by Scott Muniz | Sep 6, 2021 | Security, Technology
This article is contributed. See the original author and article here.
acccusine — pcs+/pfv+
|
A CWE-200: Exposure of Sensitive Information to an Unauthorized Actor vulnerability exist in AccuSine PCS+ / PFV+ (Versions prior to V1.6.7) and AccuSine PCSn (Versions prior to V2.2.4) that could allow an authenticated attacker to access the device via FTP protocol. |
2021-09-02 |
not yet calculated |
CVE-2021-22793
MISC |
adaptivescale — adaptivescale
|
A Hardcoded JWT Secret Key in metadata.py in AdaptiveScale LXDUI through 2.1.3 allows attackers to gain admin access to the host system. |
2021-09-03 |
not yet calculated |
CVE-2021-40494
MISC |
| adobe — acrobat_reader_dc |
Acrobat Reader DC versions versions 2021.001.20150 (and earlier), 2020.001.30020 (and earlier) and 2017.011.30194 (and earlier) are affected by an Out-of-bounds Read vulnerability in the PDFLibTool component. An unauthenticated attacker could leverage this vulnerability to achieve arbitrary code execution in the context of the current user. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-02 |
not yet calculated |
CVE-2021-28565
MISC |
| adobe — acrobat_reader_dc |
Acrobat Reader DC versions versions 2021.001.20150 (and earlier), 2020.001.30020 (and earlier) and 2017.011.30194 (and earlier) are affected by an Out-of-bounds Write vulnerability within the ImageTool component. An unauthenticated attacker could leverage this vulnerability to achieve arbitrary code execution in the context of the current user. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-02 |
not yet calculated |
CVE-2021-28564
MISC |
| adobe — acrobat_reader_dc |
Acrobat Reader DC versions versions 2021.001.20150 (and earlier), 2020.001.30020 (and earlier) and 2017.011.30194 (and earlier) are affected by a memory corruption vulnerability. An unauthenticated attacker could leverage this vulnerability to achieve arbitrary code execution in the context of the current user. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-02 |
not yet calculated |
CVE-2021-28561
MISC |
| adobe — acrobat_reader_dc |
Acrobat Reader DC versions versions 2021.001.20150 (and earlier), 2020.001.30020 (and earlier) and 2017.011.30194 (and earlier) are affected by an Out-of-bounds Read vulnerability. An unauthenticated attacker could leverage this vulnerability to leak sensitive system information in the context of the current user. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-02 |
not yet calculated |
CVE-2021-28557
MISC |
| adobe — acrobat_reader_dc |
Acrobat Reader DC versions versions 2021.001.20150 (and earlier), 2020.001.30020 (and earlier) and 2017.011.30194 (and earlier) are affected by an Out-of-bounds Read vulnerability. An unauthenticated attacker could leverage this vulnerability to get access to sensitive information in the context of the current user. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-02 |
not yet calculated |
CVE-2021-28555
MISC |
adobe — acrobat_reader_dc
|
Acrobat Reader DC versions versions 2021.001.20150 (and earlier), 2020.001.30020 (and earlier) and 2017.011.30194 (and earlier) are affected by an Heap-based buffer overflow vulnerability in the PDFLibTool component. An unauthenticated attacker could leverage this vulnerability to achieve arbitrary code execution in the context of the current user. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-02 |
not yet calculated |
CVE-2021-28558
MISC |
adobe — acrobat_reader_dc
|
Acrobat Reader DC versions versions 2020.013.20074 (and earlier), 2020.001.30018 (and earlier) and 2017.011.30188 (and earlier) are affected by an Out-of-bounds Write vulnerability in the CoolType library. An unauthenticated attacker could leverage this vulnerability to achieve arbitrary code execution in the context of the current user. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-02 |
not yet calculated |
CVE-2021-21086
MISC |
adobe — acrobat_reader_dc
|
Acrobat Reader DC versions versions 2021.001.20150 (and earlier), 2020.001.30020 (and earlier) and 2017.011.30194 (and earlier) are affected by a Heap-based Buffer Overflow vulnerability. An unauthenticated attacker could leverage this vulnerability to achieve arbitrary code execution in the context of the current user. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-02 |
not yet calculated |
CVE-2021-28560
MISC |
adobe — acrobat_reader_dc
|
Acrobat Reader DC versions versions 2021.001.20150 (and earlier), 2020.001.30020 (and earlier) and 2017.011.30194 (and earlier) are affected by an Information Exposure vulnerability. An unauthenticated attacker could leverage this vulnerability to get access to restricted data stored within global variables and objects. |
2021-09-02 |
not yet calculated |
CVE-2021-28559
MISC |
| adobe — acrobat_reader_dc |
Acrobat Reader DC versions versions 2021.001.20150 (and earlier), 2020.001.30020 (and earlier) and 2017.011.30194 (and earlier) are affected by an Use After Free vulnerability. An unauthenticated attacker could leverage this vulnerability to achieve arbitrary code execution in the context of the current user. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-02 |
not yet calculated |
CVE-2021-28553
MISC |
adobe — acrobat_reader_dc
|
Acrobat Reader DC versions versions 2021.001.20150 (and earlier), 2020.001.30020 (and earlier) and 2017.011.30194 (and earlier) are affected by a Use After Free vulnerability. An unauthenticated attacker could leverage this vulnerability to achieve arbitrary code execution in the context of the current user. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-02 |
not yet calculated |
CVE-2021-28550
MISC |
| adobe — after_effects |
Adobe After Effects version 18.2.1 (and earlier) is affected by an Out-of-bounds Read vulnerability when parsing a specially crafted file. An unauthenticated attacker could leverage this vulnerability to disclose sensitive memory information in the context of the current user. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-02 |
not yet calculated |
CVE-2021-36018
MISC |
| adobe — after_effects |
Adobe After Effects version 18.2.1 (and earlier) is affected by an out-of-bounds Write vulnerability when parsing a specially crafted file. An unauthenticated attacker could leverage this vulnerability to achieve arbitrary code execution in the context of the current user. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-02 |
not yet calculated |
CVE-2021-35994
MISC |
adobe — after_effects
|
Adobe After Effects version 18.2.1 (and earlier) is affected by an Out-of-bounds Read vulnerability when parsing a specially crafted file. An unauthenticated attacker could leverage this vulnerability to disclose arbitrary memory information in the context of the current user. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-02 |
not yet calculated |
CVE-2021-36019
MISC |
adobe — after_effects
|
Adobe After Effects version 18.2.1 (and earlier) is affected by a memory corruption vulnerability when parsing a specially crafted file. An unauthenticated attacker could leverage this vulnerability to achieve arbitrary code execution in the context of the current user. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-02 |
not yet calculated |
CVE-2021-36017
MISC |
adobe — after_effects
|
Adobe After Effects version 18.2.1 (and earlier) is affected by an out-of-bounds Write vulnerability when parsing a specially crafted file. An unauthenticated attacker could leverage this vulnerability to achieve arbitrary code execution in the context of the current user. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-02 |
not yet calculated |
CVE-2021-35993
MISC |
adobe — after_effects
|
Adobe After Effects version 18.2.1 (and earlier) is affected by an Improper input validation vulnerability when parsing a specially crafted file. An unauthenticated attacker could leverage this vulnerability to disclose arbitrary memory information in the context of the current user. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-02 |
not yet calculated |
CVE-2021-35995
MISC |
adobe — after_effects
|
Adobe After Effects version 18.2.1 (and earlier) is affected by a memory corruption vulnerability when parsing a specially crafted file. An unauthenticated attacker could leverage this vulnerability to achieve arbitrary code execution in the context of the current user. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-02 |
not yet calculated |
CVE-2021-35996
MISC |
adobe — bridge
|
Adobe Bridge version 11.1 (and earlier) is affected by a memory corruption vulnerability due to insecure handling of a malicious Bridge file, potentially resulting in arbitrary code execution in the context of the current user. User interaction is required to exploit this vulnerability. |
2021-09-01 |
not yet calculated |
CVE-2021-36068
MISC |
| adobe — bridge |
Adobe Bridge versions 11.1 (and earlier) are affected by an out-of-bounds write vulnerability that could result in arbitrary code execution in the context of the current user. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-01 |
not yet calculated |
CVE-2021-36072
MISC |
adobe — bridge
|
Adobe Bridge versions 11.1 (and earlier) are affected by an out-of-bounds read vulnerability that could lead to disclosure of arbitrary memory. An attacker could leverage this vulnerability to bypass mitigations such as ASLR. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-01 |
not yet calculated |
CVE-2021-36071
MISC |
| adobe — bridge |
Adobe Bridge version 11.1 (and earlier) is affected by a memory corruption vulnerability due to insecure handling of a malicious Bridge file, potentially resulting in arbitrary code execution in the context of the current user. User interaction is required to exploit this vulnerability. |
2021-09-01 |
not yet calculated |
CVE-2021-36069
MISC |
adobe — bridge
|
Adobe Bridge version 11.1 (and earlier) is affected by a memory corruption vulnerability due to insecure handling of a malicious Bridge file, potentially resulting in arbitrary code execution in the context of the current user. User interaction is required to exploit this vulnerability. |
2021-09-01 |
not yet calculated |
CVE-2021-36067
MISC |
adobe — bridge
|
Adobe Bridge version 11.1 (and earlier) is affected by an out-of-bounds read vulnerability when parsing a crafted .SGI file, which could result in a read past the end of an allocated memory structure. An attacker could leverage this vulnerability to execute code in the context of the current user. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-01 |
not yet calculated |
CVE-2021-36079
MISC |
adobe — bridge
|
Adobe Bridge version 11.1 (and earlier) is affected by a memory corruption vulnerability due to insecure handling of a malicious Bridge file, potentially resulting in arbitrary code execution in the context of the current user. User interaction is required to exploit this vulnerability. |
2021-09-01 |
not yet calculated |
CVE-2021-39816
MISC |
adobe — bridge
|
Adobe Bridge version 11.1 (and earlier) is affected by a memory corruption vulnerability due to insecure handling of a malicious Bridge file, potentially resulting in arbitrary code execution in the context of the current user. User interaction is required to exploit this vulnerability. |
2021-09-01 |
not yet calculated |
CVE-2021-36049
MISC |
adobe — bridge
|
Adobe Bridge version 11.1 (and earlier) is affected by a memory corruption vulnerability due to insecure handling of a malicious Bridge file, potentially resulting in arbitrary code execution in the context of the current user. User interaction is required to exploit this vulnerability. |
2021-09-01 |
not yet calculated |
CVE-2021-36059
MISC |
| adobe — bridge |
Adobe Bridge version 11.1 (and earlier) is affected by a memory corruption vulnerability due to insecure handling of a malicious Bridge file, potentially resulting in arbitrary code execution in the context of the current user. User interaction is required to exploit this vulnerability. |
2021-09-01 |
not yet calculated |
CVE-2021-36076
MISC |
| adobe — bridge |
Adobe Bridge version 11.1 (and earlier) is affected by a heap-based buffer overflow vulnerability when parsing a crafted .SGI file. An attacker could leverage this vulnerability to execute code in the context of the current user. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-01 |
not yet calculated |
CVE-2021-36073
MISC |
adobe — bridge
|
Adobe Bridge versions 11.1 (and earlier) are affected by an out-of-bounds read vulnerability that could lead to disclosure of arbitrary memory. An attacker could leverage this vulnerability to bypass mitigations such as ASLR. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-01 |
not yet calculated |
CVE-2021-36074
MISC |
adobe — bridge
|
Adobe Bridge version 11.1 (and earlier) is affected by a Buffer Overflow vulnerability due to insecure handling of a malicious Bridge file, potentially resulting in arbitrary code execution in the context of the current user. User interaction is required to exploit this vulnerability. |
2021-09-01 |
not yet calculated |
CVE-2021-36075
MISC |
| adobe — bridge |
Adobe Bridge version 11.1 (and earlier) is affected by a memory corruption vulnerability due to insecure handling of a malicious SVG file, potentially resulting in local application denial of service in the context of the current user. User interaction is required to exploit this vulnerability. |
2021-09-01 |
not yet calculated |
CVE-2021-36077
MISC |
adobe — bridge
|
Adobe Bridge version 11.1 (and earlier) is affected by a memory corruption vulnerability due to insecure handling of a malicious Bridge file, potentially resulting in arbitrary code execution in the context of the current user. User interaction is required to exploit this vulnerability. |
2021-09-01 |
not yet calculated |
CVE-2021-36078
MISC |
| adobe — bridge |
Adobe Bridge version 11.1 (and earlier) is affected by a memory corruption vulnerability due to insecure handling of a malicious Bridge file, potentially resulting in arbitrary code execution in the context of the current user. User interaction is required to exploit this vulnerability. |
2021-09-01 |
not yet calculated |
CVE-2021-39817
MISC |
adobe — captivate
|
Adobe Captivate version 11.5.5 (and earlier) is affected by an Creation of Temporary File In Directory With Incorrect Permissions vulnerability that could result in privilege escalation in the context of the current user. The attacker must plant a malicious file in a particular location of the victim’s machine. Exploitation of this issue requires user interaction in that a victim must launch the Captivate Installer. |
2021-09-01 |
not yet calculated |
CVE-2021-36002
MISC |
| adobe — connect |
Adobe Connect version 11.2.2 (and earlier) is affected by a Reflected Cross-site Scripting vulnerability that could be abused by an attacker to inject malicious scripts into vulnerable form fields. Malicious JavaScript may be executed in a victim’s browser when they browse to the page containing the vulnerable field. |
2021-09-01 |
not yet calculated |
CVE-2021-36063
MISC |
| adobe — connect |
Adobe Connect version 11.2.2 (and earlier) is affected by a Reflected Cross-site Scripting vulnerability that could be abused by an attacker to inject malicious scripts into vulnerable form fields. If an attacker is able to convince a victim to visit a URL referencing a vulnerable page, malicious JavaScript content may be executed within the context of the victim’s browser. |
2021-09-01 |
not yet calculated |
CVE-2021-36062
MISC |
| adobe — connect |
Adobe Connect version 11.2.2 (and earlier) is affected by a secure design principles violation vulnerability via the ‘pbMode’ parameter. An unauthenticated attacker could leverage this vulnerability to edit or delete recordings on the Connect environment. Exploitation of this issue requires user interaction in that a victim must publish a link of a Connect recording. |
2021-09-01 |
not yet calculated |
CVE-2021-36061
MISC |
adobe — media_encoder
|
Adobe Media Encoder version 15.1 (and earlier) is affected by an improper memory access vulnerability when parsing a crafted .SVG file. An attacker could leverage this vulnerability to execute code in the context of the current user. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-01 |
not yet calculated |
CVE-2021-36070
MISC |
adobe — photoshop
|
Adobe Photoshop versions 21.2.10 (and earlier) and 22.4.3 (and earlier) are affected by an out-of-bounds write vulnerability that could result in arbitrary code execution in the context of the current user. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-01 |
not yet calculated |
CVE-2021-36066
MISC |
adobe — photoshop
|
Adobe Photoshop versions 21.2.10 (and earlier) and 22.4.3 (and earlier) are affected by a heap-based buffer overflow vulnerability that could result in arbitrary code execution in the context of the current user. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-01 |
not yet calculated |
CVE-2021-36065
MISC |
| amazon — kindle_e-reader |
Amazon Kindle e-reader prior to and including version 5.13.4 contains an Integer Overflow that leads to a Heap-Based Buffer Overflow in function CJBig2Image::expand() and results in a memory corruption that leads to code execution when parsing a crafted PDF book. |
2021-09-01 |
not yet calculated |
CVE-2021-30354
MISC |
amazon — kindle_e-reader
|
Amazon Kindle e-reader prior to and including version 5.13.4 improperly manages privileges, allowing the framework user to elevate privileges to root. |
2021-09-01 |
not yet calculated |
CVE-2021-30355
MISC |
apache — openid_connect
|
mod_auth_openidc is an authentication/authorization module for the Apache 2.x HTTP server that functions as an OpenID Connect Relying Party, authenticating users against an OpenID Connect Provider. In versions prior to 2.4.9.4, the 3rd-party init SSO functionality of mod_auth_openidc was reported to be vulnerable to an open redirect attack by supplying a crafted URL in the `target_link_uri` parameter. A patch in version 2.4.9.4 made it so that the `OIDCRedirectURLsAllowed` setting must be applied to the `target_link_uri` parameter. There are no known workarounds aside from upgrading to a patched version. |
2021-09-03 |
not yet calculated |
CVE-2021-39191
MISC
MISC
MISC
CONFIRM |
apache — zeppelin
|
Cross Site Scripting vulnerability in markdown interpreter of Apache Zeppelin allows an attacker to inject malicious scripts. This issue affects Apache Zeppelin Apache Zeppelin versions prior to 0.9.0. |
2021-09-02 |
not yet calculated |
CVE-2021-27578
MISC
MLIST
MLIST
MLIST |
appache — zeppelin
|
Authentication bypass vulnerability in Apache Zeppelin allows an attacker to bypass Zeppelin authentication mechanism to act as another user. This issue affects Apache Zeppelin Apache Zeppelin version 0.9.0 and prior versions. |
2021-09-02 |
not yet calculated |
CVE-2020-13929
MISC
MLIST
MLIST
MLIST |
| appache — zeppelin |
bash command injection vulnerability in Apache Zeppelin allows an attacker to inject system commands into Spark interpreter settings. This issue affects Apache Zeppelin Apache Zeppelin version 0.9.0 and prior versions. |
2021-09-02 |
not yet calculated |
CVE-2019-10095
MISC
MLIST
MLIST
MLIST |
atlasian — atlasbaord
|
The renderWidgetResource resource in Atlasian Atlasboard before version 1.1.9 allows remote attackers to read arbitrary files via a path traversal vulnerability. |
2021-09-01 |
not yet calculated |
CVE-2021-39109
MISC |
atlassian — jira_server_and_data_center
|
Affected versions of Atlassian Jira Server and Data Center allow users who have watched an issue to continue receiving updates on the issue even after their Jira account is revoked, via a Broken Access Control vulnerability in the issue notification feature. The affected versions are before version 8.19.0. |
2021-09-01 |
not yet calculated |
CVE-2021-39119
MISC |
atlassian — jira_service_management_server
|
Affected versions of Atlassian Jira Service Management Server and Data Center allow remote attackers with “Jira Administrators” access to execute arbitrary Java code or run arbitrary system commands via a Server_Side Template Injection vulnerability in the Email Template feature. The affected versions are before version 4.13.9, and from version 4.14.0 before 4.18.0. |
2021-09-01 |
not yet calculated |
CVE-2021-39115
N/A |
axios — axios
|
axios is vulnerable to Inefficient Regular Expression Complexity |
2021-08-31 |
not yet calculated |
CVE-2021-3749
MISC
CONFIRM |
benq — smart_wireless_conference_projector
|
The management interface of BenQ smart wireless conference projector does not properly control user’s privilege. Attackers can access any system directory of this device through the interface and execute arbitrary commands if he enters the local subnetwork. |
2021-08-30 |
not yet calculated |
CVE-2021-37911
MISC |
bludit — bludit
|
bludit v3.13.0 contains an arbitrary file deletion vulnerability in the backup plugin via the `deleteBackup’ parameter. |
2021-09-01 |
not yet calculated |
CVE-2020-20495
MISC |
bookstack — bookstack
|
bookstack is vulnerable to Server-Side Request Forgery (SSRF) |
2021-09-02 |
not yet calculated |
CVE-2021-3758
MISC
CONFIRM |
brave — browser_desktop
|
An information disclosure exists in Brave Browser Desktop prior to version 1.28.62, where logged warning messages that included timestamps of connections to V2 onion domains in tor.log. |
2021-08-31 |
not yet calculated |
CVE-2021-22929
MISC |
| cacti — cacti |
Multiple Cross Site Scripting (XSS) vulneratiblities exist in Cacti 1.2.12 in (1) reports_admin.php, (2) data_queries.php, (3) data_input.php, (4) graph_templates.php, (5) graphs.php, (6) reports_admin.php, and (7) data_input.php. |
2021-08-27 |
not yet calculated |
CVE-2020-23226
MISC |
| cannon — multiple_devices |
Certain Canon devices manufactured in 2012 through 2020 (such as imageRUNNER ADVANCE iR-ADV C5250), when Catwalk Server is enabled for HTTP access, allow remote attackers to modify an e-mail address setting, and thus cause the device to send sensitive information through e-mail to the attacker. For example, an incoming FAX may be sent through e-mail to the attacker. This occurs when a PIN is not required for General User Mode, as exploited in the wild in August 2021. |
2021-08-29 |
not yet calculated |
CVE-2021-38154
MISC
MISC |
| cgal_libcgal — cgal_libcgal |
A code execution vulnerability exists in the Nef polygon-parsing functionality of CGAL libcgal CGAL-5.1.1. An oob read vulnerability exists in Nef_S2/SNC_io_parser.h SNC_io_parser<EW>::read_sface() sfh->boundary_entry_objects Sloop_of. A specially crafted malformed file can lead to an out-of-bounds read and type confusion, which could lead to code execution. An attacker can provide malicious input to trigger this vulnerability. |
2021-08-30 |
not yet calculated |
CVE-2020-35634
MISC |
cgal_libcgal — cgal_libcgal
|
A code execution vulnerability exists in the Nef polygon-parsing functionality of CGAL libcgal CGAL-5.1.1 in Nef_S2/SNC_io_parser.h SNC_io_parser::read_sface() store_sm_boundary_item() Sloop_of OOB read. A specially crafted malformed file can lead to an out-of-bounds read and type confusion, which could lead to code execution. An attacker can provide malicious input to trigger this vulnerability. |
2021-08-30 |
not yet calculated |
CVE-2020-35635
MISC |
| cgal_libcgal — cgal_libcgal |
A code execution vulnerability exists in the Nef polygon-parsing functionality of CGAL libcgal CGAL-5.1.1. An oob read vulnerability exists in Nef_S2/SNC_io_parser.h SNC_io_parser<EW>::read_sface() store_sm_boundary_item() Edge_of.A specially crafted malformed file can lead to an out-of-bounds read and type confusion, which could lead to code execution. An attacker can provide malicious input to trigger this vulnerability. |
2021-08-30 |
not yet calculated |
CVE-2020-35633
MISC |
christine_digital — dwu850-gs
|
webctrl.cgi.elf on Christie Digital DWU850-GS V06.46 devices allows attackers to perform any desired action via a crafted query containing an unspecified Cookie header. Authentication bypass can be achieved by including an administrative cookie that the device does not validate. |
2021-09-01 |
not yet calculated |
CVE-2021-40350
MISC |
cisco — enterprise_nfv_infrastructure_software
|
A vulnerability in the TACACS+ authentication, authorization and accounting (AAA) feature of Cisco Enterprise NFV Infrastructure Software (NFVIS) could allow an unauthenticated, remote attacker to bypass authentication and log in to an affected device as an administrator. This vulnerability is due to incomplete validation of user-supplied input that is passed to an authentication script. An attacker could exploit this vulnerability by injecting parameters into an authentication request. A successful exploit could allow the attacker to bypass authentication and log in as an administrator to the affected device. |
2021-09-02 |
not yet calculated |
CVE-2021-34746
CISCO |
| cisco — identity_services_engine_software |
A vulnerability in the web-based management interface of Cisco Identity Services Engine (ISE) Software could allow an authenticated, remote attacker with administrative credentials to conduct a cross-site scripting (XSS) attack against a user of the interface. This vulnerability exists because the web-based management interface does not properly validate user-supplied input. An attacker could exploit this vulnerability by injecting malicious code into specific pages of the interface. A successful exploit could allow the attacker to execute arbitrary script code in the context of the interface or access sensitive, browser-based information. To exploit this vulnerability, an attacker would need valid administrative credentials. |
2021-09-02 |
not yet calculated |
CVE-2021-34759
CISCO |
cisco — nexus_insights
|
A vulnerability in the web UI for Cisco Nexus Insights could allow an authenticated, remote attacker to view and download files related to the web application. The attacker requires valid device credentials. This vulnerability exists because proper role-based access control (RBAC) filters are not applied to file download actions. An attacker could exploit this vulnerability by logging in to the application and then navigating to the directory listing and download functions. A successful exploit could allow the attacker to download sensitive files that should be restricted, which could result in disclosure of sensitive information. |
2021-09-02 |
not yet calculated |
CVE-2021-34765
CISCO |
cisco — prime_collaboration_provisioning
|
A vulnerability in the web-based management interface of Cisco Prime Collaboration Provisioning could allow an unauthenticated, remote attacker to conduct a cross-site scripting (XSS) attack against a user of the interface. This vulnerability is due to insufficient validation of user-supplied input by the web-based management interface. An attacker could exploit this vulnerability by persuading a user of the interface to click a crafted link. A successful exploit could allow the attacker to execute arbitrary script code in the context of the interface or access sensitive, browser-based information. |
2021-09-02 |
not yet calculated |
CVE-2021-34732
CISCO |
cisco — prime_collaboration_provisioning
|
A vulnerability in the CLI of Cisco Prime Infrastructure and Cisco Evolved Programmable Network (EPN) Manager could allow an authenticated, local attacker to access sensitive information stored on the underlying file system of an affected system. This vulnerability exists because sensitive information is not sufficiently secured when it is stored. An attacker could exploit this vulnerability by gaining unauthorized access to sensitive information on an affected system. A successful exploit could allow the attacker to create forged authentication requests and gain unauthorized access to the affected system. |
2021-09-02 |
not yet calculated |
CVE-2021-34733
CISCO |
| compro — multiple_devices |
An issue was discovered on Compro IP70 2.08_7130218, IP570 2.08_7130520, IP60, and TN540 devices. rstp://…/medias2 does not require authorization. |
2021-09-01 |
not yet calculated |
CVE-2021-40379
MISC
MISC |
compro — multiple_devices
|
An issue was discovered on Compro IP70 2.08_7130218, IP570 2.08_7130520, IP60, and TN540 devices. /cgi-bin/support/killps.cgi deletes all data from the device. |
2021-09-01 |
not yet calculated |
CVE-2021-40378
MISC
MISC |
compro — multiple_devices
|
An issue was discovered on Compro IP70 2.08_7130218, IP570 2.08_7130520, IP60, and TN540 devices. cameralist.cgi and setcamera.cgi disclose credentials. |
2021-09-01 |
not yet calculated |
CVE-2021-40380
MISC
MISC |
| compro — multiple_devices |
An issue was discovered on Compro IP70 2.08_7130218, IP570 2.08_7130520, IP60, and TN540 devices. index_MJpeg.cgi allows video access. |
2021-09-01 |
not yet calculated |
CVE-2021-40381
MISC
MISC |
compro — multiple_devices
|
An issue was discovered on Compro IP70 2.08_7130218, IP570 2.08_7130520, IP60, and TN540 devices. mjpegStreamer.cgi allows video screenshot access. |
2021-09-01 |
not yet calculated |
CVE-2021-40382
MISC
MISC |
| craigms — craigms |
An issue in craigms/main.php of CraigMS 1.0 allows attackers to execute arbitrary commands via a crafted input entered into the DB Name field. |
2021-09-02 |
not yet calculated |
CVE-2020-18048
MISC |
| createlabelorattrib — createlabelorattrib |
A memory corruption vulnerability exists in the XML-parsing CreateLabelOrAttrib functionality of AT&T Labs’ Xmill 0.7. A specially crafted XML file can lead to a heap buffer overflow. An attacker can provide a malicious file to trigger this vulnerability. |
2021-08-31 |
not yet calculated |
CVE-2021-21811
MISC |
| cscms — cscms |
A remote code execution (RCE) vulnerability in the Playsong.php component of cscms v4.1 allows attackers to execute arbitrary commands. |
2021-08-30 |
not yet calculated |
CVE-2020-22848
MISC |
| cyberark — credential_provider |
An inadequate encryption vulnerability discovered in CyberArk Credential Provider before 12.1 may lead to Information Disclosure. An attacker may realistically have enough information that the number of possible keys (for a credential file) is only one, and the number is usually not higher than 2^36. |
2021-09-02 |
not yet calculated |
CVE-2021-31796
MISC
MISC
MISC
MISC |
| cyberark — credential_provider |
The effective key space used to encrypt the cache in CyberArk Credential Provider prior to 12.1 has low entropy, and under certain conditions a local malicious user can obtain the plaintext of cache files. |
2021-09-02 |
not yet calculated |
CVE-2021-31798
MISC
MISC
MISC
MISC |
cyberark — credential_provider
|
The user identification mechanism used by CyberArk Credential Provider prior to 12.1 is susceptible to a local host race condition, leading to password disclosure. |
2021-09-02 |
not yet calculated |
CVE-2021-31797
MISC
MISC
MISC
MISC |
cyberark — identity
|
CyberArk Identity 21.5.131, when handling an invalid authentication attempt, sometimes reveals whether the username is valid. In certain authentication policy configurations with MFA, the API response length can be used to differentiate between a valid user and an invalid one (aka Username Enumeration). Response differentiation enables attackers to enumerate usernames of valid application users. Attackers can use this information to leverage brute-force and dictionary attacks in order to discover valid account information such as passwords. |
2021-09-01 |
not yet calculated |
CVE-2021-37151
MISC
MISC |
cyrus — imap
|
Cyrus IMAP before 3.4.2 allows remote attackers to cause a denial of service (multiple-minute daemon hang) via input that is mishandled during hash-table interaction. Because there are many insertions into a single bucket, strcmp becomes slow. This is fixed in 3.4.2, 3.2.8, and 3.0.16. |
2021-09-01 |
not yet calculated |
CVE-2021-33582
MISC
MISC
CONFIRM
MISC |
| delta_electronics — diaenergie |
A Blind SQL injection vulnerability exists in the /DataHandler/HandlerAlarmGroup.ashx endpoint of Delta Electronics DIAEnergie Version 1.7.5 and prior. The application does not properly validate the user-controlled value supplied through the parameter agid before using it as part of an SQL query. A remote, unauthenticated attacker can exploit this issue to execute arbitrary code in the context of NT SERVICEMSSQLSERVER. |
2021-08-30 |
not yet calculated |
CVE-2021-38393
MISC |
delta_electronics — diaenergie
|
A Blind SQL injection vulnerability exists in the /DataHandler/HandlerEnergyType.ashx endpoint of Delta Electronics DIAEnergie Version 1.7.5 and prior. The application does not properly validate the user-controlled value supplied through the parameter egyid before using it as part of an SQL query. A remote, unauthenticated attacker can exploit this issue to execute arbitrary code in the context of NT SERVICEMSSQLSERVER. |
2021-08-30 |
not yet calculated |
CVE-2021-38390
MISC |
| delta_electronics — diaenergie |
A Blind SQL injection vulnerability exists in the /DataHandler/AM/AM_Handler.ashx endpoint of Delta Electronics DIAEnergie Version 1.7.5 and prior. The application does not properly validate the user-controlled value supplied through the parameter type before using it as part of an SQL query. A remote, unauthenticated attacker can exploit this issue to execute arbitrary code in the context of NT SERVICEMSSQLSERVER. |
2021-08-30 |
not yet calculated |
CVE-2021-38391
MISC |
detect-character-encoding — detect-character-encoding
|
detect-character-encoding is a package for detecting character encoding using ICU. In detect-character-encoding v0.3.0 and earlier, allocated memory is not released. The problem has been patched in detect-character-encoding v0.3.1. |
2021-08-31 |
not yet calculated |
CVE-2021-39176
CONFIRM
MISC
MISC
MISC |
django — django
|
Total.js framework (npm package total.js) is a framework for Node.js platfrom written in pure JavaScript similar to PHP’s Laravel or Python’s Django or ASP.NET MVC. In total.js framework before version 3.4.9, calling the utils.set function with user-controlled values leads to code-injection. This can cause a variety of impacts that include arbitrary code execution. This is fixed in version 3.4.9. |
2021-08-30 |
not yet calculated |
CVE-2021-32831
MISC
MISC
MISC
CONFIRM |
drk — odenwaldkreis_testerfassung
|
Multiple cross-site scripting (XSS) vulnerabilities in DRK Odenwaldkreis Testerfassung March-2021 allow remote attackers to inject arbitrary web script or HTML via all parameters to HTML form fields in all components. |
2021-08-30 |
not yet calculated |
CVE-2021-35061
MISC |
drk — odenwaldkreis_testerfassung
|
A Shell Metacharacter Injection vulnerability in result.php in DRK Odenwaldkreis Testerfassung March-2021 allow an attacker with a valid token of a COVID-19 test result to execute shell commands with the permissions of the web server. |
2021-08-30 |
not yet calculated |
CVE-2021-35062
MISC |
| easycorp — zentao |
A cross site scripting (XSS) issue in EasyCorp ZenTao 12.5.3 allows remote attackers to execute arbitrary web script via various areas such as data-link-creator. |
2021-08-31 |
not yet calculated |
CVE-2021-27558
MISC |
easycorp — zentao
|
A cross-site request forgery (CSRF) vulnerability in the Cron job tab in EasyCorp ZenTao 12.5.3 allows attackers to update the fields of a Cron job. |
2021-08-31 |
not yet calculated |
CVE-2021-27557
MISC |
eclipse — mosquitto
|
In Eclipse Mosquitto versions 2.0 to 2.0.11, when using the dynamic security plugin, if the ability for a client to make subscriptions on a topic is revoked when a durable client is offline, then existing subscriptions for that client are not revoked. |
2021-08-30 |
not yet calculated |
CVE-2021-34434
CONFIRM |
| eclipse – theia |
In Eclipse Theia 0.1.1 to 0.2.0, it is possible to exploit the default build to obtain remote code execution (and XXE) via the theia-xml-extension. This extension uses lsp4xml (recently renamed to LemMinX) in order to provide language support for XML. This is installed by default. |
2021-09-02 |
not yet calculated |
CVE-2021-34436
CONFIRM |
eclipse – theia
|
In Eclipse Theia 0.3.9 to 1.8.1, the “mini-browser” extension allows a user to preview HTML files in an iframe inside the IDE. But with the way it is made it is possible for a previewed HTML file to trigger an RCE. This exploit only happens if a user previews a malicious file.. |
2021-09-01 |
not yet calculated |
CVE-2021-34435
CONFIRM |
edgegallery — edgegallery
|
An issue was discovered in EdgeGallery/developer before v1.0. There is a “Deserialization of yaml file” vulnerability that can allow attackers to execute system command through uploading the malicious constructed YAML file. |
2021-08-30 |
not yet calculated |
CVE-2021-34066
MISC |
elfinder.netcore — elfinder.netcore
|
This affects all versions of package elFinder.NetCore. The Path.Combine(…) method is used to create an absolute file path. Due to missing sanitation of the user input and a missing check of the generated path its possible to escape the Files directory via path traversal |
2021-09-01 |
not yet calculated |
CVE-2021-23428
MISC
MISC
MISC |
elfinder.netcore — elfinder.netcore
|
This affects all versions of package elFinder.NetCore. The ExtractAsync function within the FileSystem is vulnerable to arbitrary extraction due to insufficient validation. |
2021-09-01 |
not yet calculated |
CVE-2021-23427
MISC
MISC |
| filebrowser — filebrowser |
A stored cross-site scripting (XSS) vulnerability exists in FileBrowser < v2.16.0 that allows an authenticated user authorized to upload a malicious .svg file which acts as a stored XSS payload. If this stored XSS payload is triggered by an administrator it will trigger malicious OS commands on the server running the FileBrowser instance. |
2021-08-31 |
not yet calculated |
CVE-2021-37794
MISC
MISC
MISC |
| form_tools — form_tools |
An issue was discovered in Form Tools through 3.0.20. SQL Injection can occur via the export_group_id field when a low-privileged user (client) tries to export a form with data, e.g., manipulation of modules/export_manager/export.php?export_group_id=1&export_group_1_results=all&export_type_id=1. |
2021-08-31 |
not yet calculated |
CVE-2021-38145
MISC
MISC
MISC
MISC |
form_tools — form_tools
|
An issue was discovered in Form Tools through 3.0.20. A low-privileged user can trigger Reflected XSS when a viewing a form via the submission_id parameter, e.g., clients/forms/edit_submission.php?form_id=1&view_id=1&submission_id=[XSS]. |
2021-08-31 |
not yet calculated |
CVE-2021-38144
MISC
MISC
MISC
MISC |
form_tools — form_tools
|
An issue was discovered in Form Tools through 3.0.20. When an administrator creates a customer account, it is possible for the customer to log in and proceed with a change of name and last name. However, these fields are vulnerable to XSS payload insertion, being triggered in the admin panel when the admin tries to see the client list. This type of XSS (stored) can lead to the extraction of the PHPSESSID cookie belonging to the admin. |
2021-08-31 |
not yet calculated |
CVE-2021-38143
MISC
MISC
MISC
MISC |
| freebsd — multiple_products |
In FreeBSD 13.0-STABLE before n246941-20f96f215562, 12.2-STABLE before r370400, 11.4-STABLE before r370399, 13.0-RELEASE before p4, 12.2-RELEASE before p10, and 11.4-RELEASE before p13, certain VirtIO-based device models in bhyve failed to handle errors when fetching I/O descriptors. A malicious guest may cause the device model to operate on uninitialized I/O vectors leading to memory corruption, crashing of the bhyve process, and possibly arbitrary code execution in the bhyve process. |
2021-08-30 |
not yet calculated |
CVE-2021-29631
MISC |
freebsd — multiple_products
|
In FreeBSD 13.0-STABLE before n246938-0729ba2f49c9, 12.2-STABLE before r370383, 11.4-STABLE before r370381, 13.0-RELEASE before p4, 12.2-RELEASE before p10, and 11.4-RELEASE before p13, the ggatec daemon does not validate the size of a response before writing it to a fixed-sized buffer allowing a malicious attacker in a privileged network position to overwrite the stack of ggatec and potentially execute arbitrary code. |
2021-08-30 |
not yet calculated |
CVE-2021-29630
MISC |
| frontier — frontier |
Frontier is Substrate’s Ethereum compatibility layer. Prior to commit number 0b962f218f0cdd796dadfe26c3f09e68f7861b26, a bug in `pallet-ethereum` can cause invalid transactions to be included in the Ethereum block state in `pallet-ethereum` due to not validating the input data size. Any invalid transactions included this way have no possibility to alter the internal Ethereum or Substrate state. The transaction will appear to have be included, but is of no effect as it is rejected by the EVM engine. The impact is further limited by Substrate extrinsic size constraints. A patch is available in commit number 0b962f218f0cdd796dadfe26c3f09e68f7861b26. There are no workarounds aside from applying the patch. |
2021-09-03 |
not yet calculated |
CVE-2021-39193
MISC
MISC
CONFIRM
MISC |
ghost — ghost
|
Ghost is a Node.js content management system. An error in the implementation of the limits service between versions 4.0.0 and 4.9.4 allows all authenticated users (including contributors) to view admin-level API keys via the integrations API endpoint, leading to a privilege escalation vulnerability. This issue is patched in Ghost version 4.10.0. As a workaround, disable all non-Administrator accounts to prevent API access. It is highly recommended to regenerate all API keys after patching or applying the workaround. |
2021-09-03 |
not yet calculated |
CVE-2021-39192
CONFIRM
MISC |
gibbon — gibbon
|
A reflected XSS vulnerability exists in multiple pages in version 22 of the Gibbon application that allows for arbitrary execution of JavaScript (gibbonCourseClassID, gibbonPersonID, subpage, currentDate, or allStudents to index.php). |
2021-09-03 |
not yet calculated |
CVE-2021-40492
MISC
MISC |
| git — git_connect_git |
git_connect_git in connect.c in Git before 2.30.1 allows a repository path to contain a newline character, which may result in unexpected cross-protocol requests, as demonstrated by the git://localhost:1234/%0d%0a%0d%0aGET%20/%20HTTP/1.1 substring. |
2021-08-31 |
not yet calculated |
CVE-2021-40330
MISC
MISC |
| globalnewsfiles — globalnewsfiles |
GlobalNewFiles is a package in Miraheze, a wiki hosting service. Prior to commit number cee254e1b158cdb0ddbea716b1d3edc31fa4fb5d, the username column of the GlobalNewFiles special page is vulnerable to a stored XSS. Commit number cee254e1b158cdb0ddbea716b1d3edc31fa4fb5d contains a patch. As a workaround, one may disallow <,> (or other characters required to insert html/js) from being used in account names so an XSS is not possible. |
2021-09-01 |
not yet calculated |
CVE-2021-39186
CONFIRM
MISC
MISC |
| google — chrome |
Use after free in Base internals in Google Chrome prior to 93.0.4577.63 allowed a remote attacker to potentially exploit heap corruption via a crafted HTML page. |
2021-09-03 |
not yet calculated |
CVE-2021-30613
MISC
MISC |
| google — chrome |
Use after free in WebRTC in Google Chrome on Linux, ChromeOS prior to 93.0.4577.63 allowed an attacker who convinced a user to install a malicious extension to potentially exploit heap corruption via a crafted HTML page. |
2021-09-03 |
not yet calculated |
CVE-2021-30611
MISC
MISC |
| google — chrome |
Use after free in Web Share in Google Chrome prior to 93.0.4577.63 allowed a remote attacker to potentially exploit heap corruption via a crafted HTML page. |
2021-09-03 |
not yet calculated |
CVE-2021-30608
MISC
MISC |
| google — chrome |
Inappropriate implementation in DevTools in Google Chrome prior to 93.0.4577.63 allowed a remote attacker who had convinced the user to use Chrome headless with remote debugging to execute arbitrary code via a crafted HTML page. |
2021-09-03 |
not yet calculated |
CVE-2021-30618
MISC
MISC |
| google — chrome |
Use after free in Bookmarks in Google Chrome prior to 93.0.4577.63 allowed an attacker who convinced a user to install a malicious extension to potentially exploit heap corruption via a crafted HTML page. |
2021-09-03 |
not yet calculated |
CVE-2021-30623
MISC
MISC |
| google — chrome |
Inappropriate implementation in Autofill in Google Chrome prior to 93.0.4577.63 allowed a remote attacker to spoof security UI via a crafted HTML page. |
2021-09-03 |
not yet calculated |
CVE-2021-30621
MISC
MISC |
| google — chrome |
Use after free in Media in Google Chrome prior to 93.0.4577.63 allowed a remote attacker to potentially exploit heap corruption via a crafted HTML page. |
2021-09-03 |
not yet calculated |
CVE-2021-30616
MISC
MISC |
google — chrome
|
Use after free in WebRTC in Google Chrome on Linux, ChromeOS prior to 93.0.4577.63 allowed an attacker who convinced a user to install a malicious extension to potentially exploit heap corruption via a crafted HTML page. |
2021-09-03 |
not yet calculated |
CVE-2021-30612
MISC
MISC |
| google — chrome |
Heap buffer overflow in TabStrip in Google Chrome prior to 93.0.4577.63 allowed an attacker who convinced a user to install a malicious extension to potentially exploit heap corruption via a crafted HTML page. |
2021-09-03 |
not yet calculated |
CVE-2021-30614
MISC
MISC |
| google — chrome |
Use after free in Blink in Google Chrome prior to 93.0.4577.63 allowed an attacker who convinced a user to drag and drop a malicous folder to a page to potentially perform a sandbox escape via a crafted HTML page. |
2021-09-03 |
not yet calculated |
CVE-2021-30606
MISC
MISC |
google — chrome
|
Policy bypass in Blink in Google Chrome prior to 93.0.4577.63 allowed a remote attacker to bypass site isolation via a crafted HTML page. |
2021-09-03 |
not yet calculated |
CVE-2021-30617
MISC
MISC |
google — chrome
|
Use after free in Autofill in Google Chrome prior to 93.0.4577.63 allowed a remote attacker to potentially exploit heap corruption via a crafted HTML page. |
2021-09-03 |
not yet calculated |
CVE-2021-30624
MISC
MISC |
| google — chrome |
Use after free in WebApp Installs in Google Chrome prior to 93.0.4577.63 allowed an attacker who convinced a user to install a malicious extension to potentially exploit heap corruption via a crafted HTML page. |
2021-09-03 |
not yet calculated |
CVE-2021-30622
MISC
MISC |
google — chrome
|
Inappropriate implementation in Navigation in Google Chrome prior to 93.0.4577.63 allowed a remote attacker to leak cross-origin data via a crafted HTML page. |
2021-09-03 |
not yet calculated |
CVE-2021-30615
MISC
MISC |
google — chrome
|
Use after free in Extensions API in Google Chrome prior to 93.0.4577.63 allowed a remote attacker to potentially exploit heap corruption via a crafted HTML page. |
2021-09-03 |
not yet calculated |
CVE-2021-30610
MISC
MISC |
google — chrome
|
Inappropriate implementation in Autofill in Google Chrome prior to 93.0.4577.63 allowed a remote attacker to spoof security UI via a crafted HTML page. |
2021-09-03 |
not yet calculated |
CVE-2021-30619
MISC
MISC |
google — chrome
|
Use after free in Permissions in Google Chrome prior to 93.0.4577.63 allowed a remote attacker who had compromised the renderer process to potentially exploit heap corruption via a crafted HTML page. |
2021-09-03 |
not yet calculated |
CVE-2021-30607
MISC
MISC |
google — chrome
|
Insufficient policy enforcement in Blink in Google Chrome prior to 93.0.4577.63 allowed a remote attacker to bypass content security policy via a crafted HTML page. |
2021-09-03 |
not yet calculated |
CVE-2021-30620
MISC
MISC |
google — chrome
|
Use after free in Sign-In in Google Chrome prior to 93.0.4577.63 allowed a remote attacker to potentially exploit heap corruption via a crafted HTML page. |
2021-09-03 |
not yet calculated |
CVE-2021-30609
MISC
MISC |
gp — pro_ex
|
A CWE-427: Uncontrolled Search Path Element vulnerability exists in GP-Pro EX,V4.09.250 and prior, that could cause local code execution with elevated privileges when installing the software. |
2021-09-02 |
not yet calculated |
CVE-2021-22775
MISC |
gyser — geyser
|
Geyser is a bridge between Minecraft: Bedrock Edition and Minecraft: Java Edition. Versions of Geyser prior to 1.4.2-SNAPSHOT allow anyone that can connect to the server to forge a LoginPacket with manipulated JWT token allowing impersonation as any user. Version 1.4.2-SNAPSHOT contains a patch for the issue. There are no known workarounds aside from upgrading. |
2021-08-30 |
not yet calculated |
CVE-2021-39177
CONFIRM
MISC
MISC |
hashicorp — vault_enterprise
|
HashiCorp Vault Enterprise 0.9.2 through 1.6.2 allowed the read of license metadata from DR secondaries without authentication. Fixed in 1.6.3. |
2021-08-31 |
not yet calculated |
CVE-2021-27668
MISC |
hedgedoc — hedgedoc
|
HedgeDoc is a platform to write and share markdown. In versions prior to 1.9.0, an unauthenticated attacker can inject arbitrary JavaScript into the speaker-notes of the slide-mode feature by embedding an iframe hosting the malicious code into the slides or by embedding the HedgeDoc instance into another page. The problem is patched in version 1.9.0. There are no known workarounds aside from upgrading. |
2021-08-30 |
not yet calculated |
CVE-2021-39175
MISC
MISC
MISC
CONFIRM |
http4s — http4s
|
Http4s is a minimal, idiomatic Scala interface for HTTP services. In http4s versions 0.21.26 and prior, 0.22.0 through 0.22.2, 0.23.0, 0.23.1, and 1.0.0-M1 through 1.0.0-M24, the default CORS configuration is vulnerable to an origin reflection attack. The middleware is also susceptible to a Null Origin Attack. The problem is fixed in 0.21.27, 0.22.3, 0.23.2, and 1.0.0-M25. The original `CORS` implementation and `CORSConfig` are deprecated. See the GitHub GHSA for more information, including code examples and workarounds. |
2021-09-01 |
not yet calculated |
CVE-2021-39185
CONFIRM
MISC |
| ibm — openpages |
IBM OpenPages with Watson 8.1 and 8.2 could allow an authenticated user to upload a file that could execute arbitrary code on the system. IBM X-Force ID: 207633. |
2021-08-31 |
not yet calculated |
CVE-2021-29907
CONFIRM
XF |
ibm — planning_analytics
|
IBM Planning Analytics 2.0 could allow a remote attacker to obtain sensitive information when a stack trace is returned in the browser. IBM X-Force ID: 205527. |
2021-09-01 |
not yet calculated |
CVE-2021-29851
CONFIRM
XF |
| ibm — planning_analytics |
IBM Planning Analytics 2.0 could expose information that could be used to to create attacks by not validating the return values from some methods or functions. IBM X-Force ID: 205529. |
2021-09-01 |
not yet calculated |
CVE-2021-29853
XF
CONFIRM |
ibm — planning_analytics
|
IBM Planning Analytics 2.0 is vulnerable to cross-site scripting. This vulnerability allows users to embed arbitrary JavaScript code in the Web UI thus altering the intended functionality potentially leading to credentials disclosure within a trusted session. IBM X-Force ID: 205528. |
2021-09-01 |
not yet calculated |
CVE-2021-29852
XF
CONFIRM |
| iec104 — iec104 |
IEC104 v1.0 contains a stack-buffer overflow in the parameter Iec10x_Sta_Addr. |
2021-08-31 |
not yet calculated |
CVE-2020-20486
MISC |
immer — immer
|
immer is vulnerable to Improperly Controlled Modification of Object Prototype Attributes (‘Prototype Pollution’) |
2021-09-02 |
not yet calculated |
CVE-2021-3757
CONFIRM
MISC |
immer — immer
|
This affects the package immer before 9.0.6. A type confusion vulnerability can lead to a bypass of CVE-2020-28477 when the user-provided keys used in the path parameter are arrays. In particular, this bypass is possible because the condition (p === “__proto__” || p === “constructor”) in applyPatches_ returns false if p is [‘__proto__’] (or [‘constructor’]). The === operator (strict equality operator) returns false if the operands have different type. |
2021-09-01 |
not yet calculated |
CVE-2021-23436
MISC
MISC
MISC |
| inetutils — inetutils |
The ftp client in GNU Inetutils before 2.2 does not validate addresses returned by PASV/LSPV responses to make sure they match the server address. This is similar to CVE-2020-8284 for curl. |
2021-09-03 |
not yet calculated |
CVE-2021-40491
MISC
MISC
MISC |
iportalis — ics
|
An issue was discovered in iPortalis iCS 7.1.13.0. Attackers can send a sequence of requests to rapidly cause .NET Input Validation errors. This increases the size of the log file on the remote server until memory is exhausted, therefore consuming the maximum amount of resources (triggering a denial of service condition). |
2021-09-01 |
not yet calculated |
CVE-2020-9000
MISC
MISC |
iportalis — ics
|
An issue was discovered in iPortalis iCS 7.1.13.0. An attacker can gain privileges by intercepting a request and changing UserRoleKey=COMPANY_ADMIN to UserRoleKey=DOMAIN_ADMIN (to achieve Domain Administrator access). |
2021-09-01 |
not yet calculated |
CVE-2020-9002
MISC
MISC |
| ivanti — workspace |
An issue was discovered in Ivanti Workspace Control before 10.6.30.0. A locally authenticated user with low privileges can bypass File and Folder Security by leveraging an unspecified attack vector. As a result, the attacker can start applications with elevated privileges. |
2021-09-01 |
not yet calculated |
CVE-2021-36235
MISC |
| iwebshop — iwebshop |
Cross Site Request Forgey (CSRF) in iWebShop v5.3 allows remote atatckers to execute arbitrary code via malicious POST request to the component ‘/index.php?controller=system&action=admin_edit_act’. |
2021-08-31 |
not yet calculated |
CVE-2020-19047
MISC |
| jenkins — azure_ad_plugin |
Jenkins Azure AD Plugin 179.vf6841393099e and earlier allows attackers to craft URLs that would bypass the CSRF protection of any target URL in Jenkins. |
2021-08-31 |
not yet calculated |
CVE-2021-21679
CONFIRM
MLIST |
| jenkins — code_coverage_appi_plugin |
Jenkins Code Coverage API Plugin 1.4.0 and earlier does not apply Jenkins JEP-200 deserialization protection to Java objects it deserializes from disk, resulting in a remote code execution vulnerability. |
2021-08-31 |
not yet calculated |
CVE-2021-21677
CONFIRM
MLIST |
jenkins — nested_view_plugin
|
Jenkins Nested View Plugin 1.20 and earlier does not configure its XML transformer to prevent XML external entity (XXE) attacks. |
2021-08-31 |
not yet calculated |
CVE-2021-21680
CONFIRM
MLIST |
jenkins — saml_plugin
|
Jenkins SAML Plugin 2.0.7 and earlier allows attackers to craft URLs that would bypass the CSRF protection of any target URL in Jenkins. |
2021-08-31 |
not yet calculated |
CVE-2021-21678
CONFIRM
MLIST |
| jenkins — nomad_plugin |
Jenkins Nomad Plugin 0.7.4 and earlier stores Docker passwords unencrypted in the global config.xml file on the Jenkins controller where they can be viewed by users with access to the Jenkins controller file system. |
2021-08-31 |
not yet calculated |
CVE-2021-21681
CONFIRM
MLIST |
jforum2 — jforum2
|
ViewCommon.java in JForum2 2.7.0 allows XSS via a user signature. |
2021-09-04 |
not yet calculated |
CVE-2021-40509
MISC
MISC |
| johnson_controls — cem_systems_ac2000 |
A vulnerability in versions 10.1 through 10.5 of Johnson Controls CEM Systems AC2000 allows a remote attacker to access to the system without adequate authorization. This issue affects: Johnson Controls CEM Systems AC2000 10.1; 10.2; 10.3; 10.4; 10.5. |
2021-08-30 |
not yet calculated |
CVE-2021-27663
CERT
CONFIRM |
kaseya — unitrends_backup_software
|
An issue was discovered in the server software in Kaseya Unitrends Backup Software before 10.5.5-2. There is authenticated remote code execution. |
2021-09-01 |
not yet calculated |
CVE-2021-40387
MISC |
kaseya — unitrends_backup_software
|
An issue was discovered in the server software in Kaseya Unitrends Backup Software before 10.5.5-2. There is a privilege escalation from read-only user to admin. |
2021-09-01 |
not yet calculated |
CVE-2021-40385
MISC |
| kpn_experia — wifi_devices |
Wireless devices running certain Arcadyan-derived firmware (such as KPN Experia WiFi 1.00.15) do not properly sanitise user input to the syslog configuration form. An authenticated remote attacker could leverage this to alter the device configuration and achieve remote code execution. This can be exploited in conjunction with CVE-2021-20090. |
2021-09-01 |
not yet calculated |
CVE-2021-38703
MISC
MISC |
| kramer — viaware |
KRAMER VIAware through August 2021 allows remote attackers to execute arbitrary code because ajaxPages/writeBrowseFilePathAjax.php accepts arbitrary executable pathnames (even though browseSystemFiles.php is no longer reachable via the GUI). NOTE: this issue exists because of an incomplete fix for CVE-2019-17124. |
2021-08-31 |
not yet calculated |
CVE-2021-36356
MISC |
| libiec_iccp_mod — libiec_iccp_mod |
A heap buffer-overflow in the client_example1.c component of libiec_iccp_mod v1.5 leads to a denial of service (DOS). |
2021-08-31 |
not yet calculated |
CVE-2020-20490
MISC |
libjxl — libjxl
|
libjxl v0.5.0 is affected by a Assertion failed issue in lib/jxl/image.cc jxl::PlaneBase::PlaneBase(). When encoding a malicous GIF file using cjxl, an attacker can trigger a denial of service. |
2021-08-30 |
not yet calculated |
CVE-2021-36691
MISC |
libjxl — libjxl
|
libjxl v0.3.7 is affected by a Divide By Zero in issue in lib/extras/codec_apng.cc jxl::DecodeImageAPNG(). When encoding a malicous APNG file using cjxl, an attacker can trigger a denial of service. |
2021-08-30 |
not yet calculated |
CVE-2021-36692
MISC
MISC
MISC |
libsolv — libsolv
|
Buffer overflow vulnerability in function pool_installable_whatprovides in src/repo.h in libsolv before 0.7.17 allows attackers to cause a Denial of Service. |
2021-09-02 |
not yet calculated |
CVE-2021-33930
MISC |
| libsolv — libsolv |
Buffer overflow vulnerability in function pool_disabled_solvable in src/repo.h in libsolv before 0.7.17 allows attackers to cause a Denial of Service. |
2021-09-02 |
not yet calculated |
CVE-2021-33929
MISC |
libsolv — libsolv
|
Buffer overflow vulnerability in function pool_installable in src/repo.h in libsolv before 0.7.17 allows attackers to cause a Denial of Service. |
2021-09-02 |
not yet calculated |
CVE-2021-33928
MISC |
libsolv — libsolv
|
Buffer overflow vulnerability in function prune_to_recommended in src/policy.c in libsolv before 0.7.17 allows attackers to cause a Denial of Service. |
2021-09-02 |
not yet calculated |
CVE-2021-33938
MISC |
| libssh — libssh |
A flaw has been found in libssh in versions prior to 0.9.6. The SSH protocol keeps track of two shared secrets during the lifetime of the session. One of them is called secret_hash and the other session_id. Initially, both of them are the same, but after key re-exchange, previous session_id is kept and used as an input to new secret_hash. Historically, both of these buffers had shared length variable, which worked as long as these buffers were same. But the key re-exchange operation can also change the key exchange method, which can be based on hash of different size, eventually creating “secret_hash” of different size than the session_id has. This becomes an issue when the session_id memory is zeroed or when it is used again during second key re-exchange. |
2021-08-31 |
not yet calculated |
CVE-2021-3634
MISC
DEBIAN |
linux — linux_kernel
|
NMSAccess32.exe in TeraRecon AQNetClient 4.4.13 allows attackers to execute a malicious binary with SYSTEM privileges via a low-privileged user account. To exploit this, a low-privileged user must change the service configuration or overwrite the binary service. |
2021-09-01 |
not yet calculated |
CVE-2021-35508
MISC
MISC |
linux — linux_kernel
|
A race condition was discovered in ext4_write_inline_data_end in fs/ext4/inline.c in the ext4 subsystem in the Linux kernel through 5.13.13. |
2021-09-03 |
not yet calculated |
CVE-2021-40490
MISC |
| magento — commerce |
Magento Commerce versions 2.4.2 (and earlier), 2.4.2-p1 (and earlier) and 2.3.7 (and earlier) are affected by an improper input validation vulnerability while saving a customer’s details with a specially crafted file. An authenticated attacker with admin privileges can leverage this vulnerability to achieve remote code execution. |
2021-09-01 |
not yet calculated |
CVE-2021-36025
MISC |
| magento — commerce |
Magento Commerce versions 2.4.2 (and earlier), 2.4.2-p1 (and earlier) and 2.3.7 (and earlier) are affected by an XML Injection vulnerability when saving a configurable product. An attacker with admin privileges can trigger a specially crafted script to achieve remote code execution. |
2021-09-01 |
not yet calculated |
CVE-2021-36028
MISC |
| magento — commerce |
Magento Commerce versions 2.4.2 (and earlier), 2.4.2-p1 (and earlier) and 2.3.7 (and earlier) are affected by a stored cross-site scripting vulnerability that could be abused by an attacker to inject malicious scripts into vulnerable form fields. Malicious JavaScript may be executed in a victim’s browser when they browse to the page containing the vulnerable field. |
2021-09-01 |
not yet calculated |
CVE-2021-36027
MISC |
| magento — commerce |
Magento Commerce versions 2.4.2 (and earlier), 2.4.2-p1 (and earlier) and 2.3.7 (and earlier) are affected by a stored cross-site scripting vulnerability in the customer address upload feature that could be abused by an attacker to inject malicious scripts into vulnerable form fields. Malicious JavaScript may be executed in a victim’s browser when they browse to the page containing the vulnerable field. |
2021-09-01 |
not yet calculated |
CVE-2021-36026
MISC |
| magento — commerce |
Magento Commerce versions 2.4.2 (and earlier), 2.4.2-p1 (and earlier) and 2.3.7 (and earlier) are affected by an Improper Neutralization of Special Elements Used In A Command via the Data collection endpoint. An attacker with admin privileges can upload a specially crafted file to achieve remote code execution. |
2021-09-01 |
not yet calculated |
CVE-2021-36024
MISC |
| magento — commerce |
Magento Commerce versions 2.4.2 (and earlier), 2.4.2-p1 (and earlier) and 2.3.7 (and earlier) are affected by a Path Traversal vulnerability via the `theme[preview_image]` parameter. An attacker with admin privileges could leverage this vulnerability to achieve remote code execution. |
2021-09-01 |
not yet calculated |
CVE-2021-36031
MISC |
| magento — commerce |
Magento Commerce versions 2.4.2 (and earlier), 2.4.2-p1 (and earlier) and 2.3.7 (and earlier) are affected by an improper input validation vulnerability. An attacker with admin privileges can upload a specially crafted file to bypass file extension restrictions and could lead to remote code execution. |
2021-09-01 |
not yet calculated |
CVE-2021-36040
MISC |
| magento — commerce |
Magento Commerce versions 2.4.2 (and earlier), 2.4.2-p1 (and earlier) and 2.3.7 (and earlier) are affected by an XML Injection vulnerability in the ‘City’ field. An unauthenticated attacker can trigger a specially crafted script to achieve remote code execution. |
2021-09-01 |
not yet calculated |
CVE-2021-36020
MISC |
| magento — commerce |
Magento Commerce versions 2.4.2 (and earlier), 2.4.2-p1 (and earlier) and 2.3.7 (and earlier) are affected by a blind SSRF vulnerability in the bundled dotmailer extension. An attacker with admin privileges could abuse this to achieve remote code execution should Redis be enabled. |
2021-09-01 |
not yet calculated |
CVE-2021-36043
MISC |
| magento — commerce |
Magento Commerce versions 2.4.2 (and earlier), 2.4.2-p1 (and earlier) and 2.3.7 (and earlier) are affected by an improper input validation vulnerability. An unauthenticated attacker could abuse this vulnerability to cause a server-side denial-of-service using a GraphQL field. |
2021-09-01 |
not yet calculated |
CVE-2021-36044
MISC |
| magento — commerce |
Magento Commerce versions 2.4.2 (and earlier), 2.4.2-p1 (and earlier) and 2.3.7 (and earlier) are affected by an improper input validation vulnerability in the Multishipping Module. An authenticated attacker could leverage this vulnerability to achieve sensitive information disclosure. |
2021-09-01 |
not yet calculated |
CVE-2021-36038
MISC |
| magento — commerce |
Magento Commerce versions 2.4.2 (and earlier), 2.4.2-p1 (and earlier) and 2.3.7 (and earlier) are affected by an XML Injection vulnerability in the Widgets Module. An attacker with admin privileges can trigger a specially crafted script to achieve remote code execution. |
2021-09-01 |
not yet calculated |
CVE-2021-36033
MISC |
| magento — commerce |
Magento Commerce versions 2.4.2 (and earlier), 2.4.2-p1 (and earlier) and 2.3.7 (and earlier) are affected by an improper input validation vulnerability in the API File Option Upload Extension. An attacker with Admin privileges can achieve unrestricted file upload which can result in remote code execution. |
2021-09-01 |
not yet calculated |
CVE-2021-36042
MISC |
| magento — commerce |
Magento Commerce versions 2.4.2 (and earlier), 2.4.2-p1 (and earlier) and 2.3.7 (and earlier) are affected by an XML Injection vulnerability in the Widgets Update Layout. An attacker with admin privileges can trigger a specially crafted script to achieve remote code execution. |
2021-09-01 |
not yet calculated |
CVE-2021-36022
MISC |
| magento — commerce |
Magento Commerce versions 2.4.2 (and earlier), 2.4.2-p1 (and earlier) and 2.3.7 (and earlier) are affected by an improper improper authorization vulnerability. An attacker with admin privileges could leverage this vulnerability to achieve remote code execution. |
2021-09-01 |
not yet calculated |
CVE-2021-36029
MISC |
| magento — commerce |
Magento Commerce versions 2.4.2 (and earlier), 2.4.2-p1 (and earlier) and 2.3.7 (and earlier) are affected by a business logic error in the placeOrder graphql mutation. An authenticated attacker can leverage this vulnerability to altar the price of an item. |
2021-09-01 |
not yet calculated |
CVE-2021-36012
MISC |
magento — commerce
|
Magento Commerce versions 2.4.2 (and earlier), 2.4.2-p1 (and earlier) and 2.3.7 (and earlier) are affected by an improper input validation vulnerability. An authenticated attacker can trigger an insecure direct object reference in the `V1/customers/me` endpoint to achieve information exposure and privilege escalation. |
2021-09-01 |
not yet calculated |
CVE-2021-36032
MISC |
| magento — commerce |
Magento Commerce versions 2.4.2 (and earlier), 2.4.2-p1 (and earlier) and 2.3.7 (and earlier) are affected by an improper improper authorization vulnerability. An authenticated attacker could leverage this vulnerability to achieve sensitive information disclosure. |
2021-09-01 |
not yet calculated |
CVE-2021-36037
MISC |
magento — commerce
|
Magento Commerce versions 2.4.2 (and earlier), 2.4.2-p1 (and earlier) and 2.3.7 (and earlier) are affected by an improper input validation vulnerability. An attacker with admin privileges can upload a specially crafted file to achieve remote code execution. |
2021-09-01 |
not yet calculated |
CVE-2021-36034
MISC |
magento — commerce
|
Magento Commerce versions 2.4.2 (and earlier), 2.4.2-p1 (and earlier) and 2.3.7 (and earlier) are affected by an improper input validation vulnerability. An attacker with admin privileges could make a crafted request to the Adobe Stock API to achieve remote code execution. |
2021-09-01 |
not yet calculated |
CVE-2021-36035
MISC |
| magento — commerce |
Magento Commerce versions 2.4.2 (and earlier), 2.4.2-p1 (and earlier) and 2.3.7 (and earlier) are affected by an improper input validation vulnerability. An attacker with admin privileges could upload a specially crafted file in the ‘pub/media` directory could lead to remote code execution. |
2021-09-01 |
not yet calculated |
CVE-2021-36041
MISC |
| magento — commerce |
Magento Commerce versions 2.4.2 (and earlier), 2.4.2-p1 (and earlier) and 2.3.7 (and earlier) are affected by an improper input validation vulnerability via the `quoteId` parameter. An attacker can abuse this vulnerability to disclose sensitive information. |
2021-09-01 |
not yet calculated |
CVE-2021-36039
MISC |
| magento — commerce |
Magento Commerce versions 2.4.2 (and earlier), 2.4.2-p1 (and earlier) and 2.3.7 (and earlier) are affected by an improper input validation vulnerability during the checkout process. An unauthenticated attacker can leverage this vulnerability to alter the price of items. |
2021-09-01 |
not yet calculated |
CVE-2021-36030
MISC |
mariadb — mariadb
|
A SQL injection vulnerability exists in version 8.0 of openSIS when MySQL or MariaDB is used as the application database. An attacker can then issue the SQL command through the index.php USERNAME parameter. NOTE: this issue may exist because of an incomplete fix for CVE-2020-6637. |
2021-09-01 |
not yet calculated |
CVE-2021-40353
MISC
MISC |
| matrix — matrix |
Matrix is an ecosystem for open federated Instant Messaging and Voice over IP. In versions 1.41.0 and prior, unauthorised users can access the name, avatar, topic and number of members of a room if they know the ID of the room. This vulnerability is limited to homeservers where the vulnerable homeserver is in the room and untrusted users are permitted to create groups (communities). By default, only homeserver administrators can create groups. However, homeserver administrators can already access this information in the database or using the admin API. As a result, only homeservers where the configuration setting `enable_group_creation` has been set to `true` are impacted. Server administrators should upgrade to 1.41.1 or higher to patch the vulnerability. There are two potential workarounds. Server administrators can set `enable_group_creation` to `false` in their homeserver configuration (this is the default value) to prevent creation of groups by non-administrators. Administrators that are using a reverse proxy could, with partial loss of group functionality, block the endpoints `/_matrix/client/r0/groups/{group_id}/rooms` and `/_matrix/client/unstable/groups/{group_id}/rooms`. |
2021-08-31 |
not yet calculated |
CVE-2021-39163
CONFIRM
MISC
MISC |
matrix — matrix
|
Matrix is an ecosystem for open federated Instant Messaging and Voice over IP. In versions 1.41.0 and prior, unauthorised users can access the membership (list of members, with their display names) of a room if they know the ID of the room. The vulnerability is limited to rooms with `shared` history visibility. Furthermore, the unauthorised user must be using an account on a vulnerable homeserver that is in the room. Server administrators should upgrade to 1.41.1 or later in order to receive the patch. One workaround is available. Administrators of servers that use a reverse proxy could, with potentially unacceptable loss of functionality, block the endpoints: `/_matrix/client/r0/rooms/{room_id}/members` with `at` query parameter, and `/_matrix/client/unstable/rooms/{room_id}/members` with `at` query parameter. |
2021-08-31 |
not yet calculated |
CVE-2021-39164
CONFIRM
MISC
MISC |
mautic — mautic
|
For Mautic versions prior to 3.3.4/4.0.0, there is an XSS vulnerability on Mautic’s password reset page where a vulnerable parameter, “bundle,” in the URL could allow an attacker to execute Javascript code. The attacker would be required to convince or trick the target into clicking a password reset URL with the vulnerable parameter utilized. |
2021-08-30 |
not yet calculated |
CVE-2021-27909
CONFIRM |
mautic — mautic
|
Insufficient sanitization / filtering allows for arbitrary JavaScript Injection in Mautic using the bounce management callback function. The values submitted in the “error” and “error_related_to” parameters of the POST request of the bounce management callback will be permanently stored and executed once the details page of an affected lead is opened by a Mautic user. An attacker with access to the bounce management callback function (identified with the Mailjet webhook, but it is assumed this will work uniformly across all kinds of webhooks) can inject arbitrary JavaScript Code into the “error” and “error_related_to” parameters of the POST request (POST /mailer/<product / webhook>/callback). It is noted that there is no authentication needed to access this function. The JavaScript Code is stored permanently in the web application and executed every time an authenticated user views the details page of a single contact / lead in Mautic. This means, arbitrary code can be executed to, e.g., steal or tamper with information. |
2021-08-30 |
not yet calculated |
CVE-2021-27910
CONFIRM |
mautic — mautic
|
Mautic versions before 3.3.4/4.0.0 are vulnerable to an inline JS XSS attack through the contact’s first or last name and triggered when viewing a contact’s details page then clicking on the action drop down and hovering over the Campaigns button. Contact first and last name can be populated from different sources such as UI, API, 3rd party syncing, forms, etc. |
2021-08-30 |
not yet calculated |
CVE-2021-27911
CONFIRM |
| microsoft — edge |
Microsoft Edge for iOS Spoofing Vulnerability |
2021-09-02 |
not yet calculated |
CVE-2021-38642
MISC |
microsoft — edge
|
Microsoft Edge for Android Information Disclosure Vulnerability |
2021-09-02 |
not yet calculated |
CVE-2021-26439
MISC |
| microsoft — edge |
Microsoft Edge (Chromium-based) Elevation of Privilege Vulnerability This CVE ID is unique from CVE-2021-36930. |
2021-09-02 |
not yet calculated |
CVE-2021-26436
MISC |
| microsoft — edge |
Microsoft Edge (Chromium-based) Elevation of Privilege Vulnerability This CVE ID is unique from CVE-2021-26436. |
2021-09-02 |
not yet calculated |
CVE-2021-36930
MISC |
| microsoft — edge |
Microsoft Edge for Android Spoofing Vulnerability |
2021-09-02 |
not yet calculated |
CVE-2021-38641
MISC |
midnight — commander
|
An issue was discovered in Midnight Commander through 4.8.26. When establishing an SFTP connection, the fingerprint of the server is neither checked nor displayed. As a result, a user connects to the server without the ability to verify its authenticity. |
2021-08-30 |
not yet calculated |
CVE-2021-36370
MISC
MISC
MISC
MISC |
| mik — starlight |
Deserialization of untrusted data in multiple functions in MIK.starlight 7.9.5.24363 allows authenticated remote attackers to execute operating system commands by crafting serialized objects. |
2021-08-31 |
not yet calculated |
CVE-2021-36231
MISC |
| mik — starlight |
Use of a hard-coded cryptographic key in MIK.starlight 7.9.5.24363 allows local users to decrypt credentials via unspecified vectors. |
2021-08-31 |
not yet calculated |
CVE-2021-36234
MISC
MISC |
| mik — starlight |
The function AdminGetFirstFileContentByFilePath in MIK.starlight 7.9.5.24363 allows (by design) an authenticated attacker to read arbitrary files from the filesystem by specifying the file path. |
2021-08-31 |
not yet calculated |
CVE-2021-36233
MISC |
mik — starlight
|
Improper Authorization in multiple functions in MIK.starlight 7.9.5.24363 allows an authenticated attacker to escalate privileges. |
2021-08-31 |
not yet calculated |
CVE-2021-36232
MISC |
| modicon — multiple_devices |
A CWE-119: Improper Restriction of Operations within the Bounds of a Memory Buffer vulnerability that could cause a Denial of Service on the Modicon PLC controller / simulator when updating the controller application with a specially crafted project file exists in Modicon M580 CPU (part numbers BMEP* and BMEH*, all versions), Modicon M340 CPU (part numbers BMXP34*, all versions), Modicon MC80 (part numbers BMKC80*, all versions), Modicon Momentum Ethernet CPU (part numbers 171CBU*, all versions), PLC Simulator for EcoStruxureª Control Expert, including all Unity Pro versions (former name of EcoStruxureª Control Expert, all versions), PLC Simulator for EcoStruxureª Process Expert including all HDCS versions (former name of EcoStruxureª Process Expert, all versions), Modicon Quantum CPU (part numbers 140CPU*, all versions), Modicon Premium CPU (part numbers TSXP5*, all versions). |
2021-09-02 |
not yet calculated |
CVE-2021-22789
MISC |
| modicon — multiple_devices |
A CWE-476: NULL Pointer Dereference vulnerability that could cause a Denial of Service on the Modicon PLC controller / simulator when updating the controller application with a specially crafted project file exists in Modicon M580 CPU (part numbers BMEP* and BMEH*, all versions), Modicon M340 CPU (part numbers BMXP34*, all versions), Modicon MC80 (part numbers BMKC80*, all versions), Modicon Momentum Ethernet CPU (part numbers 171CBU*, all versions), PLC Simulator for EcoStruxureª Control Expert, including all Unity Pro versions (former name of EcoStruxureª Control Expert, all versions), PLC Simulator for EcoStruxureª Process Expert including all HDCS versions (former name of EcoStruxureª Process Expert, all versions), Modicon Quantum CPU (part numbers 140CPU*, all versions), Modicon Premium CPU (part numbers TSXP5*, all versions). |
2021-09-02 |
not yet calculated |
CVE-2021-22792
MISC |
| modicon — multiple_devices |
A CWE-787: Out-of-bounds Write vulnerability that could cause a Denial of Service on the Modicon PLC controller / simulator when updating the controller application with a specially crafted project file exists in Modicon M580 CPU (part numbers BMEP* and BMEH*, all versions), Modicon M340 CPU (part numbers BMXP34*, all versions), Modicon MC80 (part numbers BMKC80*, all versions), Modicon Momentum Ethernet CPU (part numbers 171CBU*, all versions), PLC Simulator for EcoStruxureª Control Expert, including all Unity Pro versions (former name of EcoStruxureª Control Expert, all versions), PLC Simulator for EcoStruxureª Process Expert including all HDCS versions (former name of EcoStruxureª Process Expert, all versions), Modicon Quantum CPU (part numbers 140CPU*, all versions), Modicon Premium CPU (part numbers TSXP5*, all versions). |
2021-09-02 |
not yet calculated |
CVE-2021-22791
MISC |
modicon — multiple_devices
|
A CWE-125: Out-of-bounds Read vulnerability that could cause a Denial of Service on the Modicon PLC controller / simulator when updating the controller application with a specially crafted project file exists in Modicon M580 CPU (part numbers BMEP* and BMEH*, all versions), Modicon M340 CPU (part numbers BMXP34*, all versions), Modicon MC80 (part numbers BMKC80*, all versions), Modicon Momentum Ethernet CPU (part numbers 171CBU*, all versions), PLC Simulator for EcoStruxureª Control Expert, including all Unity Pro versions (former name of EcoStruxureª Control Expert, all versions), PLC Simulator for EcoStruxureª Process Expert including all HDCS versions (former name of EcoStruxureª Process Expert, all versions), Modicon Quantum CPU (part numbers 140CPU*, all versions), Modicon Premium CPU (part numbers TSXP5*, all versions). |
2021-09-02 |
not yet calculated |
CVE-2021-22790
MISC |
| mpath — mpath |
This affects the package mpath before 0.8.4. A type confusion vulnerability can lead to a bypass of CVE-2018-16490. In particular, the condition ignoreProperties.indexOf(parts[i]) !== -1 returns -1 if parts[i] is [‘__proto__’]. This is because the method that has been called if the input is an array is Array.prototype.indexOf() and not String.prototype.indexOf(). They behave differently depending on the type of the input. |
2021-09-01 |
not yet calculated |
CVE-2021-23438
MISC
MISC
MISC |
| mybb — mybb |
Cross Site Scripting (XSS) in MyBB v1.8.20 allows remote attackers to inject arbitrary web script or HTML via the “Title” field found in the “Add New Forum” page by doing an authenticated POST HTTP request to ‘/Upload/admin/index.php?module=forum-management&action=add’. |
2021-08-31 |
not yet calculated |
CVE-2020-19048
MISC |
mybb — mybb
|
Cross Site Scripting (XSS) in MyBB v1.8.20 allows remote attackers to inject arbitrary web script or HTML via the “Description” field found in the “Add New Forum” page by doing an authenticated POST HTTP request to ‘/Upload/admin/index.php?module=forum-management&action=add’. |
2021-08-31 |
not yet calculated |
CVE-2020-19049
MISC |
netiq — access_manager
|
This release addresses a potential information leakage vulnerability in NetIQ Access Manager versions prior to 5.0.1 |
2021-09-02 |
not yet calculated |
CVE-2021-22525
MISC |
| next.js — next.js |
Next.js is a React framework. Versions of Next.js between 10.0.0 and 11.0.0 contain a cross-site scripting vulnerability. In order for an instance to be affected by the vulnerability, the `next.config.js` file must have `images.domains` array assigned and the image host assigned in `images.domains` must allow user-provided SVG. If the `next.config.js` file has `images.loader` assigned to something other than default or the instance is deployed on Vercel, the instance is not affected by the vulnerability. The vulnerability is patched in Next.js version 11.1.1. |
2021-08-31 |
not yet calculated |
CVE-2021-39178
CONFIRM
MISC |
| npmcli/arborist — npmcli/arborist |
`@npmcli/arborist`, the library that calculates dependency trees and manages the node_modules folder hierarchy for the npm command line interface, aims to guarantee that package dependency contracts will be met, and the extraction of package contents will always be performed into the expected folder. This is accomplished by extracting package contents into a project’s `node_modules` folder. If the `node_modules` folder of the root project or any of its dependencies is somehow replaced with a symbolic link, it could allow Arborist to write package dependencies to any arbitrary location on the file system. Note that symbolic links contained within package artifact contents are filtered out, so another means of creating a `node_modules` symbolic link would have to be employed. 1. A `preinstall` script could replace `node_modules` with a symlink. (This is prevented by using `–ignore-scripts`.) 2. An attacker could supply the target with a git repository, instructing them to run `npm install –ignore-scripts` in the root. This may be successful, because `npm install –ignore-scripts` is typically not capable of making changes outside of the project directory, so it may be deemed safe. This is patched in @npmcli/arborist 2.8.2 which is included in npm v7.20.7 and above. For more information including workarounds please see the referenced GHSA-gmw6-94gg-2rc2. |
2021-08-31 |
not yet calculated |
CVE-2021-39135
CONFIRM
MISC |
| npmcli/arborist — npmcli/arborist |
`@npmcli/arborist`, the library that calculates dependency trees and manages the `node_modules` folder hierarchy for the npm command line interface, aims to guarantee that package dependency contracts will be met, and the extraction of package contents will always be performed into the expected folder. This is, in part, accomplished by resolving dependency specifiers defined in `package.json` manifests for dependencies with a specific name, and nesting folders to resolve conflicting dependencies. When multiple dependencies differ only in the case of their name, Arborist’s internal data structure saw them as separate items that could coexist within the same level in the `node_modules` hierarchy. However, on case-insensitive file systems (such as macOS and Windows), this is not the case. Combined with a symlink dependency such as `file:/some/path`, this allowed an attacker to create a situation in which arbitrary contents could be written to any location on the filesystem. For example, a package `pwn-a` could define a dependency in their `package.json` file such as `”foo”: “file:/some/path”`. Another package, `pwn-b` could define a dependency such as `FOO: “file:foo.tgz”`. On case-insensitive file systems, if `pwn-a` was installed, and then `pwn-b` was installed afterwards, the contents of `foo.tgz` would be written to `/some/path`, and any existing contents of `/some/path` would be removed. Anyone using npm v7.20.6 or earlier on a case-insensitive filesystem is potentially affected. This is patched in @npmcli/arborist 2.8.2 which is included in npm v7.20.7 and above. |
2021-08-31 |
not yet calculated |
CVE-2021-39134
CONFIRM
MISC |
| openemr — openemr |
OpenEMR 6.0.0 has a pnotes_print.php?noteid= Insecure Direct Object Reference vulnerability via which an attacker can read the messages of all users. |
2021-09-01 |
not yet calculated |
CVE-2021-40352
MISC
MISC
MISC |
| openolat — openolat |
OpenOLAT is a web-based learning management system (LMS). A path traversal vulnerability exists in versions prior to 15.3.18, 15.5.3, and 16.0.0. Using a specially prepared ZIP file, it is possible to overwrite any file that is writable by the application server user (e.g. the tomcat user). Depending on the configuration this can be limited to files of the OpenOlat user data directory, however, if not properly set up, the attack could also be used to overwrite application server config files, java code or even operating system files. The attack could be used to corrupt or modify any OpenOlat file such as course structures, config files or temporary test data. Those attack would require in-depth knowledge of the installation and thus more theoretical. If the app server configuration allows the execution of jsp files and the path to the context is known, it is also possible to execute java code. If the app server runs with the same user that is used to deploy the OpenOlat code or has write permissions on the OpenOlat code files and the path to the context is know, code injection is possible. The attack requires an OpenOlat user account to upload a ZIP file and trigger the unzip method. It can not be exploited by unregistered users. The problem is fixed in versions 15.3.18, 15.5.3 and 16.0.0. There are no known workarounds aside from upgrading. |
2021-08-31 |
not yet calculated |
CVE-2021-39180
MISC
MISC
MISC
CONFIRM
MISC |
| openolat — openolat |
OpenOlat is a web-based learning management system (LMS). Prior to version 15.3.18, 15.5.3, and 16.0.0, using a prepared import XML file (e.g. a course) any class on the Java classpath can be instantiated, including spring AOP bean factories. This can be used to execute code arbitrary code by the attacker. The attack requires an OpenOlat user account with the authoring role. It can not be exploited by unregistered users. The problem is fixed in versions 15.3.18, 15.5.3, and 16.0.0. There are no known workarounds aside from upgrading. |
2021-09-01 |
not yet calculated |
CVE-2021-39181
MISC
MISC
CONFIRM |
| opensis — opensis |
A SQL Injection vulnerability exists in openSIS 8.0 when MySQL (MariaDB) is being used as the application database. A malicious attacker can issue SQL commands to the MySQL (MariaDB) database through the NamesList.php str parameter. |
2021-09-01 |
not yet calculated |
CVE-2021-39378
MISC
MISC
MISC |
| opensis — opensis |
A SQL Injection vulnerability exists in openSIS 8.0 when MySQL (MariaDB) is being used as the application database. A malicious attacker can issue SQL commands to the MySQL (MariaDB) database through the ResetUserInfo.php password_stn_id parameter. |
2021-09-01 |
not yet calculated |
CVE-2021-39379
MISC
MISC
MISC |
| opensis — opensis |
A SQL Injection vulnerability exists in openSIS 8.0 when MySQL (MariaDB) is being used as the application database. A malicious attacker can issue SQL commands to the MySQL (MariaDB) database through the index.php username parameter. |
2021-09-01 |
not yet calculated |
CVE-2021-39377
MISC
MISC
MISC |
| openstack — neutron |
An issue was discovered in OpenStack Neutron before 16.4.1, 17.x before 17.2.1, and 18.x before 18.1.1. Authenticated attackers can reconfigure dnsmasq via a crafted extra_dhcp_opts value. |
2021-08-31 |
not yet calculated |
CVE-2021-40085
MISC
MISC
MLIST |
| outsystems — multiple_devices |
A stored XSS vulnerability was discovered in the ECT Provider in OutSystems before 2020-09-04, affecting generated applications. It could allow an unauthenticated remote attacker to craft and store malicious Feedback content into /ECT_Provider/, such that when the content is viewed (it can only be viewed by Administrators), attacker-controlled JavaScript will execute in the security context of an administrator’s browser. This is fixed in Outsystems 10.0.1005.2, Outsystems 11.9.0 Platform Server, and Outsystems 11.7.0 LifeTime Management Console. |
2021-08-31 |
not yet calculated |
CVE-2020-13639
MISC
MISC |
parse_server — parse_server
|
Parse Server is an open source backend that can be deployed to any infrastructure that can run Node.js. Prior to version 4.10.3, Parse Server crashes when if a query request contains an invalid value for the `explain` option. This is due to a bug in the MongoDB Node.js driver which throws an exception that Parse Server cannot catch. There is a patch for this issue in version 4.10.3. No workarounds aside from upgrading are known to exist. |
2021-09-02 |
not yet calculated |
CVE-2021-39187
MISC
MISC
MISC
CONFIRM |
| pepper — fuchs |
In PEPPERL+FUCHS WirelessHART-Gateway <= 3.0.8 serious issue exists, if the application is not externally accessible or uses IP-based access restrictions. Attackers can use DNS Rebinding to bypass any IP or firewall based access restrictions that may be in place, by proxying through their target’s browser. |
2021-08-31 |
not yet calculated |
CVE-2021-34561
CONFIRM |
| pepper — fuchs |
In PEPPERL+FUCHS WirelessHART-Gateway <= 3.0.7 the filename parameter is vulnerable to unauthenticated path traversal attacks, enabling read access to arbitrary files on the server. |
2021-08-31 |
not yet calculated |
CVE-2021-33555
CONFIRM |
| pepper — fuchs |
Any cookie-stealing vulnerabilities within the application or browser would enable an attacker to steal the user’s credentials to the PEPPERL+FUCHS WirelessHART-Gateway 3.0.9. |
2021-08-31 |
not yet calculated |
CVE-2021-34564
CONFIRM |
| pepper — fuchs |
In PEPPERL+FUCHS WirelessHART-Gateway 3.0.7 to 3.0.9 the SSH and telnet services are active with hard-coded credentials. |
2021-08-31 |
not yet calculated |
CVE-2021-34565
CONFIRM |
| pepper — fuchs |
In PEPPERL+FUCHS WirelessHART-Gateway <= 3.0.9 a form contains a password field with autocomplete enabled. The stored credentials can be captured by an attacker who gains control over the user’s computer. Therefore the user must have logged in at least once. |
2021-08-31 |
not yet calculated |
CVE-2021-34560
CONFIRM |
| pepper — fuchs |
In PEPPERL+FUCHS WirelessHART-Gateway <= 3.0.8 a vulnerability may allow remote attackers to rewrite links and URLs in cached pages to arbitrary strings. |
2021-08-31 |
not yet calculated |
CVE-2021-34559
CONFIRM |
| pepper — fuchs |
In PEPPERL+FUCHS WirelessHART-Gateway 3.0.8 and 3.0.9 the HttpOnly attribute is not set on a cookie. This allows the cookie’s value to be read or set by client-side JavaScript. |
2021-08-31 |
not yet calculated |
CVE-2021-34563
CONFIRM |
| pepper — fuchs |
In PEPPERL+FUCHS WirelessHART-Gateway 3.0.8 it is possible to inject arbitrary JavaScript into the application’s response. |
2021-08-31 |
not yet calculated |
CVE-2021-34562
CONFIRM |
| pillow — pillow |
The package pillow from 0 and before 8.3.2 are vulnerable to Regular Expression Denial of Service (ReDoS) via the getrgb function. |
2021-09-03 |
not yet calculated |
CVE-2021-23437
CONFIRM
CONFIRM
CONFIRM |
| pimcore — pimcore |
Pimcore is an open source data & experience management platform. Prior to version 10.1.2, an authenticated user could add XSS code as a value of custom metadata on assets. There is a patch for this issue in Pimcore version 10.1.2. As a workaround, users may apply the patch manually. |
2021-09-01 |
not yet calculated |
CVE-2021-39170
MISC
MISC
CONFIRM
MISC |
| pimcore — pimcore |
Pimcore is an open source data & experience management platform. Prior to version 10.1.2, text-values were not properly escaped before printed in the version preview. This allowed XSS by authenticated users with access to the resources. This issue is patched in Pimcore version 10.1.2. |
2021-09-01 |
not yet calculated |
CVE-2021-39166
CONFIRM
MISC |
| proto — proto |
This affects all versions of package Proto. It is possible to inject pollute the object property of an application using Proto by leveraging the merge function. |
2021-09-01 |
not yet calculated |
CVE-2021-23426
MISC
MISC |
puppet — enterprise
|
Puppet Enterprise presented a security risk by not sanitizing user input when doing a CSV export. |
2021-08-30 |
not yet calculated |
CVE-2021-27020
MISC |
puppet — puppetdb
|
PuppetDB logging included potentially sensitive system information. |
2021-08-30 |
not yet calculated |
CVE-2021-27019
MISC |
puppet — remidate
|
The mechanism which performs certificate validation was discovered to have a flaw that resulted in certificates signed by an internal certificate authority to not be properly validated. This issue only affects clients that are configured to utilize Tenable.sc as the vulnerability data source. |
2021-08-30 |
not yet calculated |
CVE-2021-27018
MISC |
| rocket.chat — rocket.chat |
Rocket.Chat is an open-source fully customizable communications platform developed in JavaScript. In Rocket.Chat before versions 3.11.3, 3.12.2, and 3.13 an issue with certain regular expressions could lead potentially to Denial of Service. This was fixed in versions 3.11.3, 3.12.2, and 3.13. |
2021-08-30 |
not yet calculated |
CVE-2021-32832
MISC
CONFIRM
MISC
MISC |
rundeck — rundeck
|
Rundeck is an open source automation service with a web console, command line tools and a WebAPI. Prior to version 3.3.14 and version 3.4.3, a user with `admin` access to the `system` resource type is potentially vulnerable to a CSRF attack that could cause the server to run untrusted code on all Rundeck editions. Patches are available in Rundeck versions 3.4.3 and 3.3.14. |
2021-08-30 |
not yet calculated |
CVE-2021-39133
CONFIRM
MISC |
rundeck — rundeck
|
Rundeck is an open source automation service with a web console, command line tools and a WebAPI. Prior to version 3.3.14 and version 3.4.3, an authorized user can upload a zip-format plugin with a crafted plugin.yaml, or a crafted aclpolicy yaml file, or upload an untrusted project archive with a crafted aclpolicy yaml file, that can cause the server to run untrusted code on Rundeck Community or Enterprise Edition. An authenticated user can make a POST request, that can cause the server to run untrusted code on Rundeck Enterprise Edition. The zip-format plugin issues requires authentication and authorization to these access levels, and affects all Rundeck editions:`admin` level access to the `system` resource type. The ACL Policy yaml file upload issues requires authentication and authorization to these access levels, and affects all Rundeck editions: `create` `update` or `admin` level access to a `project_acl` resource, and/or`create` `update` or `admin` level access to the `system_acl` resource. The unauthorized POST request requires authentication, but no specific authorization, and affects Rundeck Enterprise only. Patches are available in versions 3.4.3, 3.3.14 |
2021-08-30 |
not yet calculated |
CVE-2021-39132
CONFIRM
MISC |
| s-cms — s-cms |
Cross Site Scripting (XSS) in S-CMS v1.0 allows remote attackers to execute arbitrary code via the component ‘/admin/tpl.php?page=’. |
2021-08-31 |
not yet calculated |
CVE-2020-19046
MISC |
| s-cms — s-cms |
A SQL injection vulnerability in the 4.edu.phpconnfunction.php component of S-CMS v1.0 allows attackers to access sensitive database information. |
2021-09-01 |
not yet calculated |
CVE-2020-20340
MISC |
samsung — drive_manager
|
Samsung Drive Manager 2.0.104 on Samsung H3 devices allows attackers to bypass intended access controls on disk management. WideCharToMultiByte, WideCharStr, and MultiByteStr can contribute to password exposure. |
2021-09-01 |
not yet calculated |
CVE-2021-39373
MISC |
sernet — verinice
|
In the server in SerNet verinice before 1.22.2, insecure Java deserialization allows remote authenticated attackers to execute arbitrary code. |
2021-08-31 |
not yet calculated |
CVE-2021-36981
MISC
MISC |
| solarwinds — orion_platform |
Deserialization of Untrusted Data in the Web Console Chart Endpoint can lead to remote code execution. An unauthorized attacker who has network access to the Orion Patch Manager Web Console could potentially exploit this and compromise the server |
2021-09-01 |
not yet calculated |
CVE-2021-35218
MISC
MISC |
| solarwinds — orion_platform |
Insecure deserialization leading to Remote Code Execution was detected in the Orion Platform version 2020.2.5. Authentication is required to exploit this vulnerability. |
2021-09-01 |
not yet calculated |
CVE-2021-35215
MISC
MISC
MISC |
| solarwinds — orion_platform |
An Improper Access Control Privilege Escalation Vulnerability was discovered in the User Setting of Orion Platform version 2020.2.5. It allows a guest user to elevate privileges to the Administrator using this vulnerability. Authentication is required to exploit the vulnerability. |
2021-08-31 |
not yet calculated |
CVE-2021-35213
MISC
MISC
MISC |
| solarwinds — orion_platform |
This vulnerability allows attackers to impersonate users and perform arbitrary actions leading to a Remote Code Execution (RCE) from the Alerts Settings page. |
2021-08-31 |
not yet calculated |
CVE-2021-35222
MISC
MISC
MISC
MISC |
solarwinds — orion_platform
|
Command Injection vulnerability in EmailWebPage API which can lead to a Remote Code Execution (RCE) from the Alerts Settings page. |
2021-08-31 |
not yet calculated |
CVE-2021-35220
MISC
MISC
MISC
MISC |
solarwinds — orion_platform
|
An SQL injection Privilege Escalation Vulnerability was discovered in the Orion Platform reported by the ZDI Team. A blind Boolean SQL injection which could lead to full read/write over the Orion database content including the Orion certificate for any authenticated user. |
2021-08-31 |
not yet calculated |
CVE-2021-35212
MISC
MISC
MISC |
solarwinds — orion_platform
|
Insecure Deserialization of untrusted data remote code execution vulnerability was discovered in Patch Manager Orion Platform Integration module. An Authenticated Attacker with network access via HTTP can compromise this vulnerability can result in Remote Code Execution. |
2021-09-01 |
not yet calculated |
CVE-2021-35216
MISC
MISC |
solarwinds — orion_platform
|
ExportToPdfCmd Arbitrary File Read Information Disclosure Vulnerability using ImportAlert function within the Alerts Settings page. |
2021-08-31 |
not yet calculated |
CVE-2021-35219
MISC
MISC
MISC
MISC |
| solarwinds — orion_platform |
Improper Access Control Tampering Vulnerability using ImportAlert function which can lead to a Remote Code Execution (RCE) from the Alerts Settings page. |
2021-08-31 |
not yet calculated |
CVE-2021-35221
MISC
MISC
MISC
MISC |
| solarwinds — orion_platform |
The Serv-U File Server allows for events such as user login failures to be audited by executing a command. This command can be supplied with parameters that can take the form of ‘user string variables,” allowing remote code execution. |
2021-08-31 |
not yet calculated |
CVE-2021-35223
MISC
MISC
MISC |
| solarwinds — orion_platform |
A security researcher stored XSS via a Help Server setting. This affects customers using Internet Explorer, because they do not support ‘rel=noopener’. |
2021-08-31 |
not yet calculated |
CVE-2021-35240
MISC
MISC
MISC
MISC |
solarwinds — orion_platform
|
A security researcher found a user with Orion map manage rights could store XSS through via text box hyperlink. |
2021-08-31 |
not yet calculated |
CVE-2021-35239
MISC
MISC
MISC
MISC |
| solarwinds — orion_platform |
User with Orion Platform Admin Rights could store XSS through URL POST parameter in CreateExternalWebsite website. |
2021-09-01 |
not yet calculated |
CVE-2021-35238
MISC
MISC
MISC |
| tar — tar |
The npm package “tar” (aka node-tar) before versions 4.4.18, 5.0.10, and 6.1.9 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be outside of the extraction target directory is not extracted. This is, in part, accomplished by sanitizing absolute paths of entries within the archive, skipping archive entries that contain `..` path portions, and resolving the sanitized paths against the extraction target directory. This logic was insufficient on Windows systems when extracting tar files that contained a path that was not an absolute path, but specified a drive letter different from the extraction target, such as `C:somepath`. If the drive letter does not match the extraction target, for example `D:extractiondir`, then the result of `path.resolve(extractionDirectory, entryPath)` would resolve against the current working directory on the `C:` drive, rather than the extraction target directory. Additionally, a `..` portion of the path could occur immediately after the drive letter, such as `C:../foo`, and was not properly sanitized by the logic that checked for `..` within the normalized and split portions of the path. This only affects users of `node-tar` on Windows systems. These issues were addressed in releases 4.4.18, 5.0.10 and 6.1.9. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. There is no reasonable way to work around this issue without performing the same path normalization procedures that node-tar now does. Users are encouraged to upgrade to the latest patched versions of node-tar, rather than attempt to sanitize paths themselves. |
2021-08-31 |
not yet calculated |
CVE-2021-37713
CONFIRM
MISC |
| tar — tar |
The npm package “tar” (aka node-tar) before versions 4.4.18, 5.0.10, and 6.1.9 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary stat calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with names containing unicode values that normalized to the same value. Additionally, on Windows systems, long path portions would resolve to the same file system entities as their 8.3 “short path” counterparts. A specially crafted tar archive could thus include a directory with one form of the path, followed by a symbolic link with a different string that resolves to the same file system entity, followed by a file using the first form. By first creating a directory, and then replacing that directory with a symlink that had a different apparent name that resolved to the same entry in the filesystem, it was thus possible to bypass node-tar symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. These issues were addressed in releases 4.4.18, 5.0.10 and 6.1.9. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. If this is not possible, a workaround is available in the referenced GHSA-qq89-hq3f-393p. |
2021-08-31 |
not yet calculated |
CVE-2021-37712
CONFIRM
MISC |
| tar — tar |
The npm package “tar” (aka node-tar) before versions 4.4.16, 5.0.8, and 6.1.7 has an arbitrary file creation/overwrite and arbitrary code execution vulnerability. node-tar aims to guarantee that any file whose location would be modified by a symbolic link is not extracted. This is, in part, achieved by ensuring that extracted directories are not symlinks. Additionally, in order to prevent unnecessary stat calls to determine whether a given path is a directory, paths are cached when directories are created. This logic was insufficient when extracting tar files that contained both a directory and a symlink with the same name as the directory, where the symlink and directory names in the archive entry used backslashes as a path separator on posix systems. The cache checking logic used both “ and `/` characters as path separators, however “ is a valid filename character on posix systems. By first creating a directory, and then replacing that directory with a symlink, it was thus possible to bypass node-tar symlink checks on directories, essentially allowing an untrusted tar file to symlink into an arbitrary location and subsequently extracting arbitrary files into that location, thus allowing arbitrary file creation and overwrite. Additionally, a similar confusion could arise on case-insensitive filesystems. If a tar archive contained a directory at `FOO`, followed by a symbolic link named `foo`, then on case-insensitive file systems, the creation of the symbolic link would remove the directory from the filesystem, but _not_ from the internal directory cache, as it would not be treated as a cache hit. A subsequent file entry within the `FOO` directory would then be placed in the target of the symbolic link, thinking that the directory had already been created. These issues were addressed in releases 4.4.16, 5.0.8 and 6.1.7. The v3 branch of node-tar has been deprecated and did not receive patches for these issues. If you are still using a v3 release we recommend you update to a more recent version of node-tar. If this is not possible, a workaround is available in the referenced GHSA-9r2w-394v-53qc. |
2021-08-31 |
not yet calculated |
CVE-2021-37701
CONFIRM
MISC |
tizen — rt_rtos
|
Tizen RT RTOS version 3.0.GBB is vulnerable to integer wrap-around in functions_calloc and mm_zalloc. This improper memory assignment can lead to arbitrary memory allocation, resulting in unexpected behavior such as a crash |
2021-08-31 |
not yet calculated |
CVE-2021-22684
MISC |
unifi — protect
|
A vulnerability found in UniFi Protect application V1.18.1 and earlier allows a malicious actor with a view-only role and network access to gain the same privileges as the owner of the UniFi Protect application. This vulnerability is fixed in UniFi Protect application V1.19.0 and later. |
2021-08-31 |
not yet calculated |
CVE-2021-22944
MISC |
unifi — protect
|
A vulnerability found in UniFi Protect application V1.18.1 and earlier permits a malicious actor who has already gained access to a network to subsequently control the Protect camera(s) assigned to said network. This vulnerability is fixed in UniFi Protect application V1.19.0 and later. |
2021-08-31 |
not yet calculated |
CVE-2021-22943
MISC |
| vijeo_designer — harmony |
A CWE-22: Improper Limitation of a Pathname to a Restricted Directory vulnerability exists in Harmony/HMI Products Configured by Vijeo Designer (all versions prior to V6.2 SP11 ), Vijeo Designer Basic (all versions prior to V1.2), or EcoStruxure Machine Expert (all versions prior to V2.0) that could cause a Denial of Service or unauthorized access to system information when connecting to the Harmony HMI over FTP. |
2021-09-02 |
not yet calculated |
CVE-2021-22704
MISC |
| vmware — workspace |
VMware Workspace ONE UEM REST API contains a denial of service vulnerability. A malicious actor with access to /API/system/admins/session could cause an API denial of service due to improper rate limiting. |
2021-08-31 |
not yet calculated |
CVE-2021-22029
MISC |
| vmware — workspace_one_access_and_identity_manager |
VMware Workspace ONE Access and Identity Manager, allow the /cfg web app and diagnostic endpoints, on port 8443, to be accessed via port 443 using a custom host header. A malicious actor with network access to port 443 could tamper with host headers to facilitate access to the /cfg web app, in addition a malicious actor could access /cfg diagnostic endpoints without authentication. |
2021-08-31 |
not yet calculated |
CVE-2021-22002
MISC |
vmware — workspace_one_access_and_identity_manager
|
VMware Workspace ONE Access and Identity Manager, unintentionally provide a login interface on port 7443. A malicious actor with network access to port 7443 may attempt user enumeration or brute force the login endpoint, which may or may not be practical based on lockout policy configuration and password complexity for the target account. |
2021-08-31 |
not yet calculated |
CVE-2021-22003
MISC |
| wago — wago |
This vulnerability allows an attacker who has access to the WBM to read and write settings-parameters of the device by sending specifically constructed requests without authentication on multiple WAGO PLCs in firmware versions up to FW07. |
2021-08-31 |
not yet calculated |
CVE-2021-34578
CONFIRM |
wago — wago
|
Missing Release of Resource after Effective Lifetime vulnerability in OpenSSL implementation of WAGO 750-831/xxx-xxx, 750-880/xxx-xxx, 750-881, 750-889 in versions FW4 up to FW15 allows an unauthenticated attacker to cause DoS on the device. |
2021-08-31 |
not yet calculated |
CVE-2021-34581
CONFIRM |
| wordpress — wordpress |
The Gutenberg Template Library & Redux Framework plugin <= 4.2.11 for WordPress registered several AJAX actions available to unauthenticated users in the `includes` function in `redux-core/class-redux-core.php` that were unique to a given site but deterministic and predictable given that they were based on an md5 hash of the site URL with a known salt value of ‘-redux’ and an md5 hash of the previous hash with a known salt value of ‘-support’. These AJAX actions could be used to retrieve a list of active plugins and their versions, the site’s PHP version, and an unsalted md5 hash of site’s `AUTH_KEY` concatenated with the `SECURE_AUTH_KEY`. |
2021-09-02 |
not yet calculated |
CVE-2021-38314
MISC |
| wordpress — wordpress |
The Gutenberg Template Library & Redux Framework plugin <= 4.2.11 for WordPress used an incorrect authorization check in the REST API endpoints registered under the “redux/v1/templates/” REST Route in “redux-templates/classes/class-api.php”. The `permissions_callback` used in this file only checked for the `edit_posts` capability which is granted to lower-privileged users such as contributors, allowing such users to install arbitrary plugins from the WordPress repository and edit arbitrary posts. |
2021-09-02 |
not yet calculated |
CVE-2021-38312
MISC |
| wordpress — wordpress |
The ShareThis Dashboard for Google Analytics WordPress plugin before 2.5.2 does not sanitise or escape the ‘ga_action’ parameter in the stats view before outputting it back in an attribute when the plugin is connected to a Google Analytics account, leading to a reflected Cross-Site Scripting issue which will be executed in the context of a logged in administrator |
2021-08-30 |
not yet calculated |
CVE-2021-24438
MISC |
wordpress — wordpress
|
The Blue Admin WordPress plugin through 21.06.01 does not sanitise or escape its “Logo Title” setting before outputting in a page, leading to a Stored Cross-Site Scripting issue. Furthermore, the plugin does not have CSRF check in place when saving its settings, allowing the issue to be exploited via a CSRF attack. |
2021-08-30 |
not yet calculated |
CVE-2021-24581
MISC |
| wordpress — wordpress |
Versions up to, and including, 5.4.3, of the Booster for WooCommerce WordPress plugin are vulnerable to authentication bypass via the process_email_verification function due to a random token generation weakness in the reset_and_mail_activation_link function found in the ~/includes/class-wcj-emails-verification.php file. This allows attackers to impersonate users and trigger an email address verification for arbitrary accounts, including administrative accounts, and automatically be logged in as that user, including any site administrators. This requires the Email Verification module to be active in the plugin and the Login User After Successful Verification setting to be enabled, which it is by default. |
2021-08-30 |
not yet calculated |
CVE-2021-34646
MISC
MISC |
wordpress — wordpress
|
The underConstruction plugin <= 1.18 for WordPress echoes out the raw value of `$GLOBALS[‘PHP_SELF’]` in the ucOptions.php file. On certain configurations including Apache+modPHP, this makes it possible to use it to perform a reflected Cross-Site Scripting attack by injecting malicious code in the request path. |
2021-09-01 |
not yet calculated |
CVE-2021-39320
MISC
MISC |
wordpress — wordpress
|
The Zoomsounds plugin <= 6.45 for WordPress allows arbitrary files, including sensitive configuration files such as wp-config.php, to be downloaded via the `dzsap_download` action using directory traversal in the `link` parameter. |
2021-08-31 |
not yet calculated |
CVE-2021-39316
MISC |
| wordpress — wordpress |
The Easy Social Icons plugin <= 3.0.8 for WordPress echoes out the raw value of `$_SERVER[‘PHP_SELF’]` in its main file. On certain configurations including Apache+modPHP this makes it possible to use it to perform a reflected Cross-Site Scripting attack by injecting malicious code in the request path. |
2021-09-02 |
not yet calculated |
CVE-2021-39322
MISC
MISC |
| wtcms — wtcms |
WTCMS 1.0 contains a reflective cross-site scripting (XSS) vulnerability in the page management background which allows attackers to obtain cookies via a crafted payload entered into the search box. |
2021-09-01 |
not yet calculated |
CVE-2020-20345
MISC
MISC
MISC |
| wtcms — wtcms |
WTCMS 1.0 contains a stored cross-site scripting (XSS) vulnerability in the source field under the article management module. |
2021-09-01 |
not yet calculated |
CVE-2020-20347
MISC |
| wtcms — wtcms |
WTCMS 1.0 contains a stored cross-site scripting (XSS) vulnerability in the link address field under the background links module. |
2021-09-01 |
not yet calculated |
CVE-2020-20349
MISC |
| wtcms — wtcms |
WTCMS 1.0 contains a reflective cross-site scripting (XSS) vulnerability in the keyword search function under the background articles module. |
2021-09-01 |
not yet calculated |
CVE-2020-20344
MISC |
| wtcms — wtcms |
WTCMS 1.0 contains a stored cross-site scripting (XSS) vulnerability in the link field under the background menu management module. |
2021-09-01 |
not yet calculated |
CVE-2020-20348
MISC |
| wtcms — wtcms |
WTCMS 1.0 contains a cross-site request forgery (CSRF) vulnerability in the index.php?g=admin&m=nav&a=add_post component that allows attackers to arbitrarily add articles in the administrator background. |
2021-09-01 |
not yet calculated |
CVE-2020-20343
MISC |
| xmp — toolkit_sdk |
XMP Toolkit version 2020.1 (and earlier) is affected by a Buffer Underflow vulnerability which could result in arbitrary code execution in the context of the current user. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-01 |
not yet calculated |
CVE-2021-36064
MISC |
| xmp — toolkit_sdk |
XMP Toolkit SDK version 2020.1 (and earlier) is affected by a buffer overflow vulnerability potentially resulting in arbitrary code execution in the context of the current user. Exploitation requires user interaction in that a victim must open a crafted file. |
2021-09-01 |
not yet calculated |
CVE-2021-36050
MISC |
| xmp — toolkit_sdk |
XMP Toolkit SDK versions 2020.1 (and earlier) are affected by a use-after-free vulnerability that could result in arbitrary code execution in the context of the current user. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-01 |
not yet calculated |
CVE-2021-36055
MISC |
| xmp — toolkit_sdk |
XMP Toolkit version 2020.1 (and earlier) is affected by a memory corruption vulnerability, potentially resulting in arbitrary code execution in the context of the current user. User interaction is required to exploit this vulnerability. |
2021-09-01 |
not yet calculated |
CVE-2021-36052
MISC |
| xmp — toolkit_sdk |
XMP Toolkit SDK versions 2020.1 (and earlier) are affected by an out-of-bounds read vulnerability that could lead to disclosure of arbitrary memory. An attacker could leverage this vulnerability to bypass mitigations such as ASLR. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-01 |
not yet calculated |
CVE-2021-36053
MISC |
| xmp — toolkit_sdk |
XMP Toolkit SDK version 2020.1 (and earlier) is affected by a buffer overflow vulnerability potentially resulting in local application denial of service in the context of the current user. Exploitation requires user interaction in that a victim must open a crafted file. |
2021-09-01 |
not yet calculated |
CVE-2021-36054
MISC |
| xmp — toolkit_sdk |
XMP Toolkit SDK version 2020.1 (and earlier) is affected by a write-what-where condition vulnerability caused during the application’s memory allocation process. This may cause the memory management functions to become mismatched resulting in local application denial of service in the context of the current user. |
2021-09-01 |
not yet calculated |
CVE-2021-36057
MISC |
xmp — toolkit_sdk
|
XMP Toolkit SDK versions 2020.1 (and earlier) are affected by an out-of-bounds read vulnerability that could lead to disclosure of arbitrary memory. An attacker could leverage this vulnerability to bypass mitigations such as ASLR. Exploitation of this issue requires user interaction in that a victim must open a malicious file. |
2021-09-01 |
not yet calculated |
CVE-2021-36045
MISC |
| xmp — toolkit_sdk |
XMP Toolkit SDK version 2020.1 (and earlier) is affected by an Improper Input Validation vulnerability potentially resulting in arbitrary code execution in the context of the current user. Exploitation requires user interaction in that a victim must open a crafted file. |
2021-09-01 |
not yet calculated |
CVE-2021-36047
MISC |
| xmp — toolkit_sdk |
XMP Toolkit SDK version 2020.1 (and earlier) is affected by a stack-based buffer overflow vulnerability potentially resulting in arbitrary code execution in the context of the current user. Exploitation requires user interaction in that a victim must open a crafted file. |
2021-09-01 |
not yet calculated |
CVE-2021-39847
MISC |
| xmp — toolkit_sdk |
XMP Toolkit SDK version 2020.1 (and earlier) is affected by an Improper Input Validation vulnerability potentially resulting in arbitrary code execution in the context of the current user. Exploitation requires user interaction in that a victim must open a crafted file. |
2021-09-01 |
not yet calculated |
CVE-2021-36048
MISC |
| xmp — toolkit_sdk |
XMP Toolkit version 2020.1 (and earlier) is affected by a memory corruption vulnerability, potentially resulting in arbitrary code execution in the context of the current user. User interaction is required to exploit this vulnerability. |
2021-09-01 |
not yet calculated |
CVE-2021-36046
MISC |
xmp — toolkit_sdk
|
XMP Toolkit SDK version 2020.1 (and earlier) is affected by a buffer overflow vulnerability potentially resulting in arbitrary code execution in the context of the current user. Exploitation requires user interaction in that a victim must open a crafted file. |
2021-09-01 |
not yet calculated |
CVE-2021-36056
MISC |
| xmp — toolkit_sdk |
XMP Toolkit SDK version 2020.1 (and earlier) is affected by an Integer Overflow vulnerability potentially resulting in application-level denial of service in the context of the current user. Exploitation requires user interaction in that a victim must open a crafted file. |
2021-09-01 |
not yet calculated |
CVE-2021-36058
MISC |
| yzcms — yzcms |
YzmCMS v5.5 contains a server-side request forgery (SSRF) in the grab_image() function. |
2021-09-01 |
not yet calculated |
CVE-2020-20341
MISC |
zoho — manageengine_servicedesk_plus
|
Zoho ManageEngine ServiceDesk Plus before 11302 is vulnerable to authentication bypass that allows a few REST-API URLs without authentication. |
2021-09-01 |
not yet calculated |
CVE-2021-37415
MISC
CONFIRM |
| zte — zte |
A conference management system of ZTE is impacted by a command execution vulnerability. Since the soapmonitor’s java object service is enabled by default, the attacker could exploit this vulnerability to execute arbitrary commands by sending a deserialized payload to port 5001. |
2021-08-30 |
not yet calculated |
CVE-2021-21741
MISC |



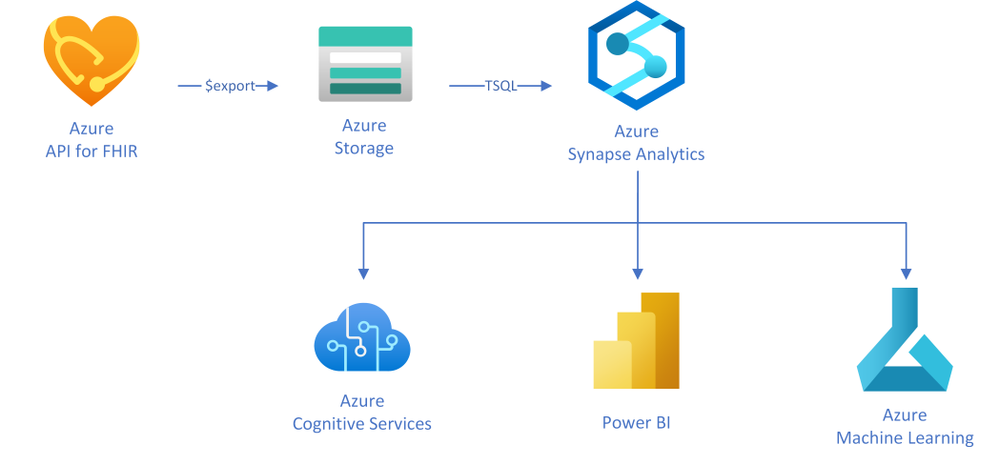

Recent Comments