MISC
MISC |
| d-link — multiple_devices |
Null pointer dereference vulnerability in D-Link DAP-2310 2,10RC039, DAP-2330 1.10RC036 BETA, DAP-2360 2.10RC055, DAP-2553 3.10rc039 BETA, DAP-2660 1.15rc131b, DAP-2690 3.20RC115 BETA, DAP-2695 1.20RC093, DAP-3320 1.05RC027 BETA and DAP-3662 1.05rc069 in the sbin/httpd binary. The crash happens at the `atoi’ operation when a specific network package are sent to the httpd binary. |
2021-08-10 |
not yet calculated |
CVE-2021-28838
MISC
MISC
MISC |
d-link — multiple_devices
|
Null Pointer Dereference vulnerability exists in D-Link DAP-2310 2.07.RC031, DAP-2330 1.07.RC028, DAP-2360 2.07.RC043, DAP-2553 3.06.RC027, DAP-2660 1.13.RC074, DAP-2690 3.16.RC100, DAP-2695 1.17.RC063, DAP-3320 1.01.RC014 and DAP-3662 1.01.RC022 in the upload_config function of sbin/httpd binary. When the binary handle the specific HTTP GET request, the content in upload_file variable is NULL in the upload_config function then the strncasecmp would take NULL as first argument, and incur the NULL pointer dereference vulnerability. |
2021-08-10 |
not yet calculated |
CVE-2021-28840
MISC
MISC
MISC |
damicms — damicms
|
Cross Site Request Forgery (CSRF) vulnerability exists in DamiCMS v6.0.6 that can add an admin account via admin.php?s=/Admin/doadd. |
2021-08-12 |
not yet calculated |
CVE-2020-18458
MISC |
| dell — command |
Dell Command Update, Dell Update, and Alienware Update versions prior to 4.3 contains a Improper Certificate Verification vulnerability. A local authenticated malicious user could exploit this vulnerability by modifying local configuration files in order to execute arbitrary code on the system. |
2021-08-09 |
not yet calculated |
CVE-2021-36277
CONFIRM |
dell — dbutilldrv2
|
Dell DBUtilDrv2.sys driver (versions 2.5 and 2.6) contains an insufficient access control vulnerability which may lead to escalation of privileges, denial of service, or information disclosure. Local authenticated user access is required. |
2021-08-09 |
not yet calculated |
CVE-2021-36276
CONFIRM |
dell — emc_data_protection_search
|
Dell EMC Data Protection Search, 19.4 and prior, and IDPA, 2.6.1 and prior, contain an Information Exposure in Log File Vulnerability in CIS. A local low privileged attacker could potentially exploit this vulnerability, leading to the disclosure of certain user credentials. The attacker may be able to use the exposed credentials to access the vulnerable application with the privileges of the compromised account. |
2021-08-10 |
not yet calculated |
CVE-2021-21601
CONFIRM |
dell — emc_networker
|
Dell EMC NetWorker, 19.4 or older, contain an uncontrolled resource consumption flaw in its API service. An authorized API user could potentially exploit this vulnerability via the web and desktop user interfaces, leading to denial of service in the manageability path. |
2021-08-10 |
not yet calculated |
CVE-2021-21600
CONFIRM |
dell — powerscale_onefs
|
Dell PowerScale OneFS 9.1.0.x contains an improper privilege management vulnerability. It may allow an authenticated user with ISI_PRIV_LOGIN_SSH and/or ISI_PRIV_LOGIN_CONSOLE to elevate privilege. |
2021-08-10 |
not yet calculated |
CVE-2021-21567
CONFIRM |
dell — wyse_thinos
|
Dell Wyse ThinOS, version 9.0, contains a Sensitive Information Disclosure Vulnerability. An authenticated malicious user with physical access to the system could exploit this vulnerability to read sensitive information written to the log files. |
2021-08-10 |
not yet calculated |
CVE-2021-21597
CONFIRM |
dell — wyse_thinos
|
Dell Wyse ThinOS, versions 9.0, 9.1, and 9.1 MR1, contain a Sensitive Information Disclosure Vulnerability. An authenticated attacker with physical access to the system could exploit this vulnerability to read sensitive Smartcard data in log files. |
2021-08-10 |
not yet calculated |
CVE-2021-21598
CONFIRM |
discourse — discourse
|
Discourse is an open-source platform for community discussion. In Discourse before versions 2.7.8 and 2.8.0.beta5, a user’s read state for a topic such as the last read post number and the notification level is exposed. |
2021-08-13 |
not yet calculated |
CVE-2021-37703
CONFIRM
MISC |
discourse — discourse
|
Discourse is an open source discussion platform. In versions prior to 2.7.8 rendering of d-popover tooltips can be susceptible to XSS attacks. This vulnerability only affects sites which have modified or disabled Discourse’s default Content Security Policy. This issue is patched in the latest `stable` 2.7.8 version of Discourse. As a workaround users may ensure that the Content Security Policy is enabled, and has not been modified in a way which would make it more vulnerable to XSS attacks. |
2021-08-09 |
not yet calculated |
CVE-2021-37633
MISC
CONFIRM |
discourse — discourse
|
Discourse is an open-source platform for community discussion. In Discourse before versions 2.7.8 and 2.8.0.beta4, when adding additional email addresses to an existing account on a Discourse site an email token is generated as part of the email verification process. Deleting the additional email address does not invalidate an unused token which can then be used in other contexts, including reseting a password. |
2021-08-13 |
not yet calculated |
CVE-2021-37693
CONFIRM
MISC |
docker — desktop
|
Docker Desktop before 3.6.0 suffers from incorrect access control. If a low-privileged account is able to access the server running the Windows containers, it can lead to a full container compromise in both process isolation and Hyper-V isolation modes. This security issue leads an attacker with low privilege to read, write and possibly even execute code inside the containers. |
2021-08-12 |
not yet calculated |
CVE-2021-37841
MISC |
domainmod — domainmod
|
A cross-site request forgery (CSRF) in /admin/maintenance/ of Domainmod 4.13 allows attackers to arbitrarily delete logs. |
2021-08-12 |
not yet calculated |
CVE-2020-20989
MISC |
domainmod — domainmod
|
A cross site scripting (XSS) vulnerability in the /segments/edit.php component of Domainmod 4.13 allows attackers to execute arbitrary web scripts or HTML via the Segment Name parameter. |
2021-08-12 |
not yet calculated |
CVE-2020-20990
MISC |
domainmod — domainmod
|
A cross site scripting (XSS) vulnerability in the /domains/cost-by-owner.php component of Domainmod 4.13 allows attackers to execute arbitrary web scripts or HTML via a crafted payload in the “or Expiring Between” parameter. |
2021-08-12 |
not yet calculated |
CVE-2020-20988
MISC |
| dut — computer_control_engineering |
An information disclosure vulnerability exists within Dut Computer Control Engineering Co.’s PLC MAC1100. |
2021-08-13 |
not yet calculated |
CVE-2020-18754
MISC |
| dut — computer_control_engineering |
An issue in Dut Computer Control Engineering Co.’s PLC MAC1100 allows attackers to cause persistent denial of service (DOS) via a crafted packet. |
2021-08-13 |
not yet calculated |
CVE-2020-18757
MISC |
dut — computer_control_engineering
|
An issue in Dut Computer Control Engineering Co.’s PLC MAC1100 allows attackers to gain access to the system and escalate privileges via a crafted packet. |
2021-08-13 |
not yet calculated |
CVE-2020-18753
MISC |
dut — computer_control_engineering
|
An arbitrary memory access vulnerability in the EPA protocol of Dut Computer Control Engineering Co.’s PLC MAC1100 allows attackers to read the contents of any variable area. |
2021-08-13 |
not yet calculated |
CVE-2020-18756
MISC |
dut — computer_control_engineering
|
An information disclosure vulnerability exists in the EPA protocol of Dut Computer Control Engineering Co.’s PLC MAC1100. |
2021-08-13 |
not yet calculated |
CVE-2020-18759
MISC |
dut — computer_control_engineering
|
An issue in Dut Computer Control Engineering Co.’s PLC MAC1100 allows attackers to execute arbitrary code. |
2021-08-13 |
not yet calculated |
CVE-2020-18758
MISC |
easycorp — zentao_pms
|
The EasyCorp ZenTao PMS 12.4.2 application suffers from an arbitrary file upload vulnerability. An attacker can upload arbitrary webshell to the server by using the downloadZipPackage() function. |
2021-08-12 |
not yet calculated |
CVE-2020-28165
MISC |
encode.pm — encode.pm
|
Encode.pm, as distributed in Perl through 5.34.0, allows local users to gain privileges via a Trojan horse Encode::ConfigLocal library (in the current working directory) that preempts dynamic module loading. Exploitation requires an unusual configuration, and certain 2021 versions of Encode.pm (3.05 through 3.11). This issue occurs because the || operator evaluates @INC in a scalar context, and thus @INC has only an integer value. |
2021-08-11 |
not yet calculated |
CVE-2021-36770
MISC
CONFIRM
CONFIRM
CONFIRM
CONFIRM |
exim — exim
|
The STARTTLS feature in Exim through 4.94.2 allows response injection (buffering) during MTA SMTP sending. |
2021-08-10 |
not yet calculated |
CVE-2021-38371
MISC
MISC
MISC |
exiv2 — exiv2
|
Exiv2 is a command-line utility and C++ library for reading, writing, deleting, and modifying the metadata of image files. An infinite loop was found in Exiv2 versions v0.27.4 and earlier. The infinite loop is triggered when Exiv2 is used to print the metadata of a crafted image file. An attacker could potentially exploit the vulnerability to cause a denial of service, if they can trick the victim into running Exiv2 on a crafted image file. Note that this bug is only triggered when printing the image ICC profile, which is a less frequently used Exiv2 operation that requires an extra command line option (`-p C`). The bug is fixed in version v0.27.5. |
2021-08-09 |
not yet calculated |
CVE-2021-37621
MISC
CONFIRM |
exiv2 — exiv2
|
Exiv2 is a command-line utility and C++ library for reading, writing, deleting, and modifying the metadata of image files. A null pointer dereference was found in Exiv2 versions v0.27.4 and earlier. The null pointer dereference is triggered when Exiv2 is used to print the metadata of a crafted image file. An attacker could potentially exploit the vulnerability to cause a denial of service, if they can trick the victim into running Exiv2 on a crafted image file. Note that this bug is only triggered when printing the interpreted (translated) data, which is a less frequently used Exiv2 operation that requires an extra command line option (`-p t` or `-P t`). The bug is fixed in version v0.27.5. |
2021-08-09 |
not yet calculated |
CVE-2021-37615
MISC
CONFIRM |
exiv2 — exiv2
|
Exiv2 is a command-line utility and C++ library for reading, writing, deleting, and modifying the metadata of image files. An out-of-bounds read was found in Exiv2 versions v0.27.4 and earlier. The out-of-bounds read is triggered when Exiv2 is used to read the metadata of a crafted image file. An attacker could potentially exploit the vulnerability to cause a denial of service, if they can trick the victim into running Exiv2 on a crafted image file. The bug is fixed in version v0.27.5. |
2021-08-09 |
not yet calculated |
CVE-2021-37620
MISC
CONFIRM |
exiv2 — exiv2
|
Exiv2 is a command-line utility and C++ library for reading, writing, deleting, and modifying the metadata of image files. An out-of-bounds read was found in Exiv2 versions v0.27.4 and earlier. The out-of-bounds read is triggered when Exiv2 is used to write metadata into a crafted image file. An attacker could potentially exploit the vulnerability to cause a denial of service by crashing Exiv2, if they can trick the victim into running Exiv2 on a crafted image file. Note that this bug is only triggered when writing the metadata, which is a less frequently used Exiv2 operation than reading the metadata. For example, to trigger the bug in the Exiv2 command-line application, you need to add an extra command-line argument such as insert. The bug is fixed in version v0.27.5. |
2021-08-09 |
not yet calculated |
CVE-2021-37619
MISC
CONFIRM |
exiv2 — exiv2
|
Exiv2 is a command-line utility and C++ library for reading, writing, deleting, and modifying the metadata of image files. An out-of-bounds read was found in Exiv2 versions v0.27.4 and earlier. The out-of-bounds read is triggered when Exiv2 is used to print the metadata of a crafted image file. An attacker could potentially exploit the vulnerability to cause a denial of service, if they can trick the victim into running Exiv2 on a crafted image file. Note that this bug is only triggered when printing the image ICC profile, which is a less frequently used Exiv2 operation that requires an extra command line option (`-p C`). The bug is fixed in version v0.27.5. |
2021-08-09 |
not yet calculated |
CVE-2021-37618
CONFIRM
MISC |
exiv2 — exiv2
|
Exiv2 is a command-line utility and C++ library for reading, writing, deleting, and modifying the metadata of image files. A null pointer dereference was found in Exiv2 versions v0.27.4 and earlier. The null pointer dereference is triggered when Exiv2 is used to print the metadata of a crafted image file. An attacker could potentially exploit the vulnerability to cause a denial of service, if they can trick the victim into running Exiv2 on a crafted image file. Note that this bug is only triggered when printing the interpreted (translated) data, which is a less frequently used Exiv2 operation that requires an extra command line option (`-p t` or `-P t`). The bug is fixed in version v0.27.5. |
2021-08-09 |
not yet calculated |
CVE-2021-37616
MISC
CONFIRM |
exiv2 — exiv2
|
Exiv2 is a command-line utility and C++ library for reading, writing, deleting, and modifying the metadata of image files. The assertion failure is triggered when Exiv2 is used to modify the metadata of a crafted image file. An attacker could potentially exploit the vulnerability to cause a denial of service, if they can trick the victim into running Exiv2 on a crafted image file. Note that this bug is only triggered when modifying the metadata, which is a less frequently used Exiv2 operation than reading the metadata. For example, to trigger the bug in the Exiv2 command-line application, you need to add an extra command-line argument such as `fi`. ### Patches The bug is fixed in version v0.27.5. ### References Regression test and bug fix: #1739 ### For more information Please see our [security policy](https://github.com/Exiv2/exiv2/security/policy) for information about Exiv2 security. |
2021-08-09 |
not yet calculated |
CVE-2021-32815
CONFIRM
MISC |
exiv2 — exiv2
|
Exiv2 is a command-line utility and C++ library for reading, writing, deleting, and modifying the metadata of image files. An infinite loop is triggered when Exiv2 is used to read the metadata of a crafted image file. An attacker could potentially exploit the vulnerability to cause a denial of service, if they can trick the victim into running Exiv2 on a crafted image file. The bug is fixed in version v0.27.5. |
2021-08-09 |
not yet calculated |
CVE-2021-34334
MISC
CONFIRM |
exiv2 — exiv2
|
Exiv2 is a command-line utility and C++ library for reading, writing, deleting, and modifying the metadata of image files. A floating point exception (FPE) due to an integer divide by zero was found in Exiv2 versions v0.27.4 and earlier. The FPE is triggered when Exiv2 is used to print the metadata of a crafted image file. An attacker could potentially exploit the vulnerability to cause a denial of service, if they can trick the victim into running Exiv2 on a crafted image file. Note that this bug is only triggered when printing the interpreted (translated) data, which is a less frequently used Exiv2 operation that requires an extra command line option (`-p t` or `-P t`). The bug is fixed in version v0.27.5. |
2021-08-09 |
not yet calculated |
CVE-2021-34335
CONFIRM
MISC |
exiv2 — exiv2
|
Exiv2 is a command-line utility and C++ library for reading, writing, deleting, and modifying the metadata of image files. An infinite loop was found in Exiv2 versions v0.27.4 and earlier. The infinite loop is triggered when Exiv2 is used to modify the metadata of a crafted image file. An attacker could potentially exploit the vulnerability to cause a denial of service, if they can trick the victim into running Exiv2 on a crafted image file. Note that this bug is only triggered when deleting the IPTC data, which is a less frequently used Exiv2 operation that requires an extra command line option (`-d I rm`). The bug is fixed in version v0.27.5. |
2021-08-09 |
not yet calculated |
CVE-2021-37623
CONFIRM
MISC |
exiv2 — exiv2
|
Exiv2 is a command-line utility and C++ library for reading, writing, deleting, and modifying the metadata of image files. An infinite loop was found in Exiv2 versions v0.27.4 and earlier. The infinite loop is triggered when Exiv2 is used to modify the metadata of a crafted image file. An attacker could potentially exploit the vulnerability to cause a denial of service, if they can trick the victim into running Exiv2 on a crafted image file. Note that this bug is only triggered when deleting the IPTC data, which is a less frequently used Exiv2 operation that requires an extra command line option (`-d I rm`). The bug is fixed in version v0.27.5. |
2021-08-09 |
not yet calculated |
CVE-2021-37622
CONFIRM
MISC |
express-cart — express-cart
|
The express-cart package through 1.1.10 for Node.js allows CSRF. |
2021-08-12 |
not yet calculated |
CVE-2020-22403
MISC |
express_engine — express_engine
|
In Expression Engine before 6.0.3, addonIcon in Addons/file/mod.file.php relies on the untrusted input value of input->get(‘file’) instead of the fixed file names of icon.png and icon.svg. |
2021-08-12 |
not yet calculated |
CVE-2021-33199
MISC
MISC |
f-secure — f-secure
|
A address bar spoofing vulnerability was discovered in Safe Browser for iOS. Showing the legitimate URL in the address bar while loading the content from other domain. This makes the user believe that the content is served by a legit domain. A remote attacker can leverage this to perform address bar spoofing attack. |
2021-08-11 |
not yet calculated |
CVE-2021-33595
MISC
MISC
MISC |
fatek — automation_fvdesigner
|
FATEK Automation FvDesigner, Versions 1.5.88 and prior is vulnerable to a stack-based buffer overflow, which may allow an attacker to execute arbitrary code. |
2021-08-11 |
not yet calculated |
CVE-2021-32947
MISC |
fatek — automation_fvdesigner
|
An uninitialized pointer in FATEK Automation FvDesigner, Versions 1.5.88 and prior may be exploited while the application is processing project files, allowing an attacker to craft a special project file that may permit arbitrary code execution. |
2021-08-11 |
not yet calculated |
CVE-2021-32931
MISC |
fatek — automation_fvdesigner
|
FATEK Automation FvDesigner, Versions 1.5.88 and prior is vulnerable to an out-of-bounds write while processing project files, allowing an attacker to craft a project file that may permit arbitrary code execution. |
2021-08-11 |
not yet calculated |
CVE-2021-32939
MISC |
ffmpeg — ffmpeg
|
FFmpeg version (git commit de8e6e67e7523e48bb27ac224a0b446df05e1640) suffers from a an assertion failure at src/libavutil/mathematics.c. |
2021-08-12 |
not yet calculated |
CVE-2021-38291
MISC |
ffmpeg — ffmpeg
|
A heap-use-after-free in the av_freep function in libavutil/mem.c of FFmpeg 4.2 allows attackers to execute arbitrary code. |
2021-08-10 |
not yet calculated |
CVE-2020-21688
MISC |
ffmpeg — ffmpeg
|
A heap-use-after-free in the mpeg_mux_write_packet function in libavformat/mpegenc.c of FFmpeg 4.2 allows to cause a denial of service (DOS) via a crafted avi file. |
2021-08-10 |
not yet calculated |
CVE-2020-21697
MISC |
| fig2dev — fig2dev |
A global buffer overflow in the set_fill component in genge.c of fig2dev 3.2.7b allows attackers to cause a denial of service (DOS) via converting a xfig file into ge format. |
2021-08-10 |
not yet calculated |
CVE-2020-21682
MISC |
fig2dev — fig2dev
|
A stack-based buffer overflow in the genpstrx_text() component in genpstricks.c of fig2dev 3.2.7b allows attackers to cause a denial of service (DOS) via converting a xfig file into pstricks format. |
2021-08-10 |
not yet calculated |
CVE-2020-21676
MISC |
fig2dev — fig2dev
|
A global buffer overflow in the genmp_writefontmacro_latex component in genmp.c of fig2dev 3.2.7b allows attackers to cause a denial of service (DOS) via converting a xfig file into mp format. |
2021-08-10 |
not yet calculated |
CVE-2020-21678
MISC |
fig2dev — fig2dev
|
A stack-based buffer overflow in the put_arrow() component in genpict2e.c of fig2dev 3.2.7b allows attackers to cause a denial of service (DOS) via converting a xfig file into pict2e format. |
2021-08-10 |
not yet calculated |
CVE-2020-21680
MISC |
fig2dev — fig2dev
|
A global buffer overflow in the set_color component in genge.c of fig2dev 3.2.7b allows attackers to cause a denial of service (DOS) via converting a xfig file into ge format. |
2021-08-10 |
not yet calculated |
CVE-2020-21681
MISC |
fig2dev — fig2dev
|
A global buffer overflow in the shade_or_tint_name_after_declare_color in genpstricks.c of fig2dev 3.2.7b allows attackers to cause a denial of service (DOS) via converting a xfig file into pstricks format. |
2021-08-10 |
not yet calculated |
CVE-2020-21683
MISC |
| flygo — flygo |
The check-in record page of Flygo contains Insecure Direct Object Reference (IDOR) vulnerability. After being authenticated as a general user, remote attackers can manipulate the employee ID and date in specific parameters to access particular employee’s check-in record. |
2021-08-09 |
not yet calculated |
CVE-2021-37213
MISC |
| flygo — flygo |
The bulletin function of Flygo contains Insecure Direct Object Reference (IDOR) vulnerability. After being authenticated as a general user, remote attackers can manipulate the bulletin ID in specific Url parameters and access and modify bulletin particular content. |
2021-08-09 |
not yet calculated |
CVE-2021-37212
MISC |
| flygo — flygo |
The employee management page of Flygo contains an Insecure Direct Object Reference (IDOR) vulnerability. After being authenticated as a general user, remote attacker can manipulate the user data and then over-write another employee’s user data by specifying that employee’s ID in the API parameter. |
2021-08-09 |
not yet calculated |
CVE-2021-37215
MISC |
flygo — flygo
|
The employee management page of Flygo contains Insecure Direct Object Reference (IDOR) vulnerability. After being authenticated as a general user, remote attackers can manipulate the employee ID in specific parameters to arbitrary access employee’s data, modify it, and then obtain administrator privilege and execute arbitrary command. |
2021-08-09 |
not yet calculated |
CVE-2021-37214
MISC |
flygo — flygo
|
The bulletin function of Flygo does not filter special characters while a new announcement is added. Remoter attackers can use the vulnerability with general user’s credential to inject JavaScript and execute stored XSS attacks. |
2021-08-09 |
not yet calculated |
CVE-2021-37211
MISC |
foxit — pdf_editor
|
An issue was discovered in Foxit PDF Editor before 11.0.1 and PDF Reader before 11.0.1 on macOS. It mishandles missing dictionary entries, leading to a NULL pointer dereference, aka CNVD-C-2021-95204. |
2021-08-11 |
not yet calculated |
CVE-2021-38567
MISC |
foxit — pdf_editor
|
An issue was discovered in Foxit PDF Reader before 11.0.1 and PDF Editor before 11.0.1. It allows an out-of-bounds read via util.scand. |
2021-08-11 |
not yet calculated |
CVE-2021-38564
MISC |
foxit — pdf_editor
|
An issue was discovered in Foxit PDF Reader before 11.0.1 and PDF Editor before 11.0.1. It mishandles situations in which an array size (derived from a /Size entry) is smaller than the maximum indirect object number, and thus there is an attempted incorrect array access (leading to a NULL pointer dereference, or out-of-bounds read or write). |
2021-08-11 |
not yet calculated |
CVE-2021-38563
MISC |
foxit — pdf_editor
|
An issue was discovered in Foxit PDF Reader before 11.0.1 and PDF Editor before 11.0.1. It allows writing to arbitrary files via submitForm. |
2021-08-11 |
not yet calculated |
CVE-2021-38565
MISC |
foxit — pdf_editor
|
An issue was discovered in Foxit PDF Reader before 11.0.1 and PDF Editor before 11.0.1. It allows stack consumption during recursive processing of embedded XML nodes. |
2021-08-11 |
not yet calculated |
CVE-2021-38566
MISC |
fuel — cms
|
A host header attack vulnerability exists in FUEL CMS 1.5.0 through fuel/modules/fuel/config/fuel_constants.php and fuel/modules/fuel/libraries/Asset.php. An attacker can use a man in the middle attack such as phishing. |
2021-08-09 |
not yet calculated |
CVE-2021-38290
MISC
MISC |
genpict2e — genpict2e
|
A global buffer overflow in the put_font in genpict2e.c of fig2dev 3.2.7b allows attackers to cause a denial of service (DOS) via converting a xfig file into pict2e format. |
2021-08-10 |
not yet calculated |
CVE-2020-21684
MISC |
getsimple — getsimple
|
A cross-site request forgery (CSRF) vulnerability in the My SMTP Contact v1.1.1 plugin for GetSimple CMS allows remote attackers to change the SMTP settings of the contact forms for the webpages of the CMS after an authenticated admin visits a malicious third-party site. |
2021-08-10 |
not yet calculated |
CVE-2021-29400
MISC |
getsimplecms — getsimplecms
|
GetSimpleCMS 3.3.16 contains a cross-site Scripting (XSS) vulnerability, where Function TSL does not filter check settings.php Website URL: “siteURL” parameter. |
2021-08-10 |
not yet calculated |
CVE-2021-36601
MISC |
github — github
|
@github/paste-markdown is an npm package for pasting markdown objects. A self Cross-Site Scripting vulnerability exists in the @github/paste-markdown before version 0.3.4. If the clipboard data contains the string `<table>`, a **div** is dynamically created, and the clipboard content is copied into its **innerHTML** property without any sanitization, resulting in improper execution of JavaScript in the browser of the victim (the user who pasted the code). Users directed to copy text from a malicious website and paste it into pages that utilize this library are affected. This is fixed in version 0.3.4. Refer the to the referenced GitHub Advisory for more details including an example exploit. |
2021-08-12 |
not yet calculated |
CVE-2021-37700
MISC
MISC
CONFIRM
MISC |
gnu — cpio
|
GNU cpio through 2.13 allows attackers to execute arbitrary code via a crafted pattern file, because of a dstring.c ds_fgetstr integer overflow that triggers an out-of-bounds heap write. NOTE: it is unclear whether there are common cases where the pattern file, associated with the -E option, is untrusted data. |
2021-08-08 |
not yet calculated |
CVE-2021-38185
MISC
MISC
MISC
MISC |
go — go
|
Go before 1.15.15 and 1.16.x before 1.16.7 has a race condition that can lead to a net/http/httputil ReverseProxy panic upon an ErrAbortHandler abort. |
2021-08-08 |
not yet calculated |
CVE-2021-36221
MISC
MISC
MISC |
go — go
|
Go before 1.17 does not properly consider extraneous zero characters at the beginning of an IP address octet, which (in some situations) allows attackers to bypass access control that is based on IP addresses, because of unexpected octal interpretation. This affects net.ParseIP and net.ParseCIDR. |
2021-08-07 |
not yet calculated |
CVE-2021-29923
MISC
MISC
MISC
MISC
MISC
MISC |
go-unarr — go-unarr
|
unarr.go in go-unarr (aka Go bindings for unarr) 0.1.1 allows Directory Traversal via ../ in a pathname within a TAR archive. |
2021-08-08 |
not yet calculated |
CVE-2021-38197
MISC |
google — android
|
An issue was discovered on LG mobile devices with Android OS P and Q software for mt6762/mt6765/mt6883. Attackers can change some of the NvRAM content by leveraging the misconfiguration of a debug command. The LG ID is LVE-SMP-210005 (August 2021). |
2021-08-12 |
not yet calculated |
CVE-2021-38591
MISC |
google — android
|
An address bar spoofing vulnerability was discovered in Safe Browser for Android. When user clicks on a specially crafted a malicious URL, it appears like a legitimate one on the address bar, while the content comes from other domain and presented in a window, covering the original content. A remote attacker can leverage this to perform address bar spoofing attack. |
2021-08-11 |
not yet calculated |
CVE-2021-33594
MISC
MISC
MISC |
google — android
|
Task Hijacking is a vulnerability that affects the applications running on Android devices due to a misconfiguration in their AndroidManifest.xml with their Task Control features. This allows an unauthorized attacker or malware to takeover legitimate apps and to steal user’s sensitive information. |
2021-08-10 |
not yet calculated |
CVE-2021-33699
MISC
MISC |
gpac — gpac
|
The gf_hinter_finalize function in GPAC 1.0.1 allows attackers to cause a denial of service (NULL pointer dereference) via a crafted file in the MP4Box command. |
2021-08-11 |
not yet calculated |
CVE-2021-32437
MISC
MISC |
gpac — gpac
|
The gf_media_export_filters function in GPAC 1.0.1 allows attackers to cause a denial of service (NULL pointer dereference) via a crafted file in the MP4Box command. |
2021-08-11 |
not yet calculated |
CVE-2021-32438
MISC
MISC |
gurock — testrail
|
A vulnerability in the web UI of Gurock TestRail v5.3.0.3603 could allow an unauthenticated, remote attacker to affect the integrity of a device via a clickjacking attack. The vulnerability is due to insufficient input validation of iFrame data in HTTP requests that are sent to an affected device. An attacker could exploit this vulnerability by sending crafted HTTP packets with malicious iFrame data. A successful exploit could allow the attacker to perform a clickjacking attack where the user is tricked into clicking a malicious link. |
2021-08-09 |
not yet calculated |
CVE-2021-37788
MISC |
gxlcms — gxlcms
|
In libadminactiondataaction.class.php in Gxlcms v1.1, SQL Injection exists via the $filename parameter. |
2021-08-12 |
not yet calculated |
CVE-2020-20975
MISC |
hashicorp — vault_and_vault_enterprise
|
HashiCorp Vault and Vault Enterprise 1.4.0 through 1.7.3 initialized an underlying database file associated with the Integrated Storage feature with excessively broad filesystem permissions. Fixed in Vault and Vault Enterprise 1.8.0. |
2021-08-13 |
not yet calculated |
CVE-2021-38553
MISC |
hashicorp — vault_and_vault_enterprises
|
HashiCorp Vault and Vault Enterprise’s UI erroneously cached and exposed user-viewed secrets between sessions in a single shared browser. Fixed in 1.8.0 and pending 1.7.4 / 1.6.6 releases. |
2021-08-13 |
not yet calculated |
CVE-2021-38554
MISC |
hcl — commerce_management_center
|
” Security vulnerability in HCL Commerce Management Center allowing XML external entity (XXE) injection” |
2021-08-13 |
not yet calculated |
CVE-2021-27741
MISC |
helpsystems — cobalt_strike
|
A Denial-of-Service (DoS) vulnerability was discovered in Team Server in HelpSystems Cobalt Strike 4.2 and 4.3. It allows remote attackers to crash the C2 server thread and block beacons’ communication with it. |
2021-08-09 |
not yet calculated |
CVE-2021-36798
MISC
MISC |
huawei — hg8045q
|
There is a command injection vulnerability in the HG8045Q product. When the command-line interface is enabled, which is disabled by default, attackers with administrator privilege could execute part of commands. |
2021-08-13 |
not yet calculated |
CVE-2021-37028
MISC |
huawei — smartphones
|
A component of the Huawei smartphone has a Double Free vulnerability. Local attackers may exploit this vulnerability to cause Root Elevation of Privileges. |
2021-08-10 |
not yet calculated |
CVE-2021-22386
MISC
MISC |
huawei — smartphones
|
A component of the Huawei smartphone has a External Control of System or Configuration Setting vulnerability. Local attackers may exploit this vulnerability to cause Kernel Code Execution. |
2021-08-10 |
not yet calculated |
CVE-2021-22385
MISC
MISC |
ibm — content_navigator
|
IBM Content Navigator 3.0.CD could allow a malicious user to cause a denial of service due to improper input validation. IBM X-Force ID: 200968. |
2021-08-09 |
not yet calculated |
CVE-2021-29714
CONFIRM
XF |
ibm — maximo_asset_management
|
IBM Maximo Asset Management 7.6.0 and 7.6.1 is potentially vulnerable to CSV Injection. A remote attacker could execute arbitrary commands on the system, caused by improper validation of csv file contents. IBM X-Force ID: 198243. |
2021-08-12 |
not yet calculated |
CVE-2021-20509
XF
CONFIRM |
ibm — planning_analytics_local
|
IBM Planning Analytics Local 2.0 could allow a remote attacker to obtain sensitive information when a stack trace is returned in the browser. X-Force ID: 198846. |
2021-08-10 |
not yet calculated |
CVE-2021-29739
CONFIRM
XF |
ibm — qradar_siem
|
IBM QRadar SIEM 7.4.3 GA – 7.4.3 Fix Pack 1 when using domains or multi-tenancy could be vulnerable to information disclosure between tenants by routing SIEM data to the incorrect domain. IBM X-Force ID: 206979. |
2021-08-13 |
not yet calculated |
CVE-2021-29880
CONFIRM
XF |
ibm — security_guardium
|
IBM Security Guardium 11.2 uses an inadequate account lockout setting that could allow a remote attacker to brute force account credentials. IBM X-Force ID: 196314. |
2021-08-11 |
not yet calculated |
CVE-2021-20427
XF
CONFIRM |
ibm — security_guardium
|
IBM Security Guardium 11.2 could disclose sensitive information due to reliance on untrusted inputs that could aid in further attacks against the system. IBM X-Force ID: 196281. |
2021-08-11 |
not yet calculated |
CVE-2021-20420
XF
CONFIRM |
ibm — security_guardium
|
IBM Security Guardium 11.2 does not require that users should have strong passwords by default, which makes it easier for attackers to compromise user accounts. IBM X-Force ID: 196279. |
2021-08-11 |
not yet calculated |
CVE-2021-20418
CONFIRM
XF |
ibm — tivoli_workload_scheduler
|
IBM Tivoli Workload Scheduler 9.4 and 9.5 is vulnerable to a stack-based buffer overflow, caused by improper bounds checking. A local attacker could overflow a buffer and gain lower level privileges. IBM X-Force ID: 194599. |
2021-08-09 |
not yet calculated |
CVE-2021-20349
CONFIRM
XF |
infrabox — infrabox
|
Due to improper input validation in InfraBox, logs can be modified by an authenticated user. |
2021-08-10 |
not yet calculated |
CVE-2021-33706
MISC |
intel — ethernet_adapters_800_series_controller
|
Uncontrolled resource consumption in firmware for Intel(R) Ethernet Adapters 800 Series Controllers and associated adapters before version 1.5.3.0 may allow privileged user to potentially enable denial of service via local access. |
2021-08-11 |
not yet calculated |
CVE-2021-0008
MISC |
| intel — ethernet_adapters_800_series_controllers |
Out-of-bounds read in the firmware for Intel(R) Ethernet Adapters 800 Series Controllers and associated adapters before version 1.5.3.0 may allow an unauthenticated user to potentially enable denial of service via adjacent access. |
2021-08-11 |
not yet calculated |
CVE-2021-0009
MISC |
| intel — ethernet_adapters_800_series_controllers |
Uncaught exception in firmware for Intel(R) Ethernet Adapters 800 Series Controllers and associated adapters before version 1.5.3.0 may allow a privileged user to potentially enable denial of service via local access. |
2021-08-11 |
not yet calculated |
CVE-2021-0005
MISC |
intel — ethernet_adapters_800_series_controllers
|
Improper conditions check in some Intel(R) Ethernet Controllers 800 series Linux drivers before version 1.4.11 may allow an authenticated user to potentially enable information disclosure or denial of service via local access. |
2021-08-11 |
not yet calculated |
CVE-2021-0002
MISC |
intel — ethernet_adapters_800_series_controllers
|
Uncaught exception in firmware for Intel(R) Ethernet Adapters 800 Series Controllers and associated adapters before version 1.5.1.0 may allow a privileged attacker to potentially enable denial of service via local access. |
2021-08-11 |
not yet calculated |
CVE-2021-0007
MISC |
intel — ethernet_adapters_800_series_controllers
|
Improper conditions check in some Intel(R) Ethernet Controllers 800 series Linux drivers before version 1.4.11 may allow an authenticated user to potentially enable information disclosure via local access. |
2021-08-11 |
not yet calculated |
CVE-2021-0003
MISC |
intel — ethernet_adapters_800_series_controllers
|
Improper conditions check in firmware for Intel(R) Ethernet Adapters 800 Series Controllers and associated adapters before version 1.5.4.0 may allow a privileged user to potentially enable denial of service via local access. |
2021-08-11 |
not yet calculated |
CVE-2021-0006
MISC |
intel — ethernet_adapters_800_series_controllers
|
Improper buffer restrictions in the firmware of Intel(R) Ethernet Adapters 800 Series Controllers and associated adapters before version 1.5.3.0 may allow a privileged user to potentially enable denial of service via local access. |
2021-08-11 |
not yet calculated |
CVE-2021-0004
MISC |
intel — ethernet_controllers_x722_and_800_series
|
Improper input validation in the Intel(R) Ethernet Controllers X722 and 800 series Linux RMDA driver before version 1.3.19 may allow an authenticated user to potentially enable escalation of privilege via local access. |
2021-08-11 |
not yet calculated |
CVE-2021-0084
MISC |
intel — graphics_drivers
|
Use after free in some Intel(R) Graphics Driver before version 27.20.100.8336, 15.45.33.5164, and 15.40.47.5166 may allow an authenticated user to potentially enable denial of service via local access. |
2021-08-11 |
not yet calculated |
CVE-2021-0012
MISC |
intel — graphics_drivers
|
Improper input validation in some Intel(R) Graphics Drivers before version 27.20.100.8935 may allow an authenticated user to potentially enable escalation of privilege via local access. |
2021-08-11 |
not yet calculated |
CVE-2021-0062
MISC |
intel — graphics_drivers
|
Improper initialization in some Intel(R) Graphics Driver before version 27.20.100.9030 may allow an authenticated user to potentially enable escalation of privilege via local access. |
2021-08-11 |
not yet calculated |
CVE-2021-0061
MISC |
intel — nuc9_extreme_laptop_kits
|
Improper access control in kernel mode driver for some Intel(R) NUC 9 Extreme Laptop Kits before version 2.2.0.20 may allow an authenticated user to potentially enable escalation of privilege via local access. |
2021-08-11 |
not yet calculated |
CVE-2021-0196
MISC |
intel — nuc_pro_chassis_element_acermedia_capture_card
|
Uncontrolled search path in some Intel(R) NUC Pro Chassis Element AverMedia Capture Card drivers before version 3.0.64.143 may allow an authenticated user to potentially enable escalation of privilege via local access. |
2021-08-11 |
not yet calculated |
CVE-2021-0160
MISC |
intel — optane_pmem
|
Improper input validation in some Intel(R) Optane(TM) PMem versions before versions 1.2.0.5446 or 2.2.0.1547 may allow a privileged user to potentially enable denial of service via local access. |
2021-08-11 |
not yet calculated |
CVE-2021-0083
MISC |
j2eefast — j2eefast
|
J2eeFAST 2.2.1 allows remote attackers to perform SQL injection via the (1) compId parameter to fast/sys/user/list, (2) deptId parameter to fast/sys/role/list, or (3) roleId parameter to fast/sys/role/authUser/list, related to the use of ${} to join SQL statements. |
2021-08-12 |
not yet calculated |
CVE-2021-28890
MISC |
jbl — go_2_devices
|
JBL Go 2 devices through 2021-08-09 allow remote attackers to recover speech signals from an LED on the device, via a telescope and an electro-optical sensor, aka a “Glowworm” attack. The power indicator LED of the speakers is connected directly to the power line, as a result, the intensity of a device’s power indicator LED is correlative to the power consumption. The sound played by the speakers affects their power consumption and as a result is also correlative to the light intensity of the LEDs. By analyzing measurements obtained from an electro-optical sensor directed at the power indicator LEDs of the speakers, we can recover the sound played by them. |
2021-08-11 |
not yet calculated |
CVE-2021-38548
MISC |
jt2go — jt2go
|
A vulnerability has been identified in JT2Go (All versions < V13.2.0.1), Teamcenter Visualization (All versions < V13.2.0.1). When parsing specially crafted CGM Files, a NULL pointer deference condition could cause the application to crash. The application must be restarted to restore the service. An attacker could leverage this vulnerability to cause a Denial-of-Service condition in the application. |
2021-08-10 |
not yet calculated |
CVE-2021-33717
MISC |
jt2go — jt2go
|
A vulnerability has been identified in JT2Go (All versions < V13.2.0.2), Teamcenter Visualization (All versions < V13.2.0.2). The plmxmlAdapterSE70.dll library in affected applications lacks proper validation of user-supplied data when parsing PAR files. This could result in an out of bounds read past the end of an allocated buffer. An attacker could leverage this vulnerability to leak information in the context of the current process. (ZDI-CAN-13405) |
2021-08-10 |
not yet calculated |
CVE-2021-33738
MISC |
jupyter — jupyterlab
|
JupyterLab is a user interface for Project Jupyter which will eventually replace the classic Jupyter Notebook. In affected versions untrusted notebook can execute code on load. In particular JupyterLab doesn’t sanitize the action attribute of html `<form>`. Using this it is possible to trigger the form validation outside of the form itself. This is a remote code execution, but requires user action to open a notebook. |
2021-08-09 |
not yet calculated |
CVE-2021-32797
MISC
CONFIRM |
jupyter — notebook
|
The Jupyter notebook is a web-based notebook environment for interactive computing. In affected versions untrusted notebook can execute code on load. Jupyter Notebook uses a deprecated version of Google Caja to sanitize user inputs. A public Caja bypass can be used to trigger an XSS when a victim opens a malicious ipynb document in Jupyter Notebook. The XSS allows an attacker to execute arbitrary code on the victim computer using Jupyter APIs. |
2021-08-09 |
not yet calculated |
CVE-2021-32798
CONFIRM
MISC |
kde — kmail
|
In KDE KMail 19.12.3 (aka 5.13.3), the SMTP STARTTLS option is not honored (and cleartext messages are sent) unless “Server requires authentication” is checked. |
2021-08-10 |
not yet calculated |
CVE-2021-38373
MISC
MISC |
kde — trojita
|
In KDE Trojita 0.7, man-in-the-middle attackers can create new folders because untagged responses from an IMAP server are accepted before STARTTLS. |
2021-08-10 |
not yet calculated |
CVE-2021-38372
MISC
MISC |
kitecms — kitecms
|
A directory traversal issue in KiteCMS 1.1.1 allows remote administrators to overwrite arbitrary files via ../ in the path parameter to index.php/admin/Template/fileedit, with PHP code in the html parameter. |
2021-08-12 |
not yet calculated |
CVE-2021-31731
MISC |
kuba — kuba
|
A vulnerability in all versions of Kuba allows attackers to overwrite arbitrary files in arbitrary directories with crafted Zip files due to improper validation of file paths in .zip archives. |
2021-08-10 |
not yet calculated |
CVE-2020-23172
MISC |
kyma — kyma
|
Due to insufficient input validation in Kyma, authenticated users can pass a Header of their choice and escalate privileges. |
2021-08-10 |
not yet calculated |
CVE-2021-33708
MISC |
leafkit — leafkit
|
Leafkit is a templating language with Swift-inspired syntax. Versions prior to 1.3.0 are susceptible to Cross-site Scripting (XSS) attacks. This affects anyone passing unsanitised data to Leaf’s variable tags. Before this fix, Leaf would not escape any strings passed to tags as variables. If an attacker managed to find a variable that was rendered with their unsanitised data, they could inject scripts into a generated Leaf page, which could enable XSS attacks if other mitigations such as a Content Security Policy were not enabled. This has been patched in 1.3.0. As a workaround sanitize any untrusted input before passing it to Leaf and enable a CSP to block inline script and CSS data. |
2021-08-09 |
not yet calculated |
CVE-2021-37634
MISC
CONFIRM |
librt — gnu_c_library
|
In librt in the GNU C Library (aka glibc) through 2.34, sysdeps/unix/sysv/linux/mq_notify.c mishandles certain NOTIFY_REMOVED data, leading to a NULL pointer dereference. NOTE: this vulnerability was introduced as a side effect of the CVE-2021-33574 fix. |
2021-08-12 |
not yet calculated |
CVE-2021-38604
MISC
MISC
MISC |
libsixel — libsixel
|
A heap-based buffer overflow in the sixel_encoder_output_without_macro function in encoder.c of Libsixel 1.8.4 allows attackers to cause a denial of service (DOS) via converting a crafted PNG file into Sixel format. |
2021-08-10 |
not yet calculated |
CVE-2020-21677
MISC |
libspf2 — libspf2
|
Stack buffer overflow in libspf2 versions below 1.2.11 when processing certain SPF macros can lead to Denial of service and potentially code execution via malicious crafted SPF explanation messages. |
2021-08-12 |
not yet calculated |
CVE-2021-20314
MISC |
linaro — op-tee
|
In Linaro OP-TEE before 3.7.0, by using inconsistent or malformed data, it is possible to call update and final cryptographic functions directly, causing a crash that could leak sensitive information. |
2021-08-11 |
not yet calculated |
CVE-2019-25052
MISC
MISC |
| linux — linux_kernel |
NVIDIA Linux kernel distributions contain a vulnerability in nvmap, where a null pointer dereference may lead to complete denial of service. |
2021-08-11 |
not yet calculated |
CVE-2021-1112
MISC |
| linux — linux_kernel |
A flaw was found in the Linux kernel netfilter implementation in versions prior to 5.5-rc7. A user with root (CAP_SYS_ADMIN) access is able to panic the system when issuing netfilter netflow commands. |
2021-08-13 |
not yet calculated |
CVE-2021-3635
MISC |
| linux — linux_kernel |
NVIDIA Linux kernel distributions contain a vulnerability in nvmap NVMAP_IOC_WRITE* paths, where improper access controls may lead to code execution, complete denial of service, and seriously compromised integrity of all system components. |
2021-08-11 |
not yet calculated |
CVE-2021-1107
MISC |
| linux — linux_kernel |
NVIDIA Linux kernel distributions on Jetson Xavier contain a vulnerability in camera firmware where a user can change input data after validation, which may lead to complete denial of service and serious data corruption of all kernel components. |
2021-08-11 |
not yet calculated |
CVE-2021-1110
MISC |
| linux — linux_kernel |
NVIDIA Linux kernel distributions contain a vulnerability in the kernel crypto node, where use after free may lead to complete denial of service. |
2021-08-11 |
not yet calculated |
CVE-2021-1114
MISC |
linux — linux_kernel
|
A use-after-free in function hci_sock_bound_ioctl() of the Linux kernel HCI subsystem was found in the way user calls ioct HCIUNBLOCKADDR or other way triggers race condition of the call hci_unregister_dev() together with one of the calls hci_sock_blacklist_add(), hci_sock_blacklist_del(), hci_get_conn_info(), hci_get_auth_info(). A privileged local user could use this flaw to crash the system or escalate their privileges on the system. This flaw affects the Linux kernel versions prior to 5.13-rc5. |
2021-08-13 |
not yet calculated |
CVE-2021-3573
MISC
MISC
MISC |
linux — linux_kernel
|
NVIDIA Linux kernel distributions contain a vulnerability in nvmap, where writes may be allowed to read-only buffers, which may result in escalation of privileges, complete denial of service, unconstrained information disclosure, and serious data tampering of all processes on the system. |
2021-08-11 |
not yet calculated |
CVE-2021-1106
MISC |
linux — linux_kernel
|
NVIDIA Linux kernel distributions contain a vulnerability in FuSa Capture (VI/ISP), where integer underflow due to lack of input validation may lead to complete denial of service, partial integrity, and serious confidentiality loss for all processes in the system. |
2021-08-11 |
not yet calculated |
CVE-2021-1108
MISC |
| live555 — live555 |
Live555 through 1.08 mishandles huge requests for the same MP3 stream, leading to recursion and s stack-based buffer over-read. An attacker can leverage this to launch a DoS attack. |
2021-08-10 |
not yet calculated |
CVE-2021-38380
MISC
MISC |
live555 — live555
|
Live555 through 1.08 does not handle MPEG-1 or 2 files properly. Sending two successive RTSP SETUP commands for the same track causes a Use-After-Free and daemon crash. |
2021-08-10 |
not yet calculated |
CVE-2021-38381
MISC
MISC |
live555 — live555
|
Live555 through 1.08 does not handle Matroska and Ogg files properly. Sending two successive RTSP SETUP commands for the same track causes a Use-After-Free and daemon crash. |
2021-08-10 |
not yet calculated |
CVE-2021-38382
MISC
MISC |
ljcms — ljcms
|
An arbitrary file upload vulnerability in the move_uploaded_file() function of LJCMS v4.3 allows attackers to execute arbitrary code. |
2021-08-12 |
not yet calculated |
CVE-2020-20979
MISC |
logitech — z120_and_s120_speakers
|
Logitech Z120 and S120 speakers through 2021-08-09 allow remote attackers to recover speech signals from an LED on the device, via a telescope and an electro-optical sensor, aka a “Glowworm” attack. The power indicator LED of the speakers is connected directly to the power line, as a result, the intensity of a device’s power indicator LED is correlative to the power consumption. The sound played by the speakers affects their power consumption and as a result is also correlative to the light intensity of the LEDs. By analyzing measurements obtained from an electro-optical sensor directed at the power indicator LEDs of the speakers, we can recover the sound played by them. |
2021-08-11 |
not yet calculated |
CVE-2021-38547
MISC |
maccms10 — maccms10
|
An arbitrary file upload vulnerability in the Template Upload function of Maccms10 allows attackers bypass the suffix whitelist verification to execute arbitrary code via adding a character to the end of the uploaded file’s name. |
2021-08-11 |
not yet calculated |
CVE-2020-21359
MISC |
maccms10 — maccms10
|
An arbitrary file deletion vulnerability exists within Maccms10. |
2021-08-11 |
not yet calculated |
CVE-2020-21363
MISC |
manageengine — adselfservice_plus
|
A CSV injection vulnerability on the login panel of ManageEngine ADSelfService Plus Version: 6.1 Build No: 6101 can be exploited by an unauthenticated user. The j_username parameter seems to be vulnerable and a reverse shell could be obtained if a privileged user exports “User Attempts Audit Report” as CSV file. |
2021-08-09 |
not yet calculated |
CVE-2021-33256
MISC |
mediawiki — mediawiki
|
An issue was discovered in the Oauth extension for MediaWiki through 1.35.2. MWOAuthConsumerSubmitControl.php does not ensure that the length of an RSA key will fit in a MySQL blob. |
2021-08-12 |
not yet calculated |
CVE-2021-31556
MISC
MISC |
merge-change — merge-change
|
All versions of package merge-change are vulnerable to Prototype Pollution via the utils.set function. |
2021-08-11 |
not yet calculated |
CVE-2021-23421
MISC
MISC |
metinfo — metinfo
|
A SQL injection in the /admin/?n=logs&c=index&a=dolist component of Metinfo 7.0 allows attackers to access sensitive database information. |
2021-08-12 |
not yet calculated |
CVE-2020-20981
MISC |
| microsoft — azure |
Azure Sphere Information Disclosure Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-26428
N/A |
| microsoft — azure |
Azure CycleCloud Elevation of Privilege Vulnerability This CVE ID is unique from CVE-2021-33762. |
2021-08-12 |
not yet calculated |
CVE-2021-36943
N/A |
microsoft — azure
|
Microsoft Azure Active Directory Connect Authentication Bypass Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-36949
N/A |
microsoft — azure
|
Azure Sphere Elevation of Privilege Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-26429
N/A |
microsoft — azure
|
Azure Sphere Denial of Service Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-26430
N/A |
microsoft — dynamics_365
|
Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-36950
N/A |
microsoft — dynamics_365
|
Microsoft Dynamics Business Central Cross-site Scripting Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-36946
N/A |
microsoft — dynamics_365
|
Microsoft Dynamics 365 (on-premises) Remote Code Execution Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-34524
N/A |
microsoft — office
|
Microsoft Office Remote Code Execution Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-34478
N/A |
microsoft — sharepoint
|
Microsoft SharePoint Server Spoofing Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-36940
N/A |
microsoft — visual_studio
|
ASP.NET Core and Visual Studio Information Disclosure Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-34532
N/A |
microsoft — visual_studio
|
.NET Core and Visual Studio Denial of Service Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-26423
N/A |
microsoft — visual_studio
|
.NET Core and Visual Studio Information Disclosure Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-34485
N/A |
| microsoft — windows |
Windows Services for NFS ONCRPC XDR Driver Information Disclosure Vulnerability This CVE ID is unique from CVE-2021-26433, CVE-2021-36932, CVE-2021-36933. |
2021-08-12 |
not yet calculated |
CVE-2021-36926
N/A |
| microsoft — windows |
Windows MSHTML Platform Remote Code Execution Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-34534
N/A |
| microsoft — windows |
Windows Update Medic Service Elevation of Privilege Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-36948
N/A |
| microsoft — windows |
Windows 10 Update Assistant Elevation of Privilege Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-36945
N/A |
| microsoft — windows |
Windows Media MPEG-4 Video Decoder Remote Code Execution Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-36937
N/A |
microsoft — windows
|
Windows Digital TV Tuner device registration application Elevation of Privilege Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-36927
N/A |
microsoft — windows
|
Windows Print Spooler Remote Code Execution Vulnerability This CVE ID is unique from CVE-2021-36947, CVE-2021-36958. |
2021-08-12 |
not yet calculated |
CVE-2021-36936
N/A |
microsoft — windows
|
Scripting Engine Memory Corruption Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-34480
N/A |
microsoft — windows
|
Windows Services for NFS ONCRPC XDR Driver Information Disclosure Vulnerability This CVE ID is unique from CVE-2021-26433, CVE-2021-36926, CVE-2021-36933. |
2021-08-12 |
not yet calculated |
CVE-2021-36932
N/A |
microsoft — windows
|
Windows Services for NFS ONCRPC XDR Driver Information Disclosure Vulnerability This CVE ID is unique from CVE-2021-26433, CVE-2021-36926, CVE-2021-36932. |
2021-08-12 |
not yet calculated |
CVE-2021-36933
N/A |
microsoft — windows
|
Windows Print Spooler Remote Code Execution Vulnerability This CVE ID is unique from CVE-2021-36936, CVE-2021-36947. |
2021-08-12 |
not yet calculated |
CVE-2021-36958
N/A |
microsoft — windows
|
Windows Cryptographic Primitives Library Information Disclosure Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-36938
N/A |
microsoft — windows
|
Windows TCP/IP Remote Code Execution Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-26424
N/A |
microsoft — windows
|
Windows LSA Spoofing Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-36942
N/A |
microsoft — windows
|
Windows Print Spooler Remote Code Execution Vulnerability This CVE ID is unique from CVE-2021-36936, CVE-2021-36958. |
2021-08-12 |
not yet calculated |
CVE-2021-36947
N/A |
microsoft — windows
|
Microsoft Windows Defender Elevation of Privilege Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-34471
N/A |
microsoft — windows
|
Windows Event Tracing Elevation of Privilege Vulnerability This CVE ID is unique from CVE-2021-34486, CVE-2021-34487. |
2021-08-12 |
not yet calculated |
CVE-2021-26425
N/A |
microsoft — windows
|
Windows Graphics Component Font Parsing Remote Code Execution Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-34533
N/A |
microsoft — windows
|
Windows Graphics Component Remote Code Execution Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-34530
N/A |
microsoft — windows
|
Windows User Profile Service Elevation of Privilege Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-34484
N/A |
microsoft — windows
|
Windows Event Tracing Elevation of Privilege Vulnerability This CVE ID is unique from CVE-2021-26425, CVE-2021-34487. |
2021-08-12 |
not yet calculated |
CVE-2021-34486
N/A |
microsoft — windows
|
Windows Event Tracing Elevation of Privilege Vulnerability This CVE ID is unique from CVE-2021-26425, CVE-2021-34486. |
2021-08-12 |
not yet calculated |
CVE-2021-34487
N/A |
microsoft — windows
|
Windows User Account Profile Picture Elevation of Privilege Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-26426
N/A |
microsoft — windows
|
Windows Print Spooler Elevation of Privilege Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-34483
N/A |
microsoft — windows
|
Storage Spaces Controller Elevation of Privilege Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-34536
N/A |
microsoft — windows
|
Remote Desktop Client Remote Code Execution Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-34535
N/A |
microsoft — windows
|
Windows Bluetooth Driver Elevation of Privilege Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-34537
N/A |
microsoft — windows
|
Windows Services for NFS ONCRPC XDR Driver Information Disclosure Vulnerability This CVE ID is unique from CVE-2021-36926, CVE-2021-36932, CVE-2021-36933. |
2021-08-12 |
not yet calculated |
CVE-2021-26433
N/A |
microsoft — windows
|
Windows Services for NFS ONCRPC XDR Driver Remote Code Execution Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-26432
N/A |
microsoft — windows
|
Windows Recovery Environment Agent Elevation of Privilege Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-26431
N/A |
microsoft — word
|
Microsoft Word Remote Code Execution Vulnerability |
2021-08-12 |
not yet calculated |
CVE-2021-36941
N/A |
miracase — mhub500
|
MIRACASE MHUB500 USB splitters through 2021-08-09, in certain specific use cases in which the device supplies power to audio-output equipment, allow remote attackers to recover speech signals from an LED on the device, via a telescope and an electro-optical sensor, aka a “Glowworm” attack. We assume that the USB splitter supplies power to some speakers. The power indicator LED of the USB splitter is connected directly to the power line, as a result, the intensity of the USB splitter’s power indicator LED is correlative to its power consumption. The sound played by the connected speakers affects the USB splitter’s power consumption and as a result is also correlative to the light intensity of the LED. By analyzing measurements obtained from an electro-optical sensor directed at the power indicator LED of the USB splitter, we can recover the sound played by the connected speakers. |
2021-08-11 |
not yet calculated |
CVE-2021-38549
MISC |
mitel — interaction_recording_multitenancy
|
The PowerPlay Web component of Mitel Interaction Recording Multitenancy systems before 6.7 could allow a user (with Administrator rights) to replay a previously recorded conversation of another tenant due to insufficient validation. |
2021-08-13 |
not yet calculated |
CVE-2021-37586
MISC
MISC |
mitel — micollab_client_service
|
The MiCollab Client Service component in Mitel MiCollab before 9.3 could allow an attacker to get source code information (disclosing sensitive application data) due to insufficient output sanitization. A successful exploit could allow an attacker to view source code methods. |
2021-08-13 |
not yet calculated |
CVE-2021-32072
MISC
MISC |
mitel — micollab_client_service
|
The MiCollab Client service in Mitel MiCollab before 9.3 could allow an unauthenticated user to gain system access due to improper access control. A successful exploit could allow an attacker to view and modify application data, and cause a denial of service for users. |
2021-08-13 |
not yet calculated |
CVE-2021-32071
MISC
MISC |
mitel — micollab_client_service
|
The MiCollab Client Service component in Mitel MiCollab before 9.3 could allow an attacker to perform a clickjacking attack due to an insecure header response. A successful exploit could allow an attacker to modify the browser header and redirect users. |
2021-08-13 |
not yet calculated |
CVE-2021-32070
MISC
MISC |
mitel — micollab_client_service
|
The AWV component of Mitel MiCollab before 9.3 could allow an attacker to perform a Man-In-the-Middle attack due to improper TLS negotiation. A successful exploit could allow an attacker to view and modify data. |
2021-08-13 |
not yet calculated |
CVE-2021-32069
MISC
MISC |
mitel — micollab_client_service
|
The AWV and MiCollab Client Service components in Mitel MiCollab before 9.3 could allow an attacker to perform a Man-In-the-Middle attack by sending multiple session renegotiation requests, due to insufficient TLS session controls. A successful exploit could allow an attacker to modify application data and state. |
2021-08-13 |
not yet calculated |
CVE-2021-32068
MISC
MISC |
mitel — micollab_client_service
|
The MiCollab Client Service component in Mitel MiCollab before 9.3 could allow an attacker to view sensitive system information through an HTTP response due to insufficient output sanitization. |
2021-08-13 |
not yet calculated |
CVE-2021-32067
MISC
MISC |
mitel — micollab_web_client
|
The Join Meeting page of Mitel MiCollab Web Client before 9.2 FP2 could allow an attacker to access (view and modify) user data by executing arbitrary code due to insufficient input validation, aka Cross-Site Scripting (XSS). |
2021-08-13 |
not yet calculated |
CVE-2021-27401
MISC
CONFIRM |
mitel — micontact_center_business
|
The Software Development Kit in Mitel MiContact Center Business from 8.0.0.0 through 8.1.4.1 and 9.0.0.0 through 9.3.1.0 could allow an unauthenticated attacker to access (view and modify) user data without authorization due to improper handling of tokens. |
2021-08-13 |
not yet calculated |
CVE-2021-3352
MISC
MISC |
| mp4box — mp4box |
Buffer overflow in the stbl_AppendSize function in MP4Box in GPAC 1.0.1 allows attackers to cause a denial of service or execute arbitrary code via a crafted file. |
2021-08-11 |
not yet calculated |
CVE-2021-32439
MISC
MISC |
mp4box — mp4box
|
The Media_RewriteODFrame function in GPAC 1.0.1 allows attackers to cause a denial of service (NULL pointer dereference) via a crafted file in the MP4Box command. |
2021-08-11 |
not yet calculated |
CVE-2021-32440
MISC
MISC |
nagios — xi_docker_wizard
|
Nagios XI before version 5.8.5 is vulnerable to insecure permissions and allows unauthenticated users to access guarded pages through a crafted HTTP request to the server. |
2021-08-13 |
not yet calculated |
CVE-2021-37351
MISC |
nagios — xi_docker_wizard
|
Nagios XI before version 5.8.5 is vulnerable to local privilege escalation because xi-sys.cfg is being imported from the var directory for some scripts with elevated permissions. |
2021-08-13 |
not yet calculated |
CVE-2021-37345
MISC
MISC |
nagios — xi_docker_wizard
|
Nagios XI Docker Wizard before version 1.1.3 is vulnerable to SSRF due to improper sanitation in table_population.php. |
2021-08-13 |
not yet calculated |
CVE-2021-37353
MISC |
nagios — xi_docker_wizard
|
A path traversal vulnerability exists in Nagios XI below version 5.8.5 AutoDiscovery component and could lead to post authenticated RCE under security context of the user running Nagios. |
2021-08-13 |
not yet calculated |
CVE-2021-37343
MISC |
nagios — xi_docker_wizard
|
Nagios XI before version 5.8.5 is vulnerable to local privilege escalation because getprofile.sh does not validate the directory name it receives as an argument. |
2021-08-13 |
not yet calculated |
CVE-2021-37347
MISC |
nagios — xi_docker_wizard
|
Nagios XI before version 5.8.5 is vulnerable to SQL injection vulnerability in Bulk Modifications Tool due to improper input sanitisation. |
2021-08-13 |
not yet calculated |
CVE-2021-37350
MISC |
nagios — xi_docker_wizard
|
An open redirect vulnerability exists in Nagios XI before version 5.8.5 that could lead to spoofing. To exploit the vulnerability, an attacker could send a link that has a specially crafted URL and convince the user to click the link. |
2021-08-13 |
not yet calculated |
CVE-2021-37352
MISC |
nagios — xi_docker_wizard
|
Nagios XI before version 5.8.5 is vulnerable to local privilege escalation because cleaner.php does not sanitise input read from the database. |
2021-08-13 |
not yet calculated |
CVE-2021-37349
MISC |
nagios — xi_docker_wizard
|
Nagios XI before version 5.8.5 is vulnerable to local file inclusion through improper limitation of a pathname in index.php. |
2021-08-13 |
not yet calculated |
CVE-2021-37348
MISC |
nagios — xi_switch_wizard
|
Nagios XI Switch Wizard before version 2.5.7 is vulnerable to remote code execution through improper neutralisation of special elements used in an OS Command (OS Command injection). |
2021-08-13 |
not yet calculated |
CVE-2021-37344
MISC |
nagios — xi_watchguard_wizard
|
Nagios XI WatchGuard Wizard before version 1.4.8 is vulnerable to remote code execution through Improper neutralisation of special elements used in an OS Command (OS Command injection). |
2021-08-13 |
not yet calculated |
CVE-2021-37346
MISC |
| netgear — multiple_devices |
Certain NETGEAR devices are affected by stored XSS. This affects D6200 before 1.1.00.40, D7000 before 1.0.1.78, R6020 before 1.0.0.48, R6080 before 1.0.0.48, R6120 before 1.0.0.66, R6260 before 1.1.0.78, R6700v2 before 1.2.0.76, R6800 before 1.2.0.76, R6900v2 before 1.2.0.76, R6850 before 1.1.0.78, R7200 before 1.2.0.76, R7350 before 1.2.0.76, R7400 before 1.2.0.76, R7450 before 1.2.0.76, AC2100 before 1.2.0.76, AC2400 before 1.2.0.76, AC2600 before 1.2.0.76, and RAX40 before 1.0.3.62. |
2021-08-11 |
not yet calculated |
CVE-2021-38537
MISC |
| netgear — multiple_devices |
Certain NETGEAR devices are affected by command injection by an unauthenticated attacker. This affects RBK40 before 2.5.1.16, RBR40 before 2.5.1.16, RBS40 before 2.5.1.16, RBK20 before 2.5.1.16, RBR20 before 2.5.1.16, RBS20 before 2.5.1.16, RBK50 before 2.5.1.16, RBR50 before 2.5.1.16, RBS50 before 2.5.1.16, and RBS50Y before 2.6.1.40. |
2021-08-11 |
not yet calculated |
CVE-2021-38530
MISC |
| netgear — multiple_devices |
Certain NETGEAR devices are affected by denial of service. This affects R6400v2 before 1.0.4.98, R6700v3 before 1.0.4.98, R7900 before 1.0.3.18, and R8000 before 1.0.4.46. |
2021-08-11 |
not yet calculated |
CVE-2021-38515
MISC |
| netgear — multiple_devices |
Certain NETGEAR devices are affected by command injection by an unauthenticated attacker. This affects D7800 before 1.0.1.56, R7800 before 1.0.2.68, R8900 before 1.0.4.26, and R9000 before 1.0.4.26. |
2021-08-11 |
not yet calculated |
CVE-2021-38529
MISC |
netgear — multiple_devices
|
Certain NETGEAR devices are affected by command injection by an authenticated user. This affects R6400 before 1.0.1.52, R6400v2 before 1.0.4.84, R6700v3 before 1.0.4.84, R6700v2 before 1.2.0.62, R6900v2 before 1.2.0.62, and R7000P before 1.3.2.124. |
2021-08-11 |
not yet calculated |
CVE-2021-38520
MISC |
netgear — multiple_devices
|
Certain NETGEAR devices are affected by a buffer overflow by an unauthenticated attacker. This affects RAX35 before 1.0.3.94, RAX38 before 1.0.3.94, and RAX40 before 1.0.3.94. |
2021-08-11 |
not yet calculated |
CVE-2021-38526
MISC |
netgear — multiple_devices
|
Certain NETGEAR devices are affected by command injection by an unauthenticated attacker. This affects CBR40 before 2.5.0.14, EX6100v2 before 1.0.1.98, EX6150v2 before 1.0.1.98, EX6250 before 1.0.0.132, EX6400 before 1.0.2.158, EX6400v2 before 1.0.0.132, EX6410 before 1.0.0.132, EX6420 before 1.0.0.132, EX7300 before 1.0.2.158, EX7300v2 before 1.0.0.132, EX7320 before 1.0.0.132, EX7700 before 1.0.0.216, EX8000 before 1.0.1.232, R7800 before 1.0.2.78, RBK12 before 2.6.1.44, RBR10 before 2.6.1.44, RBS10 before 2.6.1.44, RBK20 before 2.6.1.38, RBR20 before 2.6.1.36, RBS20 before 2.6.1.38, RBK40 before 2.6.1.38, RBR40 before 2.6.1.36, RBS40 before 2.6.1.38, RBK50 before 2.6.1.40, RBR50 before 2.6.1.40, RBS50 before 2.6.1.40, RBK752 before 3.2.16.6, RBR750 before 3.2.16.6, RBS750 before 3.2.16.6, RBK852 before 3.2.16.6, RBR850 before 3.2.16.6, RBS850 before 3.2.16.6, RBS40V before 2.6.2.4, RBS50Y before 2.6.1.40, RBW30 before 2.6.2.2, and XR500 before 2.3.2.114. |
2021-08-11 |
not yet calculated |
CVE-2021-38527
MISC |
netgear — multiple_devices
|
Certain NETGEAR devices are affected by command injection by an authenticated user. This affects R6400 before 1.0.1.50, R7900P before 1.4.1.50, R8000P before 1.4.1.50, RAX75 before 1.0.1.62, and RAX80 before 1.0.1.62. |
2021-08-11 |
not yet calculated |
CVE-2021-38521
MISC |
netgear — multiple_devices
|
Certain NETGEAR devices are affected by lack of access control at the function level. This affects D6220 before 1.0.0.48, D6400 before 1.0.0.82, D7000v2 before 1.0.0.52, D7800 before 1.0.1.44, D8500 before 1.0.3.43, DC112A before 1.0.0.40, DGN2200v4 before 1.0.0.108, RBK50 before 2.3.0.32, RBR50 before 2.3.0.32, RBS50 before 2.3.0.32, RBK20 before 2.3.0.28, RBR20 before 2.3.0.28, RBS20 before 2.3.0.28, RBK40 before 2.3.0.28, RBR40 before 2.3.0.28, RBS40 before 2.3.0.28, R6020 before 1.0.0.34, R6080 before 1.0.0.34, R6120 before 1.0.0.44, R6220 before 1.1.0.80, R6230 before 1.1.0.80, R6250 before 1.0.4.34, R6260 before 1.1.0.40, R6850 before 1.1.0.40, R6350 before 1.1.0.40, R6400v2 before 1.0.2.62, R6700v3 before 1.0.2.62, R6700v2 before 1.2.0.36, R6800 before 1.2.0.36, R6900v2 before 1.2.0.36, R7000 before 1.0.9.34, R6900P before 1.3.1.44, R7000P before 1.3.1.44, R7100LG before 1.0.0.48, R7200 before 1.2.0.48, R7350 before 1.2.0.48, R7400 before 1.2.0.48, R7450 before 1.2.0.36, AC2100 before 1.2.0.36, AC2400 before 1.2.0.36, AC2600 before 1.2.0.36, R7500v2 before 1.0.3.38, R7800 before 1.0.2.58, R7900 before 1.0.3.8, R7960P before 1.4.1.44, R8000 before 1.0.4.28, R7900P before 1.4.1.30, R8000P before 1.4.1.30, R8900 before 1.0.4.2, R9000 before 1.0.4.2, RAX120 before 1.0.0.74, RBK752 before 3.2.16.6, RBR750 before 3.2.16.6, RBS750 before 3.2.16.6, RBK852 before 3.2.16.6, RBR850 before 3.2.16.6, RBS850 before 3.2.16.6, WNR3500Lv2 before 1.2.0.56, XR450 before 2.3.2.32, and XR500 before 2.3.2.32. |
2021-08-11 |
not yet calculated |
CVE-2021-38516
MISC |
netgear — multiple_devices
|
Certain NETGEAR devices are affected by command injection by an unauthenticated attacker. This affects D8500 before 1.0.3.58, R6900P before 1.3.2.132, R7000P before 1.3.2.132, R7100LG before 1.0.0.64, WNDR3400v3 before 1.0.1.38, and XR300 before 1.0.3.56. |
2021-08-11 |
not yet calculated |
CVE-2021-38528
MISC |
netgear — multiple_devices
|
Certain NETGEAR devices are affected by command injection by an authenticated user. This affects RAX200 before 1.0.4.120, RAX75 before 1.0.4.120, RAX80 before 1.0.4.120, RBK852 before 3.2.17.12, RBR850 before 3.2.17.12, and RBS850 before 3.2.17.12. |
2021-08-11 |
not yet calculated |
CVE-2021-38518
MISC |
netgear — multiple_devices
|
Certain NETGEAR devices are affected by out-of-bounds reads and writes. This affects R6400 before 1.0.1.70, RAX75 before 1.0.4.120, RAX80 before 1.0.4.120, and XR300 before 1.0.3.50. |
2021-08-11 |
not yet calculated |
CVE-2021-38517
MISC |
netgear — multiple_devices
|
Certain NETGEAR devices are affected by command injection by an authenticated user. This affects R6250 before 1.0.4.36, R6300v2 before 1.0.4.36, R6400 before 1.0.1.50, R6400v2 before 1.0.2.66, R6700v3 before 1.0.2.66, R6700 before 1.0.2.8, R6900 before 1.0.2.8, R7000 before 1.0.9.88, R6900P before 1.3.2.132, R7100LG before 1.0.0.52, R7900 before 1.0.3.10, R8000 before 1.0.4.46, R7900P before 1.4.1.50, R8000P before 1.4.1.50, and RAX80 before 1.0.1.40. |
2021-08-11 |
not yet calculated |
CVE-2021-38519
MISC |
netgear — multiple_devices
|
Certain NETGEAR devices are affected by a stack-based buffer overflow by an authenticated user. This affects MK62 before 1.0.6.110, MR60 before 1.0.6.110, MS60 before 1.0.6.110, RAX15 before 1.0.2.82, RAX20 before 1.0.2.82, RAX200 before 1.0.3.106, RAX45 before 1.0.2.32, RAX50 before 1.0.2.32, RAX75 before 1.0.3.106, RAX80 before 1.0.3.106, RBK752 before 3.2.16.6, RBR750 before 3.2.16.6, and RBS750 before 3.2.16.6. |
2021-08-11 |
not yet calculated |
CVE-2021-38524
MISC |
netgear — multiple_devices
|
Certain NETGEAR devices are affected by authentication bypass. This affects RBK852 before 3.2.10.11, RBR850 before 3.2.10.11, RBS850 before 3.2.10.11, CBR40 before 2.5.0.10, EAX20 before 1.0.0.48, MK62 before 1.0.6.110, MR60 before 1.0.6.110, MS60 before 1.0.6.110, RBK752 before 3.2.10.10, RBR750 before 3.2.10.10, and RBS750 before 3.2.10.10. |
2021-08-11 |
not yet calculated |
CVE-2021-38513
MISC |
netgear — multiple_devices
|
Certain NETGEAR devices are affected by CSRF. This affects EX3700 before 1.0.0.90, EX3800 before 1.0.0.90, EX6120 before 1.0.0.64, and EX6130 before 1.0.0.44. |
2021-08-11 |
not yet calculated |
CVE-2021-32122
MISC |
netgear — multiple_devices
|
Certain NETGEAR devices are affected by a stack-based buffer overflow by an authenticated user. This affects D3600 before 1.0.0.76, D6000 before 1.0.0.76, D6200 before 1.1.00.36, D7000 before 1.0.1.70, EX6200v2 before 1.0.1.78, EX7000 before 1.0.1.78, EX8000 before 1.0.1.186, JR6150 before 1.0.1.18, PR2000 before 1.0.0.28, R6020 before 1.0.0.42, R6050 before 1.0.1.18, R6080 before 1.0.0.42, R6120 before 1.0.0.46, R6220 before 1.1.0.80, R6260 before 1.1.0.64, R6300v2 before 1.0.4.34, R6700 before 1.0.2.6, R6700v2 before 1.2.0.36, R6800 before 1.2.0.36, R6900 before 1.0.2.4, R6900P before 1.3.1.64, R6900v2 before 1.2.0.36, R7000 before 1.0.9.42, R7000P before 1.3.1.64, R7800 before 1.0.2.60, R8900 before 1.0.4.12, R9000 before 1.0.4.12, and XR500 before 2.3.2.40. |
2021-08-11 |
not yet calculated |
CVE-2021-38525
MISC |
netgear — multiple_devices
|
Certain NETGEAR devices are affected by authentication bypass. This affects D3600 before 1.0.0.72, D6000 before 1.0.0.72, D6100 before 1.0.0.63, D6200 before 1.1.00.34, D6220 before 1.0.0.48, D6400 before 1.0.0.86, D7000 before 1.0.1.70, D7000v2 before 1.0.0.52, D7800 before 1.0.1.56, D8500 before 1.0.3.44, DC112A before 1.0.0.42, DGN2200v4 before 1.0.0.108, DGND2200Bv4 before 1.0.0.108, EX2700 before 1.0.1.48, EX3700 before 1.0.0.76, EX3800 before 1.0.0.76, EX6000 before 1.0.0.38, EX6100 before 1.0.2.24, EX6100v2 before 1.0.1.76, EX6120 before 1.0.0.42, EX6130 before 1.0.0.28, EX6150v1 before 1.0.0.42, EX6150v2 before 1.0.1.76, EX6200 before 1.0.3.88, EX6200v2 before 1.0.1.72, EX6400 before 1.0.2.136, EX7000 before 1.0.0.66, EX7300 before 1.0.2.136, EX8000 before 1.0.1.180, RBK50 before 2.1.4.10, RBR50 before 2.1.4.10, RBS50 before 2.1.4.10, RBK40 before 2.1.4.10, RBR40 before 2.1.4.10, RBS40 before 2.1.4.10, RBW30 before 2.2.1.204, PR2000 before 1.0.0.28, R6020 before 1.0.0.38, R6080 before 1.0.0.38, R6050 before 1.0.1.18, JR6150 before 1.0.1.18, R6120 before 1.0.0.46, R6220 before 1.1.0.86, R6250 before 1.0.4.34, R6300v2 before 1.0.4.32, R6400 before 1.0.1.44, R6400v2 before 1.0.2.62, R6700 before 1.0.1.48, R6700v2 before 1.2.0.36, R6800 before 1.2.0.36, R6900v2 before 1.2.0.36, R6900 before 1.0.1.48, R7000 before 1.0.9.34, R6900P before 1.3.1.64, R7000P before 1.3.1.64, R7100LG before 1.0.0.48, R7300DST before 1.0.0.70, R7500v2 before 1.0.3.38, R7800 before 1.0.2.52, R7900 before 1.0.3.8, R8000 before 1.0.4.28, R7900P before 1.4.1.30, R8000P before 1.4.1.30, R8300 before 1.0.2.128, R8500 before 1.0.2.128, R9000 before 1.0.3.10, RBS40V before 2.2.0.58, RBK50V before 2.2.0.58, WN2000RPTv3 before 1.0.1.32, WN2500RPv2 before 1.0.1.54, WN3000RPv3 before 1.0.2.78, WN3100RPv2 before 1.0.0.66, WNDR3400v3 before 1.0.1.22, WNDR3700v4 before 1.0.2.102, WNDR4300v1 before 1.0.2.104, WNDR4300v2 before 1.0.0.56, WNDR4500v3 before 1.0.0.56, WNR2000v5 (R2000) before 1.0.0.66, WNR2020 before 1.1.0.62, WNR2050 before 1.1.0.62, WNR3500Lv2 before 1.2.0.62, and XR500 before 2.3.2.22. |
2021-08-11 |
not yet calculated |
CVE-2021-38514
MISC |
netgear — multiple_devices
|
Certain NETGEAR devices are affected by privilege escalation. This affects D8500 before 1.0.3.44, R6400v2 before 1.0.2.66, R6700 before 1.0.2.6, R6700v3 before 1.0.2.66, R6900 before 1.0.2.4, R6900P before 1.3.2.126, R7000 before 1.0.9.42, R7000P before 1.3.2.126, R7100LG before 1.0.0.50, R7300DST before 1.0.0.70, R7900 before 1.0.3.10, R8300 before 1.0.2.130, and R8500 before 1.0.2.130. |
2021-08-11 |
not yet calculated |
CVE-2021-38539
MISC |
netgear — multiple_devices
|
Certain NETGEAR devices are affected by stored XSS. This affects D7800 before 1.0.1.56, R7800 before 1.0.2.68, R8900 before 1.0.4.26, R9000 before 1.0.4.26, RAX120 before 1.0.0.78, RBK20 before 2.3.5.26, RBR20 before 2.3.5.26, RBS20 before 2.3.5.26, RBK40 before 2.3.5.30, RBR40 before 2.3.5.30, RBS40 before 2.3.5.30, RBK50 before 2.3.5.30, RBR50 before 2.3.5.30, RBS50 before 2.3.5.30, and XR500 before 2.3.2.56. |
2021-08-11 |
not yet calculated |
CVE-2021-38538
MISC |
netgear — multiple_devices
|
Certain NETGEAR devices are affected by incorrect configuration of security settings. This affects D6200 before 1.1.00.40, D7000 before 1.0.1.78, R6020 before 1.0.0.42, R6080 before 1.0.0.42, R6120 before 1.0.0.66, R6260 before 1.1.0.78, R6700v2 before 1.2.0.76, R6800 before 1.2.0.76, R6900v2 before 1.2.0.76, R7450 before 1.2.0.76, AC2100 before 1.2.0.76, and AC2400 before 1.2.0.76. |
2021-08-11 |
not yet calculated |
CVE-2021-38531
MISC |
netgear — multiple_devices
|
Certain NETGEAR devices are affected by stored XSS. This affects D3600 before 1.0.0.76, D6000 before 1.0.0.76, D6100 before 1.0.0.60, D6200 before 1.1.00.36, D6220 before 1.0.0.52, D6400 before 1.0.0.86, D7000 before 1.0.1.70, D7000v2 before 1.0.0.53, D8500 before 1.0.3.44, DC112A before 1.0.0.42, DGN2200v4 before 1.0.0.110, DGND2200Bv4 before 1.0.0.109, DM200 before 1.0.0.61, JR6150 before 1.0.1.18, PR2000 before 1.0.0.28, R6020 before 1.0.0.42, R6050 before 1.0.1.18, R6080 before 1.0.0.42, R6220 before 1.1.0.80, R6230 before 1.1.0.80, R6250 before 1.0.4.34, R6260 before 1.1.0.64, R6300v2 before 1.0.4.34, R6400 before 1.0.1.46, R6400v2 before 1.0.2.62, R6700 before 1.0.2.6, R6700v2 before 1.2.0.36, R6700v3 before 1.0.2.62, R6800 before 1.2.0.36, R6900 before 1.0.2.4, R6900P before 1.3.1.64, R6900v2 before 1.2.0.36, R7000 before 1.0.9.60, R7000P before 1.3.1.64, R7100LG before 1.0.0.50, R7300DST before 1.0.0.70, R7450 before 1.2.0.36, R7900 before 1.0.3.8, R7900P before 1.4.1.50, R8000 before 1.0.4.28, R8000P before 1.4.1.50, R8300 before 1.0.2.130, R8500 before 1.0.2.130, WNDR3400v3 before 1.0.1.24, WNR2020 before 1.1.0.62, WNR3500Lv2 before 1.2.0.62, XR450 before 2.3.2.40, and XR500 before 2.3.2.40. |
2021-08-11 |
not yet calculated |
CVE-2021-38534
MISC |
netgear — multiple_devices
|
Certain NETGEAR devices are affected by stored XSS. This affects D6200 before 1.1.00.40, D7000 before 1.0.1.78, R6020 before 1.0.0.48, R6080 before 1.0.0.48, R6120 before 1.0.0.76, R6260 before 1.1.0.78, R6700v2 before 1.2.0.76, R6800 before 1.2.0.76, R6900v2 before 1.2.0.76, R6850 before 1.1.0.78, R7200 before 1.2.0.76, R7350 before 1.2.0.76, R7400 before 1.2.0.76, R7450 before 1.2.0.76, AC2100 before 1.2.0.76, AC2400 before 1.2.0.76, AC2600 before 1.2.0.76, RAX35 before 1.0.3.62, and RAX40 before 1.0.3.62. |
2021-08-11 |
not yet calculated |
CVE-2021-38535
MISC |
netgear — multiple_devices
|
Certain NETGEAR devices are affected by stored XSS. This affects D6200 before 1.1.00.40, D7000 before 1.0.1.78, R6020 before 1.0.0.48, R6080 before 1.0.0.48, R6120 before 1.0.0.66, R6260 before 1.1.0.78, R6700v2 before 1.2.0.76, R6800 before 1.2.0.76, R6900v2 before 1.2.0.76, R6850 before 1.1.0.78, R7200 before 1.2.0.76, R7350 before 1.2.0.76, R7400 before 1.2.0.76, R7450 before 1.2.0.76, AC2100 before 1.2.0.76, AC2400 before 1.2.0.76, AC2600 before 1.2.0.76, RAX35 before 1.0.3.62, and RAX40 before 1.0.3.62. |
2021-08-11 |
not yet calculated |
CVE-2021-38536
MISC |
netgear — r6400_devices
|
NETGEAR R6400 devices before 1.0.1.52 are affected by a stack-based buffer overflow by an authenticated user. |
2021-08-11 |
not yet calculated |
CVE-2021-38522
MISC |
netgear — r6400_devices
|
NETGEAR R6400 devices before 1.0.1.70 are affected by a stack-based buffer overflow by an authenticated user. |
2021-08-11 |
not yet calculated |
CVE-2021-38523
MISC |
netgear — rax40
|
NETGEAR RAX40 devices before 1.0.3.64 are affected by stored XSS. |
2021-08-11 |
not yet calculated |
CVE-2021-38533
MISC |
netgear — wac104_devices
|
NETGEAR WAC104 devices before 1.0.4.15 are affected by incorrect configuration of security settings. |
2021-08-11 |
not yet calculated |
CVE-2021-38532
MISC |
netskope — client
|
Netskope Client through 77 allows low-privileged users to elevate their privileges to NT AUTHORITYSYSTEM. |
2021-08-12 |
not yet calculated |
CVE-2020-24576
MISC
MISC |
netweaver — enterprise_portal
|
Under certain conditions, NetWeaver Enterprise Portal, versions – 7.10, 7.11, 7.20, 7.30, 7.31, 7.40, 7.50, does not sufficiently encode report data. An attacker can craft malicious data and print it to the report. In a successful attack, a victim opens the report, and the malicious script gets executed in the victim’s browser, resulting in a Stored Cross-Site Scripting (XSS) vulnerability. |
2021-08-10 |
not yet calculated |
CVE-2021-33702
MISC
MISC |
netweaver — enterprise_portal
|
Under certain conditions, NetWeaver Enterprise Portal, versions – 7.30, 7.31, 7.40, 7.50, does not sufficiently encode URL parameters. An attacker can craft a malicious link and send it to a victim. A successful attack results in Reflected Cross-Site Scripting (XSS) vulnerability. |
2021-08-10 |
not yet calculated |
CVE-2021-33703
MISC
MISC |
newsone — cms
|
An arbitrary file upload in the <input type=”file” name=”user_image”> component of NewsOne CMS v1.1.0 allows attackers to webshell and execute arbitrary commands. |
2021-08-11 |
not yet calculated |
CVE-2020-21976
MISC |
next.js — next.js
|
Next.js is an open source website development framework to be used with the React library. In affected versions specially encoded paths could be used when pages/_error.js was statically generated allowing an open redirect to occur to an external site. In general, this redirect does not directly harm users although can allow for phishing attacks by redirecting to an attacker’s domain from a trusted domain. We recommend everyone to upgrade regardless of whether you can reproduce the issue or not. The issue has been patched in release 11.1.0. |
2021-08-12 |
not yet calculated |
CVE-2021-37699
MISC
CONFIRM |
nim-lang — nim-lang
|
A vulnerability in all versions of Nim-lang allows unauthenticated attackers to write files to arbitrary directories via a crafted zip file with dot-slash characters included in the name of the crafted file. |
2021-08-10 |
not yet calculated |
CVE-2020-23171
MISC |
nuance — winscribe_diction
|
The exporter/Login.aspx login form in the Exporter in Nuance Winscribe Dictation 4.1.0.99 is vulnerable to SQL injection that allows a remote, unauthenticated attacker to read the database (and execute code in some situations) via the txtPassword parameter. |
2021-08-12 |
not yet calculated |
CVE-2021-37599
MISC
MISC |
nuvoton — trusted_platform_module
|
An attacker with physical access to Nuvoton Trusted Platform Module (NPCT75x 7.2.x before 7.2.2.0) could extract an Elliptic Curve Cryptography (ECC) private key via a side-channel attack against ECDSA, because of an Observable Timing Discrepancy. |
2021-08-10 |
not yet calculated |
CVE-2020-25082
MISC |
| nvidia — camera |
NVIDIA camera firmware contains a multistep, timing-related vulnerability where an unauthorized modification by camera resources may result in loss of data integrity or denial of service across several streams. |
2021-08-11 |
not yet calculated |
CVE-2021-1109
MISC |
nvidia — camera
|
NVIDIA camera firmware contains a vulnerability where an unauthorized modification by camera resources may result in complete denial of service and loss of partial data integrity for all clients. |
2021-08-11 |
not yet calculated |
CVE-2021-1113
MISC |
nvidia — dcgm
|
NVIDIA DCGM contains a vulnerability in the DIAG module where any user can inject shared libraries into the DCGM server, which is usually running as root, which may lead to privilege escalation, total loss of confidentiality and integrity, and complete denial of service |
2021-08-13 |
not yet calculated |
CVE-2021-34398
MISC |
on24 — screenshare
|
The ON24 ScreenShare (aka DesktopScreenShare.app) plugin before 2.0 for macOS allows remote file access via its built-in HTTP server. This allows unauthenticated remote users to retrieve files accessible to the logged-on macOS user. When a remote user sends a crafted HTTP request to the server, it triggers a code path that will download a configuration file from a specified remote machine over HTTP. There is an XXE flaw in processing of this configuration file that allows reading local (to macOS) files and uploading them to remote machines. |
2021-08-13 |
not yet calculated |
CVE-2021-34823
MISC
MISC |
onefuzz — onefuzz
|
OneFuzz is an open source self-hosted Fuzzing-As-A-Service platform. Starting with OneFuzz 2.12.0 or greater, an incomplete authorization check allows an authenticated user from any Azure Active Directory tenant to make authorized API calls to a vulnerable OneFuzz instance. To be vulnerable, a OneFuzz deployment must be both version 2.12.0 or greater and deployed with the non-default –multi_tenant_domain option. This can result in read/write access to private data such as software vulnerability and crash information, security testing tools and proprietary code and symbols. Via authorized API calls, this also enables tampering with existing data and unauthorized code execution on Azure compute resources. This issue is resolved starting in release 2.31.0, via the addition of application-level check of the bearer token’s `issuer` against an administrator-configured allowlist. As a workaround users can restrict access to the tenant of a deployed OneFuzz instance < 2.31.0 by redeploying in the default configuration, which omits the `–multi_tenant_domain` option. |
2021-08-13 |
not yet calculated |
CVE-2021-37705
MISC
MISC
MISC
CONFIRM
MISC |
open-graph — open-graph
|
This affects the package open-graph before 0.2.6. The function parse could be tricked into adding or modifying properties of Object.prototype using a __proto__ or constructor payload. |
2021-08-08 |
not yet calculated |
CVE-2021-23419
MISC
MISC |
open_ticket_request_system — help_desk
|
Multiple SQL injection vulnerabilities in Open Ticket Request System (OTRS) Help Desk 3.0.x before 3.0.22, 3.1.x before 3.1.18, and 3.2.x before 3.2.9 allow remote authenticated users to execute arbitrary SQL commands via unspecified vectors related to Kernel/Output/HTML/PreferencesCustomQueue.pm, Kernel/System/CustomerCompany.pm, Kernel/System/Ticket/IndexAccelerator/RuntimeDB.pm, Kernel/System/Ticket/IndexAccelerator/StaticDB.pm, and Kernel/System/TicketSearch.pm. |
2021-08-09 |
not yet calculated |
CVE-2013-4717
MISC |
open_ticket_request_system — open_ticket_request_system
|
Cross-site scripting (XSS) vulnerability in Open Ticket Request System (OTRS) ITSM 3.0.x before 3.0.9, 3.1.x before 3.1.10, and 3.2.x before 3.2.7 allows remote authenticated users to inject arbitrary web script or HTML via an ITSM ConfigItem search. |
2021-08-09 |
not yet calculated |
CVE-2013-4718
MISC |
openbaraza — hcm
|
openBaraza HCM 3.1.6 does not properly neutralize user-controllable input: an unauthenticated remote attacker can conduct a stored cross-site scripting (XSS) attack against an administrative user from hr/subscription.jsp and hr/application.jsp and and hr/index.jsp (with view=). |
2021-08-13 |
not yet calculated |
CVE-2021-38619
MISC
MISC
MISC |
openbaraza — openbaraza
|
openBaraza HCM 3.1.6 does not properly neutralize user-controllable input, which allows reflected cross-site scripting (XSS) on multiple pages: hr/subscription.jsp and hr/application.jsp and and hr/index.jsp (with view= and data=). |
2021-08-13 |
not yet calculated |
CVE-2021-38583
MISC
MISC
MISC |
openstack — keystone
|
OpenStack Keystone 10.x through 16.x before 16.0.2, 17.x before 17.0.1, 18.x before 18.0.1, and 19.x before 19.0.1 allows information disclosure during account locking (related to PCI DSS features). By guessing the name of an account and failing to authenticate multiple times, any unauthenticated actor could both confirm the account exists and obtain that account’s corresponding UUID, which might be leveraged for other unrelated attacks. All deployments enabling security_compliance.lockout_failure_attempts are affected. |
2021-08-06 |
not yet calculated |
CVE-2021-38155
MISC
CONFIRM
MLIST |
owntone — owntone
|
OwnTone (aka owntone-server) through 28.1 has a use-after-free in net_bind() in misc.c. |
2021-08-10 |
not yet calculated |
CVE-2021-38383
MISC |
| palo_alto_networks — pan-os |
An improper authentication vulnerability exists in Palo Alto Networks PAN-OS software that enables a SAML authenticated attacker to impersonate any other user in the GlobalProtect Portal and GlobalProtect Gateway when they are configured to use SAML authentication. This issue impacts: PAN-OS 8.1 versions earlier than PAN-OS 8.1.19; PAN-OS 9.0 versions earlier than PAN-OS 9.0.14; PAN-OS 9.1 versions earlier than PAN-OS 9.1.9; PAN-OS 10.0 versions earlier than PAN-OS 10.0.5. PAN-OS 10.1 versions are not impacted. |
2021-08-11 |
not yet calculated |
CVE-2021-3046
CONFIRM |
palo_alto_networks — pan-os
|
An OS command injection vulnerability in the Palo Alto Networks PAN-OS web interface enables an authenticated administrator to execute arbitrary OS commands to escalate privileges. This issue impacts: PAN-OS 9.0 version 9.0.10 through PAN-OS 9.0.14; PAN-OS 9.1 version 9.1.4 through PAN-OS 9.1.10; PAN-OS 10.0 version 10.0.7 and earlier PAN-OS 10.0 versions; PAN-OS 10.1 version 10.1.0 through PAN-OS 10.1.1. Prisma Access firewalls and firewalls running PAN-OS 8.1 versions are not impacted by this issue. |
2021-08-11 |
not yet calculated |
CVE-2021-3050
CONFIRM |
palo_alto_networks — pan-os
|
An OS command argument injection vulnerability in the Palo Alto Networks PAN-OS web interface enables an authenticated administrator to read any arbitrary file from the file system. This issue impacts: PAN-OS 8.1 versions earlier than PAN-OS 8.1.19; PAN-OS 9.0 versions earlier than PAN-OS 9.0.14; PAN-OS 9.1 versions earlier than PAN-OS 9.1.10. PAN-OS 10.0 and later versions are not impacted. |
2021-08-11 |
not yet calculated |
CVE-2021-3045
CONFIRM |
palo_alto_networks — pan-os
|
A cryptographically weak pseudo-random number generator (PRNG) is used during authentication to the Palo Alto Networks PAN-OS web interface. This enables an authenticated attacker, with the capability to observe their own authentication secrets over a long duration on the PAN-OS appliance, to impersonate another authenticated web interface administrator’s session. This issue impacts: PAN-OS 8.1 versions earlier than PAN-OS 8.1.19; PAN-OS 9.0 versions earlier than PAN-OS 9.0.14; PAN-OS 9.1 versions earlier than PAN-OS 9.1.10; PAN-OS 10.0 versions earlier than PAN-OS 10.0.4. PAN-OS 10.1 versions are not impacted. |
2021-08-11 |
not yet calculated |
CVE-2021-3047
CONFIRM |
palo_alto_networks — pan-os
|
Certain invalid URL entries contained in an External Dynamic List (EDL) cause the Device Server daemon (devsrvr) to stop responding. This condition causes subsequent commits on the firewall to fail and prevents administrators from performing commits and configuration changes even though the firewall remains otherwise functional. If the firewall then restarts, it results in a denial-of-service (DoS) condition and the firewall stops processing traffic. This issue impacts: PAN-OS 9.0 versions earlier than PAN-OS 9.0.14; PAN-OS 9.1 versions earlier than PAN-OS 9.1.9; PAN-OS 10.0 versions earlier than PAN-OS 10.0.5. PAN-OS 8.1 and PAN-OS 10.1 versions are not impacted. |
2021-08-11 |
not yet calculated |
CVE-2021-3048
CONFIRM |
parsers — parsers
|
Parsers in the open source project RCDCAP before 1.0.5 allow remote attackers to execute arbitrary code or cause a denial of service (memory corruption and application crash) via specially crafted packets. |
2021-08-12 |
not yet calculated |
CVE-2021-37222
MISC
MISC |
pbootcms — pbootcms
|
Cross Site Scripting (XSS) vulnerability exists in PbootCMS v1.3.7 via the title parameter in the mod function in SingleController.php. |
2021-08-12 |
not yet calculated |
CVE-2020-18456
MISC |
pear — admin_think
|
Pear Admin Think through 2.1.2 has an arbitrary file upload vulnerability that allows attackers to execute arbitrary code remotely. A .php file can be uploaded via admin.php/index/upload because app/common/service/UploadService.php mishandles fileExt. |
2021-08-12 |
not yet calculated |
CVE-2021-29377
MISC |
phpfastcache — phpfastcache
|
PhpFastCache is a high-performance backend cache system (packagist package phpfastcache/phpfastcache). In versions before 6.1.5, 7.1.2, and 8.0.7 the `phpinfo()` can be exposed if the `/vendor` is not protected from public access. This is a rare situation today since the vendor directory is often located outside the web directory or protected via server rule (.htaccess, etc). Only the v6, v7 and v8 will be patched respectively in 8.0.7, 7.1.2, 6.1.5. Older versions such as v5, v4 are not longer supported and will **NOT** be patched. As a workaround, protect the `/vendor` directory from public access. |
2021-08-12 |
not yet calculated |
CVE-2021-37704
CONFIRM
MISC
MISC
MISC
MISC
MISC
MISC
MISC |
pluxml — pluxml
|
PluXML 5.8.7 allows Article Editing stored XSS via Headline or Content. |
2021-08-12 |
not yet calculated |
CVE-2021-38602
MISC
MISC |
pluxml — pluxml
|
PluXML 5.8.7 allows core/admin/profil.php stored XSS via the Information field. |
2021-08-12 |
not yet calculated |
CVE-2021-38603
MISC
MISC
MISC |
polipo — polipo
|
** UNSUPPORTED WHEN ASSIGNED ** Polipo through 1.1.1, when NDEBUG is used, allows a heap-based buffer overflow during parsing of a Range header. NOTE: This vulnerability only affects products that are no longer supported by the maintainer. |
2021-08-12 |
not yet calculated |
CVE-2021-38614
MISC |
postgresql — postgresql
|
The set_user extension module before 2.0.1 for PostgreSQL allows a potential privilege escalation using RESET SESSION AUTHORIZATION after set_user(). |
2021-08-10 |
not yet calculated |
CVE-2021-38140
CONFIRM
MISC |
qnap — f_viocard
|
** UNSUPPORTED WHEN ASSIGNED ** QNAP F_VioCard 2312 and F_VioGate 2308 have hardcoded entries in authorized_keys files. NOTE: 1. All active models are not affected. The last affected model was EOL since 2010. 2. The legacy authorization mechanism is no longer adopted in all active models. |
2021-08-09 |
not yet calculated |
CVE-2013-6276
MISC
MISC |
qt — qt
|
Qt 5.0.0 through 6.1.2 has an out-of-bounds write in QOutlineMapper::convertPath (called from QRasterPaintEngine::fill and QPaintEngineEx::stroke). |
2021-08-12 |
not yet calculated |
CVE-2021-38593
MISC
MISC
MISC
MISC
MISC |
quectel — eg25-g_devices
|
Quectel EG25-G devices through 202006130814 allow executing arbitrary code remotely by using an AT command to place shell metacharacters in quectel_handle_fumo_cfg input in atfwd_daemon. |
2021-08-12 |
not yet calculated |
CVE-2021-31698
MISC |
raspberry — pi_3_b_and_4_b_devices
|
Raspberry Pi 3 B+ and 4 B devices through 2021-08-09, in certain specific use cases in which the device supplies power to audio-output equipment, allow remote attackers to recover speech signals from an LED on the device, via a telescope and an electro-optical sensor, aka a “Glowworm” attack. We assume that the Raspberry Pi supplies power to some speakers. The power indicator LED of the Raspberry Pi is connected directly to the power line, as a result, the intensity of a device’s power indicator LED is correlative to the power consumption. The sound played by the speakers affects the Raspberry Pi’s power consumption and as a result is also correlative to the light intensity of the LED. By analyzing measurements obtained from an electro-optical sensor directed at the power indicator LED of the Raspberry Pi, we can recover the sound played by the speakers. |
2021-08-11 |
not yet calculated |
CVE-2021-38545
MISC |
rengine — rengine
|
reNgine through 0.5 relies on a predictable directory name. |
2021-08-12 |
not yet calculated |
CVE-2021-38606
MISC |
risc-v — instruction_set_manual
|
The RISC-V Instruction Set Manual contains a documented ambiguity for the Machine Trap Vector Base Address (MTVEC) register that may lead to a vulnerability due to the initial state of the register not being defined, potentially leading to information disclosure, data tampering and denial of service. |
2021-08-13 |
not yet calculated |
CVE-2021-1104
CONFIRM |
rocket — chat_server
|
A sanitization vulnerability exists in Rocket.Chat server versions <3.13.2, <3.12.4, <3.11.4 that allowed queries to an endpoint which could result in a NoSQL injection, potentially leading to RCE. |
2021-08-09 |
not yet calculated |
CVE-2021-22910
MISC |
runprocess — runprocess
|
This affects the package codeception/codeception from 4.0.0 and before 4.1.22, before 3.1.3. The RunProcess class can be leveraged as a gadget to run arbitrary commands on a system that is deserializing user input without validation. |
2021-08-11 |
not yet calculated |
CVE-2021-23420
MISC
MISC
MISC
MISC |
| rust — rust |
An issue was discovered in the libsecp256k1 crate before 0.5.0 for Rust. It can verify an invalid signature because it allows the R or S parameter to be larger than the curve order, aka an overflow. |
2021-08-08 |
not yet calculated |
CVE-2021-38195
MISC
MISC |
| rust — rust |
An issue was discovered in the model crate through 2020-11-10 for Rust. The Shared data structure has an implementation of the Send and Sync traits without regard for the inner type. |
2021-08-08 |
not yet calculated |
CVE-2020-36460
MISC
MISC |
| rust — rust |
An issue was discovered in the noise_search crate through 2020-12-10 for Rust. There are unconditional implementations of Send and Sync for MvccRwLock. |
2021-08-08 |
not yet calculated |
CVE-2020-36461
MISC
MISC |
| rust — rust |
An issue was discovered in the array-tools crate before 0.3.2 for Rust. FixedCapacityDequeLike::clone() has a drop of uninitialized memory. |
2021-08-08 |
not yet calculated |
CVE-2020-36452
MISC
MISC |
| rust — rust |
An issue was discovered in the syncpool crate before 0.1.6 for Rust. There is an unconditional implementation of Send for Bucket2. |
2021-08-08 |
not yet calculated |
CVE-2020-36462
MISC
MISC |
| rust — rust |
An issue was discovered in the parc crate through 2020-11-14 for Rust. LockWeak<T> has an unconditional implementation of Send without trait bounds on T. |
2021-08-08 |
not yet calculated |
CVE-2020-36454
MISC
MISC |
| rust — rust |
An issue was discovered in the multiqueue crate through 2020-12-25 for Rust. There are unconditional implementations of Send for InnerSend<RW, T>, InnerRecv<RW, T>, FutInnerSend<RW, T>, and FutInnerRecv<RW, T>. |
2021-08-08 |
not yet calculated |
CVE-2020-36463
MISC
MISC |
| rust — rust |
An issue was discovered in the lever crate before 0.1.1 for Rust. AtomicBox<T> implements the Send and Sync traits for all types T. |
2021-08-08 |
not yet calculated |
CVE-2020-36457
MISC
MISC |
| rust — rust |
An issue was discovered in the chunky crate through 2020-08-25 for Rust. The Chunk API does not honor an alignment requirement. |
2021-08-08 |
not yet calculated |
CVE-2020-36433
MISC
MISC |
| rust — rust |
An issue was discovered in the conqueue crate before 0.4.0 for Rust. There are unconditional implementations of Send and Sync for QueueSender<T>. |
2021-08-08 |
not yet calculated |
CVE-2020-36437
MISC
MISC |
| rust — rust |
An issue was discovered in the libp2p-deflate crate before 0.27.1 for Rust. An uninitialized buffer is passed to AsyncRead::poll_read(), which is a user-provided trait function. |
2021-08-08 |
not yet calculated |
CVE-2020-36443
MISC
MISC |
| rust — rust |
An issue was discovered in the libsbc crate before 0.1.5 for Rust. For Decoder<R>, it implements Send for any R: Read. |
2021-08-08 |
not yet calculated |
CVE-2020-36440
MISC
MISC |
| rust — rust |
An issue was discovered in the appendix crate through 2020-11-15 for Rust. For the generic K and V type parameters, Send and Sync are implemented unconditionally. |
2021-08-08 |
not yet calculated |
CVE-2020-36469
MISC
MISC |
rust — rust
|
An issue was discovered in the abox crate before 0.4.1 for Rust. It implements Send and Sync for AtomicBox<T> with no requirement for T: Send and T: Sync. |
2021-08-08 |
not yet calculated |
CVE-2020-36441
MISC
MISC |
rust — rust
|
An issue was discovered in the lexer crate through 2020-11-10 for Rust. For ReaderResult<T, E>, there is an implementation of Sync with a trait bound of T: Send, E: Send. |
2021-08-08 |
not yet calculated |
CVE-2020-36458
MISC
MISC |
rust — rust
|
An issue was discovered in the async-coap crate through 2020-12-08 for Rust. Send and Sync are implemented for ArcGuard<RC, T> without trait bounds on RC. |
2021-08-08 |
not yet calculated |
CVE-2020-36444
MISC
MISC |
rust — rust
|
An issue was discovered in the toolshed crate through 2020-11-15 for Rust. In CopyCell<T>, the Send trait lacks bounds on the contained type. |
2021-08-08 |
not yet calculated |
CVE-2020-36456
MISC
MISC |
rust — rust
|
library/std/src/net/parser.rs in Rust before 1.53.0 does not properly consider extraneous zero characters at the beginning of an IP address string, which (in some situations) allows attackers to bypass access control that is based on IP addresses, because of unexpected octal interpretation. |
2021-08-07 |
not yet calculated |
CVE-2021-29922
MISC
MISC
MISC
MISC
MISC |
rust — rust
|
An issue was discovered in the unicycle crate before 0.7.1 for Rust. PinSlab<T> and Unordered<T, S> do not have bounds on their Send and Sync traits. |
2021-08-08 |
not yet calculated |
CVE-2020-36436
MISC
MISC |
rust — rust
|
An issue was discovered in the tiny_future crate before 0.4.0 for Rust. Future<T> does not have bounds on its Send and Sync traits. |
2021-08-08 |
not yet calculated |
CVE-2020-36438
MISC
MISC |
rust — rust
|
An issue was discovered in the cache crate through 2020-11-24 for Rust. There are unconditional implementations of Send and Sync for Cache<K>. |
2021-08-08 |
not yet calculated |
CVE-2020-36448
MISC
MISC |
rust — rust
|
An issue was discovered in the beef crate before 0.5.0 for Rust. beef::Cow has no Sync bound on its Send trait. |
2021-08-08 |
not yet calculated |
CVE-2020-36442
MISC
MISC |
rust — rust
|
An issue was discovered in the ticketed_lock crate before 0.3.0 for Rust. There are unconditional implementations of Send for ReadTicket<T> and WriteTicket<T>. |
2021-08-08 |
not yet calculated |
CVE-2020-36439
MISC
MISC |
rust — rust
|
An issue was discovered in the kekbit crate before 0.3.4 for Rust. For ShmWriter<H>, Send is implemented without requiring H: Send. |
2021-08-08 |
not yet calculated |
CVE-2020-36449
MISC
MISC |
rust — rust
|
An issue was discovered in the bunch crate through 2020-11-12 for Rust. There are unconditional implementations of Send and Sync for Bunch<T>. |
2021-08-08 |
not yet calculated |
CVE-2020-36450
MISC
MISC |
rust — rust
|
An issue was discovered in the rcu_cell crate through 2020-11-14 for Rust. There are unconditional implementations of Send and Sync for RcuCell<T>. |
2021-08-08 |
not yet calculated |
CVE-2020-36451
MISC
MISC |
rust — rust
|
An issue was discovered in the scottqueue crate through 2020-11-15 for Rust. There are unconditional implementations of Send and Sync for Queue<T>. |
2021-08-08 |
not yet calculated |
CVE-2020-36453
MISC
MISC |
rust — rust
|
An issue was discovered in the slock crate through 2020-11-17 for Rust. Slock<T> unconditionally implements Send and Sync. |
2021-08-08 |
not yet calculated |
CVE-2020-36455
MISC
MISC |
rust — rust
|
An issue was discovered in the dces crate through 2020-12-09 for Rust. The World type is marked as Send but lacks bounds on its EntityStore and ComponentStore. |
2021-08-08 |
not yet calculated |
CVE-2020-36459
MISC
MISC |
rust — rust
|
An issue was discovered in the v9 crate through 2020-12-18 for Rust. There is an unconditional implementation of Sync for SyncRef<T>. |
2021-08-08 |
not yet calculated |
CVE-2020-36447
MISC
MISC |
rust — rust
|
An issue was discovered in the max7301 crate before 0.2.0 for Rust. The ImmediateIO and TransactionalIO types implement Sync for all Expander<EI> types that they contain. |
2021-08-08 |
not yet calculated |
CVE-2020-36472
MISC
MISC |
rust — rust
|
An issue was discovered in the tokio crate before 1.8.1 for Rust. Upon a JoinHandle::abort, a Task may be dropped in the wrong thread. |
2021-08-08 |
not yet calculated |
CVE-2021-38191
MISC
MISC |
rust — rust
|
An issue was discovered in the actix-http crate before 3.0.0-beta.9 for Rust. HTTP/1 request smuggling (aka HRS) can occur, potentially leading to credential disclosure. |
2021-08-10 |
not yet calculated |
CVE-2021-38512
MISC
MISC |
rust — rust
|
An issue was discovered in the heapless crate before 0.6.1 for Rust. The IntoIter Clone implementation clones an entire underlying Vec without considering whether it has already been partially consumed. |
2021-08-08 |
not yet calculated |
CVE-2020-36464
MISC
MISC |
rust — rust
|
An issue was discovered in the generic-array crate before 0.13.3 for Rust. It violates soundness by using the arr! macro to extend lifetimes. |
2021-08-08 |
not yet calculated |
CVE-2020-36465
MISC
MISC |
rust — rust
|
An issue was discovered in the cgc crate through 2020-12-10 for Rust. Ptr implements Send and Sync for all types. |
2021-08-08 |
not yet calculated |
CVE-2020-36466
MISC
MISC |
rust — rust
|
An issue was discovered in the cgc crate through 2020-12-10 for Rust. Ptr::get returns more than one mutable reference to the same object. |
2021-08-08 |
not yet calculated |
CVE-2020-36467
MISC
MISC |
rust — rust
|
An issue was discovered in the cgc crate through 2020-12-10 for Rust. Ptr::write performs non-atomic write operations on an underlying pointer. |
2021-08-08 |
not yet calculated |
CVE-2020-36468
MISC
MISC |
rust — rust
|
An issue was discovered in the prost-types crate before 0.8.0 for Rust. An overflow can occur during conversion from Timestamp to SystemTime. |
2021-08-08 |
not yet calculated |
CVE-2021-38192
MISC
MISC |
rust — rust
|
An issue was discovered in the generator crate before 0.7.0 for Rust. It does not ensure that a function (for yielding values) has Send bounds. |
2021-08-08 |
not yet calculated |
CVE-2020-36471
MISC
MISC |
rust — rust
|
An issue was discovered in the nalgebra crate before 0.27.1 for Rust. It allows out-of-bounds memory access because it does not ensure that the number of elements is equal to the product of the row count and column count. |
2021-08-08 |
not yet calculated |
CVE-2021-38190
MISC
MISC |
rust — rust
|
An issue was discovered in the tar crate before 0.4.36 for Rust. When symlinks are present in a TAR archive, extraction can create arbitrary directories via .. traversal. |
2021-08-10 |
not yet calculated |
CVE-2021-38511
MISC
MISC |
rust — rust
|
An issue was discovered in the disrustor crate through 2020-12-17 for Rust. RingBuffer doe not properly limit the number of mutable references. |
2021-08-08 |
not yet calculated |
CVE-2020-36470
MISC
MISC |
rust — rust
|
An issue was discovered in the anymap crate through 0.12.1 for Rust. It violates soundness via conversion of a *u8 to a *u64. |
2021-08-08 |
not yet calculated |
CVE-2021-38187
MISC
MISC |
rust — rust
|
An issue was discovered in the better-macro crate through 2021-07-22 for Rust. It intentionally demonstrates that remote attackers can execute arbitrary code via proc-macros, and otherwise has no legitimate purpose. |
2021-08-08 |
not yet calculated |
CVE-2021-38196
MISC
MISC |
rust — rust
|
An issue was discovered in the iced-x86 crate through 1.10.3 for Rust. In Decoder::new(), slice.get_unchecked(slice.length()) is used unsafely. |
2021-08-08 |
not yet calculated |
CVE-2021-38188
MISC
MISC |
rust — rust
|
An issue was discovered in the ark-r1cs-std crate before 0.3.1 for Rust. It does not enforce any constraints in the FieldVar::mul_by_inverse method. Thus, a prover can produce a proof that is unsound but is nonetheless verified. |
2021-08-08 |
not yet calculated |
CVE-2021-38194
MISC
MISC |
rust — rust
|
An issue was discovered in the ammonia crate before 3.1.0 for Rust. XSS can occur because the parsing differences for HTML, SVG, and MathML are mishandled, a similar issue to CVE-2020-26870. |
2021-08-08 |
not yet calculated |
CVE-2021-38193
MISC
MISC |
rust — rust
|
An issue was discovered in the lettre crate before 0.9.6 for Rust. In an e-mail message body, an attacker can place a . character after two <CR><LF> sequences and then inject arbitrary SMTP commands. |
2021-08-08 |
not yet calculated |
CVE-2021-38189
MISC
MISC |
sap — businessobjects_edge
|
SAP BusinessObjects Edge 4.1 allows remote attackers to obtain the SI_PLATFORM_SEARCH_SERVER_LOGON_TOKEN token and consequently gain SYSTEM privileges via vectors involving CORBA calls, aka SAP Note 2039905. |
2021-08-09 |
not yet calculated |
CVE-2014-9320
MISC
MISC
MISC
MISC
MISC |
sap — mobile_platform
|
SAP Mobile Platform 3.0 SP05 ClientHub allows attackers to obtain the keystream and other sensitive information via the DataVault, aka SAP Security Note 2094830. |
2021-08-09 |
not yet calculated |
CVE-2015-7731
MISC
MISC |
sap — netweaver_knowledge_management
|
SAP NetWeaver Knowledge Management allows remote attackers to redirect users to arbitrary websites and conduct phishing attacks via a URL stored in a component. This could enable the attacker to compromise the user’s confidentiality and integrity. |
2021-08-10 |
not yet calculated |
CVE-2021-33707
MISC
MISC |
sapphireims — sapphireims
|
In SapphireIMS 5.0, there is no CSRF token present in the entire application. This can lead to CSRF vulnerabilities in critical application forms like account resent. |
2021-08-11 |
not yet calculated |
CVE-2020-25562
MISC
MISC |
sapphireims — sapphireims
|
In SapphireIMS 5.0, it is possible to take over an account by sending a request to the Save_Password form as shown in POC. Notice that we do not require a JSESSIONID in this request and can reset any user’s password by changing the username to that user and password to base64(desired password). |
2021-08-11 |
not yet calculated |
CVE-2020-25566
MISC
MISC |
sapphireims — sapphireims
|
In SapphireIMS 5.0, it is possible to create local administrator on any client with credentials of a non-privileged user by directly accessing RemoteMgmtTaskSave (Automation Tasks) feature. |
2021-08-11 |
not yet calculated |
CVE-2020-25564
MISC
MISC |
sapphireims — sapphireims
|
In SapphireIMS 5.0, it is possible to use the hardcoded credential in clients (username: sapphire, password: ims) and gain access to the portal. Once the access is available, the attacker can inject malicious OS commands on “ping”, “traceroute” and “snmp” functions and execute code on the server. |
2021-08-11 |
not yet calculated |
CVE-2020-25565
MISC
MISC |
sapphireims — sapphireims
|
In SapphireIMS 4097_1, the password in the database is stored in Base64 format. |
2021-08-11 |
not yet calculated |
CVE-2017-16632
MISC
MISC |
sapphireims — sapphireims
|
SapphireIMS 5 utilized default sapphire:ims credentials to connect the client to server. This credential is saved in ServerConf.config file in the client. |
2021-08-11 |
not yet calculated |
CVE-2020-25561
MISC
MISC |
sapphireims — sapphireims
|
In SapphireIMS 5.0, it is possible to use the hardcoded credential in clients (username: sapphire, password: ims) and gain access to the portal. Once the access is available, the attacker can inject malicious OS commands on “ping”, “traceroute” and “snmp” functions and execute code on the server. We also observed the same is true if the JSESSIONID is completely removed. |
2021-08-11 |
not yet calculated |
CVE-2020-25560
MISC
MISC |
sapphireims — sapphireims
|
In SapphireIMS 4097_1, a guest user is able to change the password of an administrative user by utilizing an Insecure Direct Object Reference (IDOR) in the “Account Password Reset” functionality. |
2021-08-11 |
not yet calculated |
CVE-2017-16631
MISC
MISC |
sapphireims — sapphireims
|
In SapphireIMS 4097_1, a guest user can create a local administrator account on any system that has SapphireIMS installed, because of an Insecure Direct Object Reference (IDOR) in the local user creation function. |
2021-08-11 |
not yet calculated |
CVE-2017-16630
MISC
MISC |
sapphireims — sapphireims
|
In SapphireIMS 5.0, it is possible to create local administrator on any client without requiring any credentials by directly accessing RemoteMgmtTaskSave (Automation Tasks) feature and not having a JSESSIONID. |
2021-08-11 |
not yet calculated |
CVE-2020-25563
MISC
MISC |
sas — admin_portal
|
The SAS Admin portal of Mitel MiCollab before 9.2 FP2 could allow an unauthenticated attacker to access (view and modify) user data by injecting arbitrary directory paths due to improper URL validation, aka Directory Traversal. |
2021-08-13 |
not yet calculated |
CVE-2021-27402
MISC
CONFIRM |
scada — scada
|
The affected product is vulnerable to a stack-based buffer overflow, which may allow an attacker to remotely execute arbitrary code on the WebAccess/SCADA (WebAccess/SCADA versions prior to 8.4.5, WebAccess/SCADA versions prior to 9.0.1). |
2021-08-10 |
not yet calculated |
CVE-2021-32943
MISC |
servicecomb — servicecenter_directory
|
Improper configuration will cause ServiceComb ServiceCenter Directory Traversal problem in ServcieCenter 1.x.x versions and fixed in 2.0.0. |
2021-08-10 |
not yet calculated |
CVE-2021-21501
MISC
MLIST |
severless — offline
|
Serverless Offline 8.0.0 returns a 403 HTTP status code for a route that has a trailing / character, which might cause a developer to implement incorrect access control, because the actual behavior within the Amazon AWS environment is a 200 HTTP status code (i.e., possibly greater than expected permissions). |
2021-08-10 |
not yet calculated |
CVE-2021-38384
MISC |
siemens — automation_ license_manager
|
A vulnerability has been identified in Automation License Manager 5 (All versions), Automation License Manager 6 (All versions < V6.0 SP9 Update 2). Sending specially crafted packets to port 4410/tcp of an affected system could lead to extensive memory being consumed and as such could cause a denial-of-service preventing legitimate users from using the system. |
2021-08-10 |
not yet calculated |
CVE-2021-25659
MISC |
simatic — multiple_devices
|
A vulnerability has been identified in SIMATIC Drive Controller family (All versions < V2.9.2), SIMATIC ET 200SP Open Controller CPU 1515SP PC2 (incl. SIPLUS variants) (All versions), SIMATIC S7 PLCSIM Advanced (All versions > V2 < V4), SIMATIC S7-1200 CPU family (incl. SIPLUS variants) (Version V4.4), SIMATIC S7-1500 CPU family (incl. related ET200 CPUs and SIPLUS variants) (All versions > V2.5 < V2.9.2), SIMATIC S7-1500 Software Controller (All versions > V2.5), TIM 1531 IRC (incl. SIPLUS NET variants) (Version V2.1). Due to an incorrect authorization check in the affected component, an attacker could extract information about access protected PLC program variables over port 102/tcp from an affected device when reading multiple attributes at once. |
2021-08-10 |
not yet calculated |
CVE-2020-28397
MISC |
simatic — s7-1200
|
A vulnerability has been identified in SIMATIC S7-1200 CPU family (incl. SIPLUS variants) (V4.5.0). Affected devices fail to authenticate against configured passwords when provisioned using TIA Portal V13. This could allow an attacker using TIA Portal V17 or later versions to bypass authentication and download arbitrary programs to the PLC. The vulnerability does not occur when TIA Portal V13 SP1 or any later version was used to provision the device. |
2021-08-10 |
not yet calculated |
CVE-2021-37172
MISC |
sinec — nms
|
A vulnerability has been identified in SINEC NMS (All versions < V1.0 SP2). The affected application incorrectly neutralizes special elements when creating batch operations which could lead to command injection. An authenticated remote attacker with administrative privileges could exploit this vulnerability to execute arbitrary code on the system with system privileges. |
2021-08-10 |
not yet calculated |
CVE-2021-33721
MISC |
sitecore — sitecore
|
Sitecore through 10.1, when Update Center is enabled, allows remote authenticated users to upload arbitrary files and achieve remote code execution by visiting an uploaded .aspx file at an admin/Packages URL. |
2021-08-12 |
not yet calculated |
CVE-2021-38366
MISC |
solid_edge — se2021
|
A vulnerability has been identified in Solid Edge SE2021 (All Versions < SE2021MP7). The PSKERNEL.dll library in affected application lacks proper validation while parsing user-supplied OBJ files that could lead to a use-after-free condition. An attacker could leverage this vulnerability to execute code in the context of the current process. (ZDI-CAN-13777) |
2021-08-10 |
not yet calculated |
CVE-2021-37179
MISC |
solid_edge — se2021
|
A vulnerability has been identified in Solid Edge SE2021 (All Versions < SE2021MP7). An XML external entity injection vulnerability in the underlying XML parser could cause the affected application to disclose arbitrary files to remote attackers by loading a specially crafted xml file. |
2021-08-10 |
not yet calculated |
CVE-2021-37178
MISC |
solid_edge — se2021
|
A vulnerability has been identified in Solid Edge SE2021 (All Versions < SE2021MP7). The PSKERNEL.dll library lacks proper validation while parsing user-supplied OBJ files that could cause an out of bounds access to an uninitialized pointer. An attacker could leverage this vulnerability to execute code in the context of the current process. (ZDI-CAN-13775) |
2021-08-10 |
not yet calculated |
CVE-2021-37180
MISC |
sonatype — nexus_repository_manager
|
Multiple XSS issues exist in Sonatype Nexus Repository Manager 3 before 3.33.0. An authenticated attacker with the ability to add HTML files to a repository could redirect users to Nexus Repository Manager’s pages with code modifications. |
2021-08-10 |
not yet calculated |
CVE-2021-37152
MISC
MISC |
sonicwall — analytics
|
SonicWall Analytics 2.5 On-Prem is vulnerable to Java Debug Wire Protocol (JDWP) interface security misconfiguration vulnerability which potentially leads to Remote Code Execution. This vulnerability impacts Analytics On-Prem 2.5.2518 and earlier. |
2021-08-10 |
not yet calculated |
CVE-2021-20032
CONFIRM |
sony — srs-xb33_and_srs-xb43_devices
|
Sony SRS-XB33 and SRS-XB43 devices through 2021-08-09 allow remote attackers to recover speech signals from an LED on the device, via a telescope and an electro-optical sensor, aka a “Glowworm” attack. The power indicator LED of the speakers is connected directly to the power line, as a result, the intensity of a device’s power indicator LED is correlative to the power consumption. The sound played by the speakers affects their power consumption and as a result is also correlative to the light intensity of the LEDs. By analyzing measurements obtained from an electro-optical sensor directed at the power indicator LEDs of the speakers, we can recover the sound played by them. |
2021-08-11 |
not yet calculated |
CVE-2021-38544
MISC |
sunhillo — sureline
|
Sunhillo SureLine before 8.7.0.1.1 allows Unauthenticated OS Command Injection via shell metacharacters in ipAddr or dnsAddr /cgi/networkDiag.cgi. |
2021-08-13 |
not yet calculated |
CVE-2021-36380
MISC
MISC |
| tensorflow — tensorflow |
TensorFlow is an end-to-end open source platform for machine learning. In affected versions providing a negative element to `num_elements` list argument of `tf.raw_ops.TensorListReserve` causes the runtime to abort the process due to reallocating a `std::vector` to have a negative number of elements. The [implementation](https://github.com/tensorflow/tensorflow/blob/8d72537c6abf5a44103b57b9c2e22c14f5f49698/tensorflow/core/kernels/list_kernels.cc#L312) calls `std::vector.resize()` with the new size controlled by input given by the user, without checking that this input is valid. We have patched the issue in GitHub commit 8a6e874437670045e6c7dc6154c7412b4a2135e2. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37644
CONFIRM
MISC |
| tensorflow — tensorflow |
TensorFlow is an end-to-end open source platform for machine learning. In affected versions an attacker can read from outside of bounds of heap allocated data by sending specially crafted illegal arguments to `tf.raw_ops.UpperBound`. The [implementation](https://github.com/tensorflow/tensorflow/blob/460e000de3a83278fb00b61a16d161b1964f15f4/tensorflow/core/kernels/searchsorted_op.cc#L85-L104) does not validate the rank of `sorted_input` argument. A similar issue occurs in `tf.raw_ops.LowerBound`. We have patched the issue in GitHub commit 42459e4273c2e47a3232cc16c4f4fff3b3a35c38. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37670
MISC
CONFIRM |
| tensorflow — tensorflow |
TensorFlow is an end-to-end open source platform for machine learning. The code for `tf.raw_ops.UncompressElement` can be made to trigger a null pointer dereference. The [implementation](https://github.com/tensorflow/tensorflow/blob/f24faa153ad31a4b51578f8181d3aaab77a1ddeb/tensorflow/core/kernels/data/experimental/compression_ops.cc#L50-L53) obtains a pointer to a `CompressedElement` from a `Variant` tensor and then proceeds to dereference it for decompressing. There is no check that the `Variant` tensor contained a `CompressedElement`, so the pointer is actually `nullptr`. We have patched the issue in GitHub commit 7bdf50bb4f5c54a4997c379092888546c97c3ebd. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37649
MISC
CONFIRM |
| tensorflow — tensorflow |
TensorFlow is an end-to-end open source platform for machine learning. In affected versions the implementation for `tf.raw_ops.FractionalAvgPoolGrad` can be tricked into accessing data outside of bounds of heap allocated buffers. The [implementation](https://github.com/tensorflow/tensorflow/blob/f24faa153ad31a4b51578f8181d3aaab77a1ddeb/tensorflow/core/kernels/fractional_avg_pool_op.cc#L205) does not validate that the input tensor is non-empty. Thus, code constructs an empty `EigenDoubleMatrixMap` and then accesses this buffer with indices that are outside of the empty area. We have patched the issue in GitHub commit 0f931751fb20f565c4e94aa6df58d54a003cdb30. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37651
CONFIRM
MISC |
| tensorflow — tensorflow |
TensorFlow is an end-to-end open source platform for machine learning. In affected versions the shape inference code for `tf.raw_ops.Dequantize` has a vulnerability that could trigger a denial of service via a segfault if an attacker provides invalid arguments. The shape inference [implementation](https://github.com/tensorflow/tensorflow/blob/460e000de3a83278fb00b61a16d161b1964f15f4/tensorflow/core/ops/array_ops.cc#L2999-L3014) uses `axis` to select between two different values for `minmax_rank` which is then used to retrieve tensor dimensions. However, code assumes that `axis` can be either `-1` or a value greater than `-1`, with no validation for the other values. We have patched the issue in GitHub commit da857cfa0fde8f79ad0afdbc94e88b5d4bbec764. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37677
CONFIRM
MISC |
| tensorflow — tensorflow |
TensorFlow is an end-to-end open source platform for machine learning. When a user does not supply arguments that determine a valid sparse tensor, `tf.raw_ops.SparseTensorSliceDataset` implementation can be made to dereference a null pointer. The [implementation](https://github.com/tensorflow/tensorflow/blob/8d72537c6abf5a44103b57b9c2e22c14f5f49698/tensorflow/core/kernels/data/sparse_tensor_slice_dataset_op.cc#L240-L251) has some argument validation but fails to consider the case when either `indices` or `values` are provided for an empty sparse tensor when the other is not. If `indices` is empty, then [code that performs validation](https://github.com/tensorflow/tensorflow/blob/8d72537c6abf5a44103b57b9c2e22c14f5f49698/tensorflow/core/kernels/data/sparse_tensor_slice_dataset_op.cc#L260-L261) (i.e., checking that the indices are monotonically increasing) results in a null pointer dereference. If `indices` as provided by the user is empty, then `indices` in the C++ code above is backed by an empty `std::vector`, hence calling `indices->dim_size(0)` results in null pointer dereferencing (same as calling `std::vector::at()` on an empty vector). We have patched the issue in GitHub commit 02cc160e29d20631de3859c6653184e3f876b9d7. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37647
CONFIRM
MISC |
| tensorflow — tensorflow |
TensorFlow is an end-to-end open source platform for machine learning. In affected versions due to incomplete validation in MKL implementation of requantization, an attacker can trigger undefined behavior via binding a reference to a null pointer or can access data outside the bounds of heap allocated arrays. The [implementation](https://github.com/tensorflow/tensorflow/blob/460e000de3a83278fb00b61a16d161b1964f15f4/tensorflow/core/kernels/mkl/mkl_requantization_range_per_channel_op.cc) does not validate the dimensions of the `input` tensor. A similar issue occurs in `MklRequantizePerChannelOp`. The [implementation](https://github.com/tensorflow/tensorflow/blob/460e000de3a83278fb00b61a16d161b1964f15f4/tensorflow/core/kernels/mkl/mkl_requantize_per_channel_op.cc) does not perform full validation for all the input arguments. We have patched the issue in GitHub commit 9e62869465573cb2d9b5053f1fa02a81fce21d69 and in the Github commit 203214568f5bc237603dbab6e1fd389f1572f5c9. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37665
MISC
CONFIRM
MISC |
| tensorflow — tensorflow |
TensorFlow is an end-to-end open source platform for machine learning. In affected versions an attacker can cause undefined behavior via binding a reference to null pointer in `tf.raw_ops.RaggedTensorToVariant`. The [implementation](https://github.com/tensorflow/tensorflow/blob/460e000de3a83278fb00b61a16d161b1964f15f4/tensorflow/core/kernels/ragged_tensor_to_variant_op.cc#L129) has an incomplete validation of the splits values, missing the case when the argument would be empty. We have patched the issue in GitHub commit be7a4de6adfbd303ce08be4332554dff70362612. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37666
MISC
CONFIRM |
| tensorflow — tensorflow |
TensorFlow is an end-to-end open source platform for machine learning. In affected versions the strided slice implementation in TFLite has a logic bug which can allow an attacker to trigger an infinite loop. This arises from newly introduced support for [ellipsis in axis definition](https://github.com/tensorflow/tensorflow/blob/149562d49faa709ea80df1d99fc41d005b81082a/tensorflow/lite/kernels/strided_slice.cc#L103-L122). An attacker can craft a model such that `ellipsis_end_idx` is smaller than `i` (e.g., always negative). In this case, the inner loop does not increase `i` and the `continue` statement causes execution to skip over the preincrement at the end of the outer loop. We have patched the issue in GitHub commit dfa22b348b70bb89d6d6ec0ff53973bacb4f4695. TensorFlow 2.6.0 is the only affected version. |
2021-08-12 |
not yet calculated |
CVE-2021-37686
CONFIRM
MISC |
| tensorflow — tensorflow |
TensorFlow is an end-to-end open source platform for machine learning. In affected versions TFLite’s [`GatherNd` implementation](https://github.com/tensorflow/tensorflow/blob/149562d49faa709ea80df1d99fc41d005b81082a/tensorflow/lite/kernels/gather_nd.cc#L124) does not support negative indices but there are no checks for this situation. Hence, an attacker can read arbitrary data from the heap by carefully crafting a model with negative values in `indices`. Similar issue exists in [`Gather` implementation](https://github.com/tensorflow/tensorflow/blob/149562d49faa709ea80df1d99fc41d005b81082a/tensorflow/lite/kernels/gather.cc). We have patched the issue in GitHub commits bb6a0383ed553c286f87ca88c207f6774d5c4a8f and eb921122119a6b6e470ee98b89e65d721663179d. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37687
MISC
MISC
CONFIRM |
| tensorflow — tensorflow |
TensorFlow is an end-to-end open source platform for machine learning. In affected versions the implementation of `tf.raw_ops.QuantizeAndDequantizeV4Grad` is vulnerable to an integer overflow issue caused by converting a signed integer value to an unsigned one and then allocating memory based on this value. The [implementation](https://github.com/tensorflow/tensorflow/blob/8d72537c6abf5a44103b57b9c2e22c14f5f49698/tensorflow/core/kernels/quantize_and_dequantize_op.cc#L126) uses the `axis` value as the size argument to `absl::InlinedVector` constructor. But, the constructor uses an unsigned type for the argument, so the implicit conversion transforms the negative value to a large integer. We have patched the issue in GitHub commit 96f364a1ca3009f98980021c4b32be5fdcca33a1. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, and TensorFlow 2.4.3, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37645
CONFIRM
MISC |
| tensorflow — tensorflow |
TensorFlow is an end-to-end open source platform for machine learning. In affected versions an attacker can cause undefined behavior via binding a reference to null pointer in `tf.raw_ops.UnicodeEncode`. The [implementation](https://github.com/tensorflow/tensorflow/blob/460e000de3a83278fb00b61a16d161b1964f15f4/tensorflow/core/kernels/unicode_ops.cc#L533-L539) reads the first dimension of the `input_splits` tensor before validating that this tensor is not empty. We have patched the issue in GitHub commit 2e0ee46f1a47675152d3d865797a18358881d7a6. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37667
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. If a user does not provide a valid padding value to `tf.raw_ops.MatrixDiagPartOp`, then the code triggers a null pointer dereference (if input is empty) or produces invalid behavior, ignoring all values after the first. The [implementation](https://github.com/tensorflow/tensorflow/blob/8d72537c6abf5a44103b57b9c2e22c14f5f49698/tensorflow/core/kernels/linalg/matrix_diag_op.cc#L89) reads the first value from a tensor buffer without first checking that the tensor has values to read from. We have patched the issue in GitHub commit 482da92095c4d48f8784b1f00dda4f81c28d2988. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37643
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. Sending invalid argument for `row_partition_types` of `tf.raw_ops.RaggedTensorToTensor` API results in a null pointer dereference and undefined behavior. The [implementation](https://github.com/tensorflow/tensorflow/blob/47a06f40411a69c99f381495f490536972152ac0/tensorflow/core/kernels/ragged_tensor_to_tensor_op.cc#L328) accesses the first element of a user supplied list of values without validating that the provided list is not empty. We have patched the issue in GitHub commit 301ae88b331d37a2a16159b65b255f4f9eb39314. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37638
CONFIRM
MISC |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions under certain conditions, Go code can trigger a segfault in string deallocation. For string tensors, `C.TF_TString_Dealloc` is called during garbage collection within a finalizer function. However, tensor structure isn’t checked until encoding to avoid a performance penalty. The current method for dealloc assumes that encoding succeeded, but segfaults when a string tensor is garbage collected whose encoding failed (e.g., due to mismatched dimensions). To fix this, the call to set the finalizer function is deferred until `NewTensor` returns and, if encoding failed for a string tensor, deallocs are determined based on bytes written. We have patched the issue in GitHub commit 8721ba96e5760c229217b594f6d2ba332beedf22. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, which is the other affected version. |
2021-08-12 |
not yet calculated |
CVE-2021-37692
MISC
CONFIRM
MISC |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions an attacker can craft a TFLite model that would trigger a division by zero error in LSH [implementation](https://github.com/tensorflow/tensorflow/blob/149562d49faa709ea80df1d99fc41d005b81082a/tensorflow/lite/kernels/lsh_projection.cc#L118). We have patched the issue in GitHub commit 0575b640091680cfb70f4dd93e70658de43b94f9. The fix will be included in TensorFlow 2.6.0. We will also cherrypick thiscommit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37691
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions the implementation of sparse reduction operations in TensorFlow can trigger accesses outside of bounds of heap allocated data. The [implementation](https://github.com/tensorflow/tensorflow/blob/a1bc56203f21a5a4995311825ffaba7a670d7747/tensorflow/core/kernels/sparse_reduce_op.cc#L217-L228) fails to validate that each reduction group does not overflow and that each corresponding index does not point to outside the bounds of the input tensor. We have patched the issue in GitHub commit 87158f43f05f2720a374f3e6d22a7aaa3a33f750. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37635
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions the implementation of `tf.raw_ops.SparseDenseCwiseDiv` is vulnerable to a division by 0 error. The [implementation](https://github.com/tensorflow/tensorflow/blob/a1bc56203f21a5a4995311825ffaba7a670d7747/tensorflow/core/kernels/sparse_dense_binary_op_shared.cc#L56) uses a common class for all binary operations but fails to treat the division by 0 case separately. We have patched the issue in GitHub commit d9204be9f49520cdaaeb2541d1dc5187b23f31d9. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37636
CONFIRM
MISC |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions when running shape functions, some functions (such as `MutableHashTableShape`) produce extra output information in the form of a `ShapeAndType` struct. The shapes embedded in this struct are owned by an inference context that is cleaned up almost immediately; if the upstream code attempts to access this shape information, it can trigger a segfault. `ShapeRefiner` is mitigating this for normal output shapes by cloning them (and thus putting the newly created shape under ownership of an inference context that will not die), but we were not doing the same for shapes and types. This commit fixes that by doing similar logic on output shapes and types. We have patched the issue in GitHub commit ee119d4a498979525046fba1c3dd3f13a039fbb1. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-13 |
not yet calculated |
CVE-2021-37690
CONFIRM
MISC |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions an attacker can craft a TFLite model that would trigger a null pointer dereference, which would result in a crash and denial of service. This is caused by the MLIR optimization of `L2NormalizeReduceAxis` operator. The [implementation](https://github.com/tensorflow/tensorflow/blob/149562d49faa709ea80df1d99fc41d005b81082a/tensorflow/compiler/mlir/lite/transforms/optimize.cc#L67-L70) unconditionally dereferences a pointer to an iterator to a vector without checking that the vector has elements. We have patched the issue in GitHub commit d6b57f461b39fd1aa8c1b870f1b974aac3554955. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37689
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions an attacker can cause undefined behavior via binding a reference to null pointer in `tf.raw_ops.SparseFillEmptyRows`. The shape inference [implementation](https://github.com/tensorflow/tensorflow/blob/460e000de3a83278fb00b61a16d161b1964f15f4/tensorflow/core/ops/sparse_ops.cc#L608-L634) does not validate that the input arguments are not empty tensors. We have patched the issue in GitHub commit 578e634b4f1c1c684d4b4294f9e5281b2133b3ed. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37676
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions an attacker can craft a TFLite model that would trigger a null pointer dereference, which would result in a crash and denial of service. The [implementation](https://github.com/tensorflow/tensorflow/blob/149562d49faa709ea80df1d99fc41d005b81082a/tensorflow/lite/kernels/internal/optimized/optimized_ops.h#L268-L285) unconditionally dereferences a pointer. We have patched the issue in GitHub commit 15691e456c7dc9bd6be203b09765b063bf4a380c. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37688
CONFIRM
MISC |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions TensorFlow and Keras can be tricked to perform arbitrary code execution when deserializing a Keras model from YAML format. The [implementation](https://github.com/tensorflow/tensorflow/blob/460e000de3a83278fb00b61a16d161b1964f15f4/tensorflow/python/keras/saving/model_config.py#L66-L104) uses `yaml.unsafe_load` which can perform arbitrary code execution on the input. Given that YAML format support requires a significant amount of work, we have removed it for now. We have patched the issue in GitHub commit 23d6383eb6c14084a8fc3bdf164043b974818012. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37678
CONFIRM
MISC |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions the implementations of pooling in TFLite are vulnerable to division by 0 errors as there are no checks for divisors not being 0. We have patched the issue in GitHub commit [dfa22b348b70bb89d6d6ec0ff53973bacb4f4695](https://github.com/tensorflow/tensorflow/commit/dfa22b348b70bb89d6d6ec0ff53973bacb4f4695). The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37684
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions the implementation of `tf.raw_ops.SparseReshape` can be made to trigger an integral division by 0 exception. The [implementation](https://github.com/tensorflow/tensorflow/blob/8d72537c6abf5a44103b57b9c2e22c14f5f49698/tensorflow/core/kernels/reshape_util.cc#L176-L181) calls the reshaping functor whenever there is at least an index in the input but does not check that shape of the input or the target shape have both a non-zero number of elements. The [reshape functor](https://github.com/tensorflow/tensorflow/blob/8d72537c6abf5a44103b57b9c2e22c14f5f49698/tensorflow/core/kernels/reshape_util.cc#L40-L78) blindly divides by the dimensions of the target shape. Hence, if this is not checked, code will result in a division by 0. We have patched the issue in GitHub commit 4923de56ec94fff7770df259ab7f2288a74feb41. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1 as this is the other affected version. |
2021-08-12 |
not yet calculated |
CVE-2021-37640
CONFIRM
MISC |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions if the arguments to `tf.raw_ops.RaggedGather` don’t determine a valid ragged tensor code can trigger a read from outside of bounds of heap allocated buffers. The [implementation](https://github.com/tensorflow/tensorflow/blob/8d72537c6abf5a44103b57b9c2e22c14f5f49698/tensorflow/core/kernels/ragged_gather_op.cc#L70) directly reads the first dimension of a tensor shape before checking that said tensor has rank of at least 1 (i.e., it is not a scalar). Furthermore, the implementation does not check that the list given by `params_nested_splits` is not an empty list of tensors. We have patched the issue in GitHub commit a2b743f6017d7b97af1fe49087ae15f0ac634373. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37641
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions the implementation of division in TFLite is [vulnerable to a division by 0 error](https://github.com/tensorflow/tensorflow/blob/460e000de3a83278fb00b61a16d161b1964f15f4/tensorflow/lite/kernels/div.cc). There is no check that the divisor tensor does not contain zero elements. We have patched the issue in GitHub commit 1e206baedf8bef0334cca3eb92bab134ef525a28. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37683
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions the code for `tf.raw_ops.SaveV2` does not properly validate the inputs and an attacker can trigger a null pointer dereference. The [implementation](https://github.com/tensorflow/tensorflow/blob/8d72537c6abf5a44103b57b9c2e22c14f5f49698/tensorflow/core/kernels/save_restore_v2_ops.cc) uses `ValidateInputs` to check that the input arguments are valid. This validation would have caught the illegal state represented by the reproducer above. However, the validation uses `OP_REQUIRES` which translates to setting the `Status` object of the current `OpKernelContext` to an error status, followed by an empty `return` statement which just terminates the execution of the function it is present in. However, this does not mean that the kernel execution is finalized: instead, execution continues from the next line in `Compute` that follows the call to `ValidateInputs`. This is equivalent to lacking the validation. We have patched the issue in GitHub commit 9728c60e136912a12d99ca56e106b7cce7af5986. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37648
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. When restoring tensors via raw APIs, if the tensor name is not provided, TensorFlow can be tricked into dereferencing a null pointer. Alternatively, attackers can read memory outside the bounds of heap allocated data by providing some tensor names but not enough for a successful restoration. The [implementation](https://github.com/tensorflow/tensorflow/blob/47a06f40411a69c99f381495f490536972152ac0/tensorflow/core/kernels/save_restore_tensor.cc#L158-L159) retrieves the tensor list corresponding to the `tensor_name` user controlled input and immediately retrieves the tensor at the restoration index (controlled via `preferred_shard` argument). This occurs without validating that the provided list has enough values. If the list is empty this results in dereferencing a null pointer (undefined behavior). If, however, the list has some elements, if the restoration index is outside the bounds this results in heap OOB read. We have patched the issue in GitHub commit 9e82dce6e6bd1f36a57e08fa85af213e2b2f2622. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37639
CONFIRM
MISC |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions it is possible to nest a `tf.map_fn` within another `tf.map_fn` call. However, if the input tensor is a `RaggedTensor` and there is no function signature provided, code assumes the output is a fully specified tensor and fills output buffer with uninitialized contents from the heap. The `t` and `z` outputs should be identical, however this is not the case. The last row of `t` contains data from the heap which can be used to leak other memory information. The bug lies in the conversion from a `Variant` tensor to a `RaggedTensor`. The [implementation](https://github.com/tensorflow/tensorflow/blob/460e000de3a83278fb00b61a16d161b1964f15f4/tensorflow/core/kernels/ragged_tensor_from_variant_op.cc#L177-L190) does not check that all inner shapes match and this results in the additional dimensions. The same implementation can result in data loss, if input tensor is tweaked. We have patched the issue in GitHub commit 4e2565483d0ffcadc719bd44893fb7f609bb5f12. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37679
CONFIRM
MISC |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions the implementation of fully connected layers in TFLite is [vulnerable to a division by zero error](https://github.com/tensorflow/tensorflow/blob/460e000de3a83278fb00b61a16d161b1964f15f4/tensorflow/lite/kernels/fully_connected.cc#L226). We have patched the issue in GitHub commit 718721986aa137691ee23f03638867151f74935f. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37680
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions the implementation of SVDF in TFLite is [vulnerable to a null pointer error](https://github.com/tensorflow/tensorflow/blob/460e000de3a83278fb00b61a16d161b1964f15f4/tensorflow/lite/kernels/svdf.cc#L300-L313). The [`GetVariableInput` function](https://github.com/tensorflow/tensorflow/blob/460e000de3a83278fb00b61a16d161b1964f15f4/tensorflow/lite/kernels/kernel_util.cc#L115-L119) can return a null pointer but `GetTensorData` assumes that the argument is always a valid tensor. Furthermore, because `GetVariableInput` calls [`GetMutableInput`](https://github.com/tensorflow/tensorflow/blob/460e000de3a83278fb00b61a16d161b1964f15f4/tensorflow/lite/kernels/kernel_util.cc#L82-L90) which might return `nullptr`, the `tensor->is_variable` expression can also trigger a null pointer exception. We have patched the issue in GitHub commit 5b048e87e4e55990dae6b547add4dae59f4e1c76. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37681
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions all TFLite operations that use quantization can be made to use unitialized values. [For example](https://github.com/tensorflow/tensorflow/blob/460e000de3a83278fb00b61a16d161b1964f15f4/tensorflow/lite/kernels/depthwise_conv.cc#L198-L200). The issue stems from the fact that `quantization.params` is only valid if `quantization.type` is different that `kTfLiteNoQuantization`. However, these checks are missing in large parts of the code. We have patched the issue in GitHub commits 537bc7c723439b9194a358f64d871dd326c18887, 4a91f2069f7145aab6ba2d8cfe41be8a110c18a5 and 8933b8a21280696ab119b63263babdb54c298538. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37682
MISC
MISC
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions TFLite’s [`expand_dims.cc`](https://github.com/tensorflow/tensorflow/blob/149562d49faa709ea80df1d99fc41d005b81082a/tensorflow/lite/kernels/expand_dims.cc#L36-L50) contains a vulnerability which allows reading one element outside of bounds of heap allocated data. If `axis` is a large negative value (e.g., `-100000`), then after the first `if` it would still be negative. The check following the `if` statement will pass and the `for` loop would read one element before the start of `input_dims.data` (when `i = 0`). We have patched the issue in GitHub commit d94ffe08a65400f898241c0374e9edc6fa8ed257. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37685
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. It is possible to trigger a null pointer dereference in TensorFlow by passing an invalid input to `tf.raw_ops.CompressElement`. The [implementation](https://github.com/tensorflow/tensorflow/blob/47a06f40411a69c99f381495f490536972152ac0/tensorflow/core/data/compression_utils.cc#L34) was accessing the size of a buffer obtained from the return of a separate function call before validating that said buffer is valid. We have patched the issue in GitHub commit 5dc7f6981fdaf74c8c5be41f393df705841fb7c5. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37637
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions the implementation of `tf.raw_ops.ResourceScatterDiv` is vulnerable to a division by 0 error. The [implementation](https://github.com/tensorflow/tensorflow/blob/8d72537c6abf5a44103b57b9c2e22c14f5f49698/tensorflow/core/kernels/resource_variable_ops.cc#L865) uses a common class for all binary operations but fails to treat the division by 0 case separately. We have patched the issue in GitHub commit 4aacb30888638da75023e6601149415b39763d76. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37642
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions an attacker can generate undefined behavior via a reference binding to nullptr in `BoostedTreesCalculateBestGainsPerFeature` and similar attack can occur in `BoostedTreesCalculateBestFeatureSplitV2`. The [implementation](https://github.com/tensorflow/tensorflow/blob/84d053187cb80d975ef2b9684d4b61981bca0c41/tensorflow/core/kernels/boosted_trees/stats_ops.cc) does not validate the input values. We have patched the issue in GitHub commit 9c87c32c710d0b5b53dc6fd3bfde4046e1f7a5ad and in commit 429f009d2b2c09028647dd4bb7b3f6f414bbaad7. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37662
MISC
CONFIRM
MISC |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions an attacker can cause a denial of service in `boosted_trees_create_quantile_stream_resource` by using negative arguments. The [implementation](https://github.com/tensorflow/tensorflow/blob/84d053187cb80d975ef2b9684d4b61981bca0c41/tensorflow/core/kernels/boosted_trees/quantile_ops.cc#L96) does not validate that `num_streams` only contains non-negative numbers. In turn, [this results in using this value to allocate memory](https://github.com/tensorflow/tensorflow/blob/84d053187cb80d975ef2b9684d4b61981bca0c41/tensorflow/core/kernels/boosted_trees/quantiles/quantile_stream_resource.h#L31-L40). However, `reserve` receives an unsigned integer so there is an implicit conversion from a negative value to a large positive unsigned. This results in a crash from the standard library. We have patched the issue in GitHub commit 8a84f7a2b5a2b27ecf88d25bad9ac777cd2f7992. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37661
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions an attacker can cause denial of service in applications serving models using `tf.raw_ops.UnravelIndex` by triggering a division by 0. The [implementation](https://github.com/tensorflow/tensorflow/blob/460e000de3a83278fb00b61a16d161b1964f15f4/tensorflow/core/kernels/unravel_index_op.cc#L36) does not check that the tensor subsumed by `dims` is not empty. Hence, if one element of `dims` is 0, the implementation does a division by 0. We have patched the issue in GitHub commit a776040a5e7ebf76eeb7eb923bf1ae417dd4d233. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37668
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions an attacker can cause denial of service in applications serving models using `tf.raw_ops.NonMaxSuppressionV5` by triggering a division by 0. The [implementation](https://github.com/tensorflow/tensorflow/blob/460e000de3a83278fb00b61a16d161b1964f15f4/tensorflow/core/kernels/image/non_max_suppression_op.cc#L170-L271) uses a user controlled argument to resize a `std::vector`. However, as `std::vector::resize` takes the size argument as a `size_t` and `output_size` is an `int`, there is an implicit conversion to unsigned. If the attacker supplies a negative value, this conversion results in a crash. A similar issue occurs in `CombinedNonMaxSuppression`. We have patched the issue in GitHub commit 3a7362750d5c372420aa8f0caf7bf5b5c3d0f52d and commit [b5cdbf12ffcaaffecf98f22a6be5a64bb96e4f58. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37669
CONFIRM
MISC
MISC |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions an attacker can cause undefined behavior via binding a reference to null pointer in `tf.raw_ops.Map*` and `tf.raw_ops.OrderedMap*` operations. The [implementation](https://github.com/tensorflow/tensorflow/blob/460e000de3a83278fb00b61a16d161b1964f15f4/tensorflow/core/kernels/map_stage_op.cc#L222-L248) has a check in place to ensure that `indices` is in ascending order, but does not check that `indices` is not empty. We have patched the issue in GitHub commit 532f5c5a547126c634fefd43bbad1dc6417678ac. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37671
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions an attacker can read from outside of bounds of heap allocated data by sending specially crafted illegal arguments to `tf.raw_ops.SdcaOptimizerV2`. The [implementation](https://github.com/tensorflow/tensorflow/blob/460e000de3a83278fb00b61a16d161b1964f15f4/tensorflow/core/kernels/sdca_internal.cc#L320-L353) does not check that the length of `example_labels` is the same as the number of examples. We have patched the issue in GitHub commit a4e138660270e7599793fa438cd7b2fc2ce215a6. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37672
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions most implementations of convolution operators in TensorFlow are affected by a division by 0 vulnerability where an attacker can trigger a denial of service via a crash. The shape inference [implementation](https://github.com/tensorflow/tensorflow/blob/460e000de3a83278fb00b61a16d161b1964f15f4/tensorflow/core/framework/common_shape_fns.cc#L577) is missing several validations before doing divisions and modulo operations. We have patched the issue in GitHub commit 8a793b5d7f59e37ac7f3cd0954a750a2fe76bad4. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37675
CONFIRM
MISC |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions an attacker can trigger a denial of service via a `CHECK`-fail in `tf.raw_ops.MapStage`. The [implementation](https://github.com/tensorflow/tensorflow/blob/460e000de3a83278fb00b61a16d161b1964f15f4/tensorflow/core/kernels/map_stage_op.cc#L513) does not check that the `key` input is a valid non-empty tensor. We have patched the issue in GitHub commit d7de67733925de196ec8863a33445b73f9562d1d. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37673
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions due to incomplete validation in `tf.raw_ops.QuantizeV2`, an attacker can trigger undefined behavior via binding a reference to a null pointer or can access data outside the bounds of heap allocated arrays. The [implementation](https://github.com/tensorflow/tensorflow/blob/84d053187cb80d975ef2b9684d4b61981bca0c41/tensorflow/core/kernels/quantize_op.cc#L59) has some validation but does not check that `min_range` and `max_range` both have the same non-zero number of elements. If `axis` is provided (i.e., not `-1`), then validation should check that it is a value in range for the rank of `input` tensor and then the lengths of `min_range` and `max_range` inputs match the `axis` dimension of the `input` tensor. We have patched the issue in GitHub commit 6da6620efad397c85493b8f8667b821403516708. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37663
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions an attacker can read from outside of bounds of heap allocated data by sending specially crafted illegal arguments to `BoostedTreesSparseCalculateBestFeatureSplit`. The [implementation](https://github.com/tensorflow/tensorflow/blob/84d053187cb80d975ef2b9684d4b61981bca0c41/tensorflow/core/kernels/boosted_trees/stats_ops.cc) needs to validate that each value in `stats_summary_indices` is in range. We have patched the issue in GitHub commit e84c975313e8e8e38bb2ea118196369c45c51378. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37664
CONFIRM
MISC |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions an attacker can trigger a denial of service via a segmentation fault in `tf.raw_ops.MaxPoolGrad` caused by missing validation. The [implementation](https://github.com/tensorflow/tensorflow/blob/460e000de3a83278fb00b61a16d161b1964f15f4/tensorflow/core/kernels/maxpooling_op.cc) misses some validation for the `orig_input` and `orig_output` tensors. The fixes for CVE-2021-29579 were incomplete. We have patched the issue in GitHub commit 136b51f10903e044308cf77117c0ed9871350475. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37674
MISC
CONFIRM
MISC |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions the implementation of `tf.raw_ops.StringNGrams` is vulnerable to an integer overflow issue caused by converting a signed integer value to an unsigned one and then allocating memory based on this value. The [implementation](https://github.com/tensorflow/tensorflow/blob/8d72537c6abf5a44103b57b9c2e22c14f5f49698/tensorflow/core/kernels/string_ngrams_op.cc#L184) calls `reserve` on a `tstring` with a value that sometimes can be negative if user supplies negative `ngram_widths`. The `reserve` method calls `TF_TString_Reserve` which has an `unsigned long` argument for the size of the buffer. Hence, the implicit conversion transforms the negative value to a large integer. We have patched the issue in GitHub commit c283e542a3f422420cfdb332414543b62fc4e4a5. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37646
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions an attacker can cause a floating point exception by calling inplace operations with crafted arguments that would result in a division by 0. The [implementation](https://github.com/tensorflow/tensorflow/blob/84d053187cb80d975ef2b9684d4b61981bca0c41/tensorflow/core/kernels/inplace_ops.cc#L283) has a logic error: it should skip processing if `x` and `v` are empty but the code uses `||` instead of `&&`. We have patched the issue in GitHub commit e86605c0a336c088b638da02135ea6f9f6753618. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37660
CONFIRM
MISC |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions an attacker can cause undefined behavior via binding a reference to null pointer in all binary cwise operations that don’t require broadcasting (e.g., gradients of binary cwise operations). The [implementation](https://github.com/tensorflow/tensorflow/blob/84d053187cb80d975ef2b9684d4b61981bca0c41/tensorflow/core/kernels/cwise_ops_common.h#L264) assumes that the two inputs have exactly the same number of elements but does not check that. Hence, when the eigen functor executes it triggers heap OOB reads and undefined behavior due to binding to nullptr. We have patched the issue in GitHub commit 93f428fd1768df147171ed674fee1fc5ab8309ec. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37659
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions an attacker can cause undefined behavior via binding a reference to null pointer in all operations of type `tf.raw_ops.MatrixSetDiagV*`. The [implementation](https://github.com/tensorflow/tensorflow/blob/84d053187cb80d975ef2b9684d4b61981bca0c41/tensorflow/core/kernels/linalg/matrix_diag_op.cc) has incomplete validation that the value of `k` is a valid tensor. We have check that this value is either a scalar or a vector, but there is no check for the number of elements. If this is an empty tensor, then code that accesses the first element of the tensor is wrong. We have patched the issue in GitHub commit ff8894044dfae5568ecbf2ed514c1a37dc394f1b. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37658
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions an attacker can cause undefined behavior via binding a reference to null pointer in all operations of type `tf.raw_ops.MatrixDiagV*`. The [implementation](https://github.com/tensorflow/tensorflow/blob/84d053187cb80d975ef2b9684d4b61981bca0c41/tensorflow/core/kernels/linalg/matrix_diag_op.cc) has incomplete validation that the value of `k` is a valid tensor. We have check that this value is either a scalar or a vector, but there is no check for the number of elements. If this is an empty tensor, then code that accesses the first element of the tensor is wrong. We have patched the issue in GitHub commit f2a673bd34f0d64b8e40a551ac78989d16daad09. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37657
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions an attacker can cause undefined behavior via binding a reference to null pointer in `tf.raw_ops.RaggedTensorToSparse`. The [implementation](https://github.com/tensorflow/tensorflow/blob/f24faa153ad31a4b51578f8181d3aaab77a1ddeb/tensorflow/core/kernels/ragged_tensor_to_sparse_kernel.cc#L30) has an incomplete validation of the splits values: it does not check that they are in increasing order. We have patched the issue in GitHub commit 1071f554dbd09f7e101324d366eec5f4fe5a3ece. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37656
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions an attacker can trigger a read from outside of bounds of heap allocated data by sending invalid arguments to `tf.raw_ops.ResourceScatterUpdate`. The [implementation](https://github.com/tensorflow/tensorflow/blob/f24faa153ad31a4b51578f8181d3aaab77a1ddeb/tensorflow/core/kernels/resource_variable_ops.cc#L919-L923) has an incomplete validation of the relationship between the shapes of `indices` and `updates`: instead of checking that the shape of `indices` is a prefix of the shape of `updates` (so that broadcasting can happen), code only checks that the number of elements in these two tensors are in a divisibility relationship. We have patched the issue in GitHub commit 01cff3f986259d661103412a20745928c727326f. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37655
CONFIRM
MISC |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions an attacker can trigger a crash via a `CHECK`-fail in debug builds of TensorFlow using `tf.raw_ops.ResourceGather` or a read from outside the bounds of heap allocated data in the same API in a release build. The [implementation](https://github.com/tensorflow/tensorflow/blob/f24faa153ad31a4b51578f8181d3aaab77a1ddeb/tensorflow/core/kernels/resource_variable_ops.cc#L660-L668) does not check that the `batch_dims` value that the user supplies is less than the rank of the input tensor. Since the implementation uses several for loops over the dimensions of `tensor`, this results in reading data from outside the bounds of heap allocated buffer backing the tensor. We have patched the issue in GitHub commit bc9c546ce7015c57c2f15c168b3d9201de679a1d. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37654
CONFIRM
MISC |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions an attacker can trigger a crash via a floating point exception in `tf.raw_ops.ResourceGather`. The [implementation](https://github.com/tensorflow/tensorflow/blob/f24faa153ad31a4b51578f8181d3aaab77a1ddeb/tensorflow/core/kernels/resource_variable_ops.cc#L725-L731) computes the value of a value, `batch_size`, and then divides by it without checking that this value is not 0. We have patched the issue in GitHub commit ac117ee8a8ea57b73d34665cdf00ef3303bc0b11. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37653
CONFIRM
MISC |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions the implementation for `tf.raw_ops.BoostedTreesCreateEnsemble` can result in a use after free error if an attacker supplies specially crafted arguments. The [implementation](https://github.com/tensorflow/tensorflow/blob/f24faa153ad31a4b51578f8181d3aaab77a1ddeb/tensorflow/core/kernels/boosted_trees/resource_ops.cc#L55) uses a reference counted resource and decrements the refcount if the initialization fails, as it should. However, when the code was written, the resource was represented as a naked pointer but later refactoring has changed it to be a smart pointer. Thus, when the pointer leaves the scope, a subsequent `free`-ing of the resource occurs, but this fails to take into account that the refcount has already reached 0, thus the resource has been already freed. During this double-free process, members of the resource object are accessed for cleanup but they are invalid as the entire resource has been freed. We have patched the issue in GitHub commit 5ecec9c6fbdbc6be03295685190a45e7eee726ab. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37652
MISC
CONFIRM |
tensorflow — tensorflow
|
TensorFlow is an end-to-end open source platform for machine learning. In affected versions the implementation for `tf.raw_ops.ExperimentalDatasetToTFRecord` and `tf.raw_ops.DatasetToTFRecord` can trigger heap buffer overflow and segmentation fault. The [implementation](https://github.com/tensorflow/tensorflow/blob/f24faa153ad31a4b51578f8181d3aaab77a1ddeb/tensorflow/core/kernels/data/experimental/to_tf_record_op.cc#L93-L102) assumes that all records in the dataset are of string type. However, there is no check for that, and the example given above uses numeric types. We have patched the issue in GitHub commit e0b6e58c328059829c3eb968136f17aa72b6c876. The fix will be included in TensorFlow 2.6.0. We will also cherrypick this commit on TensorFlow 2.5.1, TensorFlow 2.4.3, and TensorFlow 2.3.4, as these are also affected and still in supported range. |
2021-08-12 |
not yet calculated |
CVE-2021-37650
MISC
CONFIRM |
tinyobjloader — tinyobjloader
|
An improper array index validation vulnerability exists in the LoadObj functionality of tinyobjloader v2.0-rc1 and tinyobjloader development commit 79d4421. A specially crafted file could lead to code execution. An attacker can provide a malicious file to trigger this vulnerability. |
2021-08-11 |
not yet calculated |
CVE-2020-28589
MISC |
tmerc-cogs — tmerc-cogs
|
tmerc-cogs are a collection of open source plugins for the Red Discord bot. A vulnerability has been found in the code that allows any user to access sensitive information by crafting a specific membership event message. Issue is patched in commit d63c49b4cfc30c795336e4fff08cba3795e0fcc0. As a workaround users may unload the Welcome cog. |
2021-08-11 |
not yet calculated |
CVE-2021-37697
CONFIRM
MISC |
tmerc-cogs — tmerc-cogs
|
tmerc-cogs are a collection of open source plugins for the Red Discord bot. A vulnerability has been found in the code that allows any user to access sensitive information by crafting a specific MassDM message. Issue is patched in commit 92325be650a6c17940cc52611797533ed95dbbe1. All users are advised to update to the current commit. As a workaround users may unload the MassDM cog or globally disable the `[p]massdm` command. |
2021-08-11 |
not yet calculated |
CVE-2021-37696
CONFIRM
MISC |
tp-link — ue330_usb_splitter_devices
|
TP-Link UE330 USB splitter devices through 2021-08-09, in certain specific use cases in which the device supplies power to audio-output equipment, allow remote attackers to recover speech signals from an LED on the device, via a telescope and an electro-optical sensor, aka a “Glowworm” attack. We assume that the USB splitter supplies power to some speakers. The power indicator LED of the USB splitter is connected directly to the power line, as a result, the intensity of the USB splitter’s power indicator LED is correlative to its power consumption. The sound played by the connected speakers affects the USB splitter’s power consumption and as a result is also correlative to the light intensity of the LED. By analyzing measurements obtained from an electro-optical sensor directed at the power indicator LED of the USB splitter, we can recover the sound played by the connected speakers. |
2021-08-11 |
not yet calculated |
CVE-2021-38543
MISC |
trendnet — tew-755ap
|
Null Pointer Dereference vulnerability exists in TRENDnet TEW-755AP 1.11B03, TEW-755AP2KAC 1.11B03, TEW-821DAP2KAC 1.11B03, and TEW-825DAP 1.11B03 by sending the POST request to apply_cgi via a do_graph_auth action without a session_id key. |
2021-08-10 |
not yet calculated |
CVE-2021-28844
MISC |
trendnet — tew-755ap
|
A Format String vulnerablity exists in TRENDnet TEW-755AP 1.11B03, TEW-755AP2KAC 1.11B03, TEW-821DAP2KAC 1.11B03, and TEW-825DAP 1.11B03, which could let a remote malicious user cause a denial of service due to a logic bug at address 0x40dcd0 when calling fprintf with “%s: key len = %d, too longn” format. The two variables seem to be put in the wrong order. The vulnerability could be triggered by sending the POST request to apply_cgi with a long and unknown key in the request body. |
2021-08-10 |
not yet calculated |
CVE-2021-28846
MISC |
trendnet — tew-755ap
|
Null Pointer Dereference vulnerability exists in TRENDnet TEW-755AP 1.11B03, TEW-755AP2KAC 1.11B03, TEW-821DAP2KAC 1.11B03, and TEW-825DAP 1.11B03 by sending the POST request to apply_cgi with an unknown action name. |
2021-08-10 |
not yet calculated |
CVE-2021-28843
MISC |
trendnet — tew-755ap
|
Null Pointer Dereference vulnerability in TRENDnet TEW-755AP 1.11B03, TEW-755AP2KAC 1.11B03, TEW-821DAP2KAC 1.11B03, and TEW-825DAP 1.11B03, which could let a remote malicious user cause a denial of service by sending a POST request to apply_cgi via an action ping_test without a ping_ipaddr key. |
2021-08-10 |
not yet calculated |
CVE-2021-28841
MISC |
trendnet — tew-755ap
|
Null Pointer Deference vulnerability exists in TRENDnet TEW-755AP 1.11B03, TEW-755AP2KAC 1.11B03, TEW-821DAP2KAC 1.11B03, and TEW-825DAP 1.11B03, which could let a remote malicious user cause a denial os service by sending the POST request to apply_cgi via action do_graph_auth without login_name key. |
2021-08-10 |
not yet calculated |
CVE-2021-28842
MISC |
trendnet — tv-ip110wn
|
Cross Site Scripting (XSS) vulnerability in TRENDnet TV-IP110WN V1.2.2.64 V1.2.2.65 V1.2.2.68 via the profile parameter. in a GET request in view.cgi. |
2021-08-10 |
not yet calculated |
CVE-2021-31655
MISC
MISC
MISC |
ttiny — java_web_server_and_servlet_container
|
A reflected cross-site scripting (XSS) vulnerability in the web server TTiny Java Web Server and Servlet Container (TJWS) <=1.115 allows an adversary to inject malicious code on the server’s “404 Page not Found” error page |
2021-08-09 |
not yet calculated |
CVE-2021-37573
MISC |
| typo3 — typo3 |
The dated_news (aka Dated News) extension through 5.1.1 for TYPO3 allows XSS. |
2021-08-13 |
not yet calculated |
CVE-2021-36790
MISC
MISC |
| typo3 — typo3 |
The femanager extension before 5.5.1 and 6.x before 6.3.1 for TYPO3 allows XSS via a crafted SVG document. |
2021-08-13 |
not yet calculated |
CVE-2021-36787
MISC
CONFIRM |
| typo3 — typo3 |
The dated_news (aka Dated News) extension through 5.1.1 for TYPO3 allows Information Disclosure of application registration data. |
2021-08-13 |
not yet calculated |
CVE-2021-36791
MISC
CONFIRM |
| typo3 — typo3 |
TYPO3 is an open source PHP based web content management system released under the GNU GPL. In affected versions failing to properly parse, sanitize and encode malicious rich-text content, the content rendering process in the website frontend is vulnerable to cross-site scripting. Corresponding rendering instructions via TypoScript functionality HTMLparser does not consider all potentially malicious HTML tag & attribute combinations per default. In default scenarios, a valid backend user account is needed to exploit this vulnerability. In case custom plugins used in the website frontend accept and reflect rich-text content submitted by users, no authentication is required. Update to TYPO3 versions 7.6.53 ELTS, 8.7.42 ELTS, 9.5.29, 10.4.19, 11.3.2 that fix the problem described. |
2021-08-10 |
not yet calculated |
CVE-2021-32768
MISC
CONFIRM |
typo3 — typo3
|
The yoast_seo (aka Yoast SEO) extension before 7.2.3 for TYPO3 allows XSS. |
2021-08-13 |
not yet calculated |
CVE-2021-36788
MISC
CONFIRM |
typo3 — typo3
|
The miniorange_saml (aka Miniorange Saml) extension before 1.4.3 for TYPO3 allows XSS. |
2021-08-13 |
not yet calculated |
CVE-2021-36785
MISC
CONFIRM |
typo3 — typo3
|
The miniorange_saml (aka Miniorange Saml) extension before 1.4.3 for TYPO3 allows Sensitive Data Exposure of API credentials and private keys. |
2021-08-13 |
not yet calculated |
CVE-2021-36786
MISC
CONFIRM |
typo3 — typo3
|
The deferred_image_processing (aka Deferred image processing) extension before 1.0.2 for TYPO3 allows Denial of Service via the FAL API because of /var/transient disk consumption. |
2021-08-13 |
not yet calculated |
CVE-2021-38623
MISC |
typo3 — typo3
|
The dated_news (aka Dated News) extension through 5.1.1 for TYPO3 allows SQL Injection. |
2021-08-13 |
not yet calculated |
CVE-2021-36789
MISC
MISC |
typo3 — typo3
|
The routes (aka Extbase Yaml Routes) extension before 2.1.1 for TYPO3, when CsrfTokenViewHelper is used, allows Sensitive Information Disclosure because a session identifier is unsafely present in HTML output. |
2021-08-13 |
not yet calculated |
CVE-2021-36793
CONFIRM
MISC |
typo3 — typo3
|
The Newsletter extension through 4.0.0 for TYPO3 allows SQL Injection. |
2021-08-13 |
not yet calculated |
CVE-2021-38302
MISC
CONFIRM |
typo3 — typo3
|
The dated_news (aka Dated News) extension through 5.1.1 for TYPO3 has incorrect Access Control for confirming various applications. |
2021-08-13 |
not yet calculated |
CVE-2021-36792
MISC
MISC |
uaa — server
|
UAA server versions prior to 75.4.0 are vulnerable to an open redirect vulnerability. A malicious user can exploit the open redirect vulnerability by social engineering leading to take over of victims’ accounts in certain cases along with redirection of UAA users to a malicious sites. |
2021-08-11 |
not yet calculated |
CVE-2021-22098
MISC |
ubuntu — dolibarr
|
In “Dolibarr” application, 2.8.1 to 13.0.4 don’t restrict or incorrectly restricts access to a resource from an unauthorized actor. A low privileged attacker can modify the Private Note which only an administrator has rights to do, the affected field is at “/adherents/note.php?id=1” endpoint. |
2021-08-09 |
not yet calculated |
CVE-2021-25954
MISC
MISC |
ucweb — ucweb
|
UCWeb UC 12.12.3.1219 through 12.12.3.1226 uses cleartext HTTP, and thus man-in-the-middle attackers can discover visited URLs. |
2021-08-14 |
not yet calculated |
CVE-2020-36473
MISC |
virtual_robots.txt — virtual_robots.txt
|
Virtual Robots.txt before 1.10 does not block HTML tags in the robots.txt field. |
2021-08-12 |
not yet calculated |
CVE-2021-28121
MISC |
wal-g — wal-g
|
WAL-G before 1.1, when a non-libsodium build (e.g., one of the official binary releases published as GitHub Releases) is used, silently ignores the libsodium encryption key and uploads cleartext backups. This is arguably a Principle of Least Surprise violation because “the user likely wanted to encrypt all file activity.” |
2021-08-12 |
not yet calculated |
CVE-2021-38599
MISC
MISC |
wasm3 — wasm3
|
Wasm3 0.5.0 has a heap-based buffer overflow in op_Const64 (called from EvaluateExpression and m3_LoadModule). |
2021-08-12 |
not yet calculated |
CVE-2021-38592
MISC
MISC |
winner — winner
|
Winner (aka ToneWinner) desktop speakers through 2021-08-09 allow remote attackers to recover speech signals from the power-indicator LED via a telescope and an electro-optical sensor, aka a “Glowworm” attack. |
2021-08-10 |
not yet calculated |
CVE-2021-38365
MISC
MISC |
wolfssl — wolfssl
|
wolfSSL before 4.8.1 incorrectly skips OCSP verification in certain situations of irrelevant response data that contains the NoCheck extension. |
2021-08-12 |
not yet calculated |
CVE-2021-38597
MISC
MISC |
| wordpress — wordpress |
The WP Fusion Lite WordPress plugin is vulnerable to Reflected Cross-Site Scripting via the startdate parameter found in the ~/includes/admin/logging/class-log-table-list.php file which allows attackers to inject arbitrary web scripts, in versions up to and including 3.37.18. |
2021-08-09 |
not yet calculated |
CVE-2021-34660
MISC
MISC |
wordpress — wordpress
|
The Stock in & out WordPress plugin through 1.0.4 lacks proper sanitization before passing variables to an SQL request, making it vulnerable to SQL Injection attacks. Users with a role of contributor or higher can exploit this vulnerability. |
2021-08-09 |
not yet calculated |
CVE-2021-24520
MISC
MISC |
wordpress — wordpress
|
The Newsmag WordPress theme before 5.0 does not sanitise the td_block_id parameter in its td_ajax_block AJAX action, leading to an unauthenticated Reflected Cross-site Scripting (XSS) vulnerability. |
2021-08-09 |
not yet calculated |
CVE-2021-24304
MISC |
wordpress — wordpress
|
The Securimage-WP-Fixed WordPress plugin is vulnerable to Reflected Cross-Site Scripting due to the use of $_SERVER[‘PHP_SELF’] in the ~/securimage-wp.php file which allows attackers to inject arbitrary web scripts, in versions up to and including 3.5.4. |
2021-08-11 |
not yet calculated |
CVE-2021-34640
MISC
MISC |
wordpress — wordpress
|
The Page View Count WordPress plugin before 2.4.9 does not escape the postid parameter of pvc_stats shortcode, allowing users with a role as low as Contributor to perform Stored XSS attacks. A post made by a contributor would still have to be approved by an admin to have the XSS triggered in the frontend, however, higher privilege users, such as editor could exploit this without the need of approval, and even when the blog disallows the unfiltered_html capability. |
2021-08-09 |
not yet calculated |
CVE-2021-24509
MISC |
wordpress — wordpress
|
The WP Fusion Lite WordPress plugin is vulnerable to Cross-Site Request Forgery via the `show_logs_section` function found in the ~/includes/admin/logging/class-log-handler.php file which allows attackers to drop all logs for the plugin, in versions up to and including 3.37.18. |
2021-08-09 |
not yet calculated |
CVE-2021-34661
MISC
MISC |
wordpress — wordpress
|
The User Registration, User Profile, Login & Membership – ProfilePress (Formerly WP User Avatar) WordPress plugin before 3.1.11’s widget for tabbed login/register was not properly escaped and could be used in an XSS attack which could lead to wp-admin access. Further, the plugin in several places assigned $_POST as $_GET which meant that in some cases this could be replicated with just $_GET parameters and no need for $_POST values. |
2021-08-09 |
not yet calculated |
CVE-2021-24522
MISC |
wordpress — wordpress
|
The Astra Pro Addon WordPress plugin before 3.5.2 did not properly sanitise or escape some of the POST parameters from the astra_pagination_infinite and astra_shop_pagination_infinite AJAX action (available to both unauthenticated and authenticated user) before using them in SQL statement, leading to an SQL Injection issues |
2021-08-09 |
not yet calculated |
CVE-2021-24507
MISC
MISC |
wordpress — wordpress
|
The Forms WordPress plugin before 1.12.3 did not sanitise its input fields, leading to Stored Cross-Site scripting issues. The plugin was vulnerable to an Authenticated Stored Cross-Site Scripting (XSS) vulnerability within the Forms “Add new” field. |
2021-08-09 |
not yet calculated |
CVE-2021-24505
MISC |
wordpress — wordpress
|
The WP Google Map WordPress plugin before 1.7.7 did not sanitise or escape the Map Title before outputting them in the page, leading to a Stored Cross-Site Scripting issue by high privilege users, even when the unfiltered_html capability is disallowed |
2021-08-09 |
not yet calculated |
CVE-2021-24502
MISC
MISC |
wordpress — wordpress
|
The Workreap WordPress theme before 2.2.2 had several AJAX actions missing authorization checks to verify that a user was authorized to perform critical operations such as modifying or deleting objects. This allowed a logged in user to modify or delete objects belonging to other users on the site. |
2021-08-09 |
not yet calculated |
CVE-2021-24501
MISC
MISC |
wordpress — wordpress
|
Several AJAX actions available in the Workreap WordPress theme before 2.2.2 lacked CSRF protections, as well as allowing insecure direct object references that were not validated. This allows an attacker to trick a logged in user to submit a POST request to the vulnerable site, potentially modifying or deleting arbitrary objects on the target site. |
2021-08-09 |
not yet calculated |
CVE-2021-24500
MISC
MISC |
wordpress — wordpress
|
The Side Menu Lite – add sticky fixed buttons WordPress plugin before 2.2.1 does not properly sanitize input values from the browser when building an SQL statement. Users with the administrator role or permission to manage this plugin could perform an SQL Injection attack. |
2021-08-09 |
not yet calculated |
CVE-2021-24521
MISC
MISC |
wordpress — wordpress
|
The Workreap WordPress theme before 2.2.2 AJAX actions workreap_award_temp_file_uploader and workreap_temp_file_uploader did not perform nonce checks, or validate that the request is from a valid user in any other way. The endpoints allowed for uploading arbitrary files to the uploads/workreap-temp directory. Uploaded files were neither sanitized nor validated, allowing an unauthenticated visitor to upload executable code such as php scripts. |
2021-08-09 |
not yet calculated |
CVE-2021-24499
MISC
MISC |
wordpress — wordpress
|
The Marmoset Viewer WordPress plugin before 1.9.3 does not property sanitize, validate or escape the ‘id’ parameter before outputting back in the page, leading to a reflected Cross-Site Scripting issue. |
2021-08-09 |
not yet calculated |
CVE-2021-24495
MISC
MISC |
wordpress — wordpress
|
The Leaflet Map WordPress plugin before 3.0.0 does not verify the CSRF nonce when saving its settings, which allows attackers to make a logged in admin update the settings via a Cross-Site Request Forgery attack. This could lead to Cross-Site Scripting issues by either changing the URL of the JavaScript library being used, or using malicious attributions which will be executed in all page with an embed map from the plugin |
2021-08-09 |
not yet calculated |
CVE-2021-24467
MISC |
yii2 — yii2
|
yii2 is vulnerable to Use of Predictable Algorithm in Random Number Generator |
2021-08-10 |
not yet calculated |
CVE-2021-3689
CONFIRM
MISC |
yii2 — yii2
|
yii2 is vulnerable to Use of Predictable Algorithm in Random Number Generator |
2021-08-10 |
not yet calculated |
CVE-2021-3692
MISC
CONFIRM |
zte — zxhn_h2640
|
There is an information leak vulnerability in the digital media player (DMS) of ZTE’s residential gateway product. The attacker could insert the USB disk with the symbolic link into the residential gateway, and access unauthorized directory information through the symbolic link, causing information leak. |
2021-08-09 |
not yet calculated |
CVE-2021-21740
MISC |


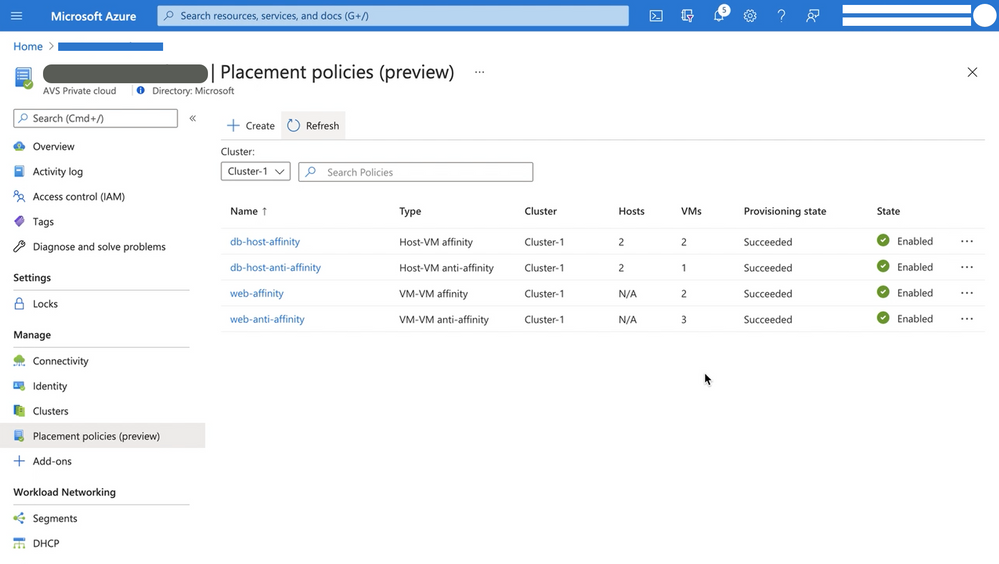
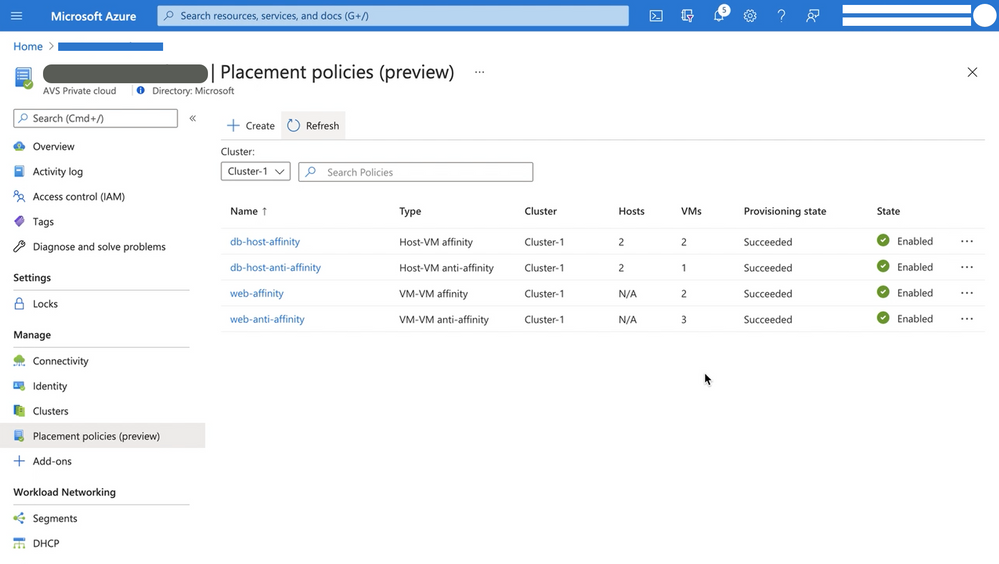
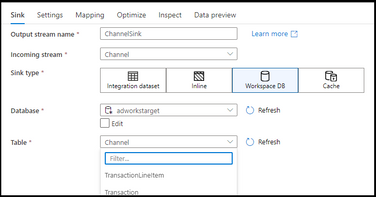
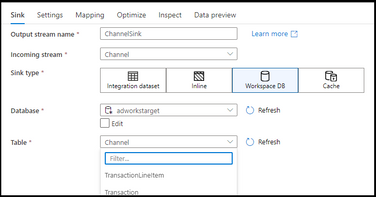
Recent Comments