Microsoft HoloLens 2 and mixed reality bridge physical reality and digital experiences
This article is contributed. See the original author and article here.
Across industries, companies are finding practical ways to bridge physical reality and digital experiences using hands-free headsets and augmented reality solutions to inform decisions and action on insights produced by smart, connected solutions.
Mixed realitya set of technologies that superimposes digital data and images in the physical worldbrings new opportunities that have become instrumental to how we tap into unique real-world, human capabilities. This technology is becoming more widely used across organizations today and has proven to be transformative to task performance, learning and retention, and collaboration. In fact, the augmented and virtual reality market is expected to reach $372.1 billion by the end of 2022, and swell to $542.8 billion by the end of 2025 according to new data from the IDC.1
Microsoft’s comprehensive ecosystem of mixed reality solutions such as Microsoft HoloLens 2, Microsoft Dynamics 365 Remote Assist, and Microsoft Dynamics 365 Guides are helping organizations optimize operations, reduce downtime, accelerate onboarding and upskilling, and decrease costs with more precise, efficient hands-free work.
Microsoft HoloLens 2 and mixed reality solutions are driving material ROI across industries
Based on the Microsoft-commissioned Forrester Total Economic Impact (TEI) report, Microsoft HoloLens 2 is delivering 177 percent return on investment (ROI) and a net present value (NPV) of $7.6 million over three years with a payback of 13 months.2 Customers across leading industries are realizing significant value from deploying mixed reality solutions in their most common, critical work scenarios.
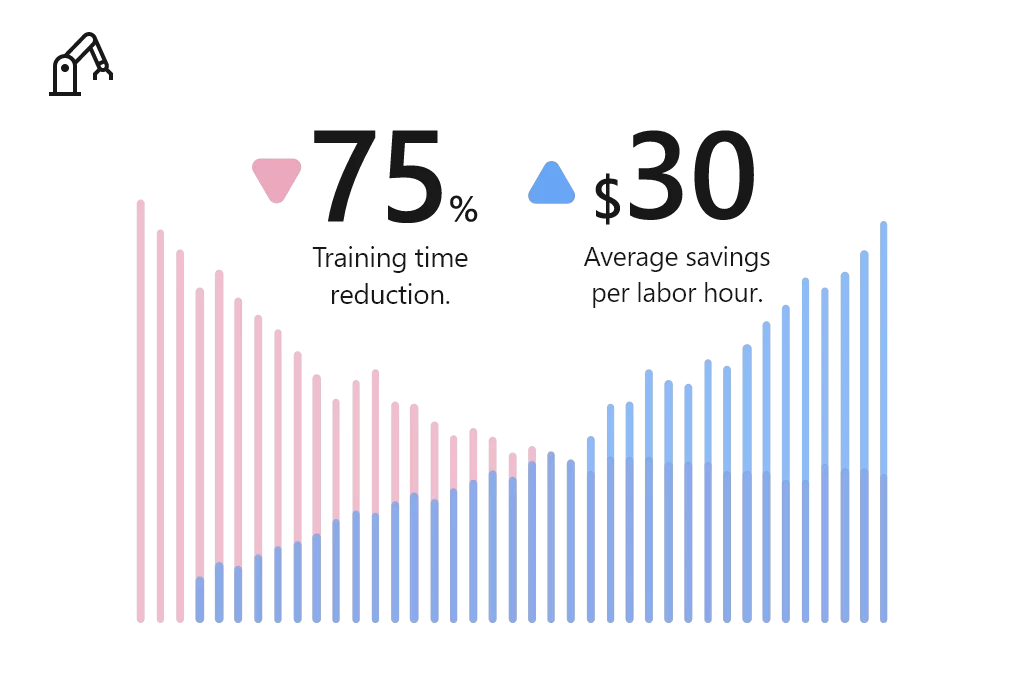
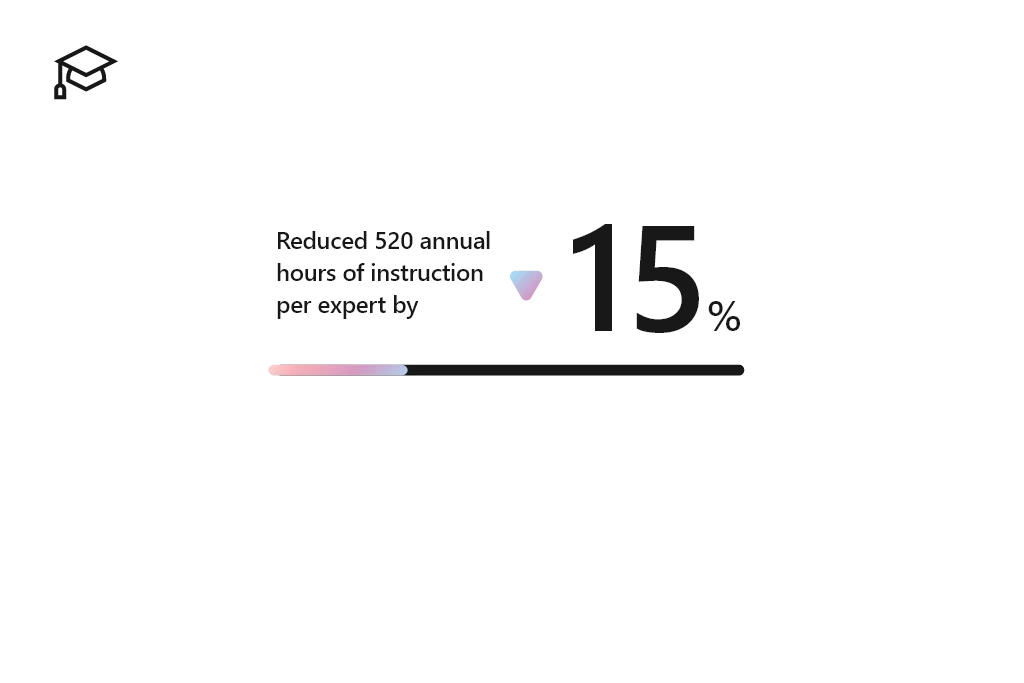
Manufacturing
Manufacturing companies deploying Microsoft HoloLens 2 and mixed reality applications to train their workforces, accelerate employee proficiency, and build more agile factories. Using Microsoft mixed reality, Manufacturers reduced training time by 75 percent, at an average savings of $30 per labor hour.2
Common scenarios in which manufacturers benefit from mixed reality on Microsoft HoloLens 2:
- Guided assembly and training: Empower employees to learn new skills and complex assembly tasks with holographic step-by-step instructions, no instructor necessary.
- Remote inspection and audits: Enable remote employees to solve business problems in real time, using 3D annotations to access, share, and bring critical information into view.
- Connected field service: Connect field technicians with remote experts to collaborate seamlessly, heads-up and hands-free with content capture abilities, interactive annotations, and contextual data overlays.
“When you describe a problem, imagine that we are speaking different languages. When you explain it, someone on the other side may not understand precisely what’s happening, but when you show it in real time with the HoloLens, people understand.”Eaton Vehicle Group. Read more about the Eaton Vehicle Group customer story.
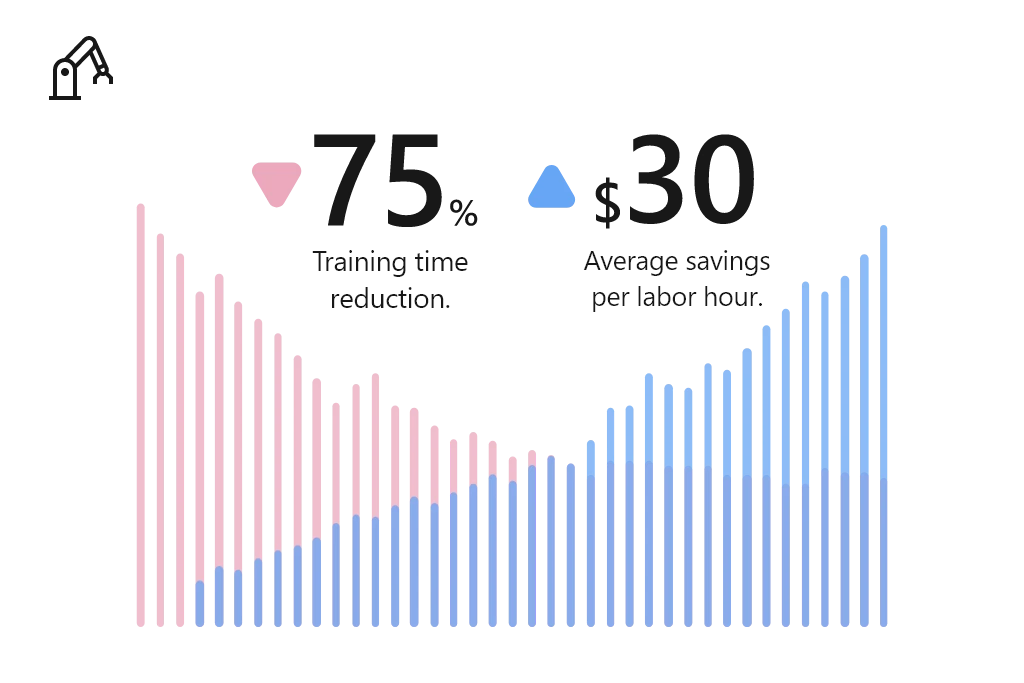
Education
Educators are turning to Microsoft HoloLens 2 and mixed reality applications to help students embrace a new way of learning. For example, education institutions reduced 520 annual hours of instruction per expert by 15 percent.2
Common scenarios in which educators benefit from mixed reality on Microsoft HoloLens 2:
- Augmented teaching: Captivate students and bring education to life with impressionable, high-impact 3D visualization models that enable virtual collaboration and instruction.
- Experiential learning: Enable educators to build an experience-based lesson plan, integrating textbook concepts into physical environments to create a simple “learn by doing” approach for studentshands-on and unmediated.
- Scaled learning and research: Develop a scalable research collaboration model that improves efficiency of research, lab work, and medical training.
“We did a trial back with our medical students. The students that had been in the HoloLens lab scored 50 percent better compared to the rest of the med school class.”Case Western. Read more about the Case Western customer story.
Healthcare
Mixed reality is empowering providers, payors, and health science experts to reimagine healthcare by accelerating diagnoses, reducing time-to-care, and enabling personalization. Using Microsoft mixed reality, healthcare providers reduced average consumables by 80%, saving $4,000 per trainee.2

Common scenarios in which healthcare providers benefit from mixed reality on Microsoft HoloLens 2:
- Holographic patient consultation: Enable healthcare providers to project 3D holographic visualizations of patients’ internal systems that provide procedural understandingbuilding confidence in upcoming procedures and/or treatments.
- Remote expert consultation: Support remote consultation and enable medical staff to consult colleagues with heads-up and hands-free through an interactive collaborative experience from anywhere in the world.
- Training simulations: Train medical staff with holographic step-by-step guidance without subject matter experts being physically present.
“Using Dynamics 365 Remote Assist, doctors wearing HoloLens, can hold “hands-free” and “heads-up” Teams video calls with colleagues and experts anywhere in the world. They can receive advice, interacting with the caller and the patient at the same time, while medical notes and X-rays can also be placed alongside the call in the wearer’s field of view.”Imperial College Healthcare NHS Trust. Read more about the Imperial College Healthcare NHS Trust customer story.
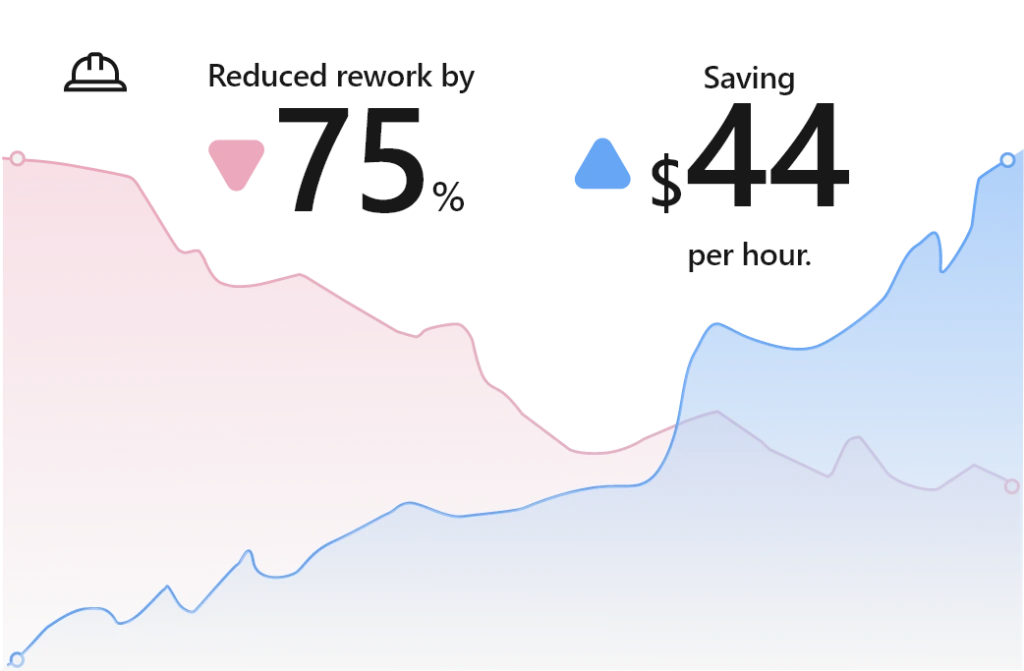
Architecture, engineering, and construction
With Mixed Reality, architecture, engineering, and construction (AEC) firms are empowered to overcome design, modeling, collaboration, and building site challenges to enhance project quality, decision-making, improve productivity. For example, AEC firms have reduced rework by 75 percent, saving $44 per hour.2
Common scenarios in which AEC organizations benefit from mixed reality on Microsoft HoloLens 2:
- Clash detection: Enable onsite workers to preemptively identify issues, detect clashes, and gain buy-in of onsite workers and key stakeholders with overlay designs on physical locations. This mitigates late-stage design changes that could result in rework, budget overrun, and project delays.
- 3D plan and model demonstrations: Empower project leaders, designers, and engineers and improve customer service and sales with 3D demonstration and immersive visualizations.
- Self-guided learning: Equip onsite workers to view task instructions, essential data, and model visualizations while in the flow of work, increasing speed, quality, and safety.
“We use Dynamics 365 Remote Assist on HoloLens 2 to work more effectively and share expertise at critical milestones. This not only saves us money but also helps us construct datacenters for our customers more quickly.”Microsoft. Read the full customer story.
The Forrester TEI study validates how mixed reality solutions on Microsoft HoloLens 2 are empowering enterprises across industries to achieve more. We believe these technologies have offered not only innovative results, but long-term and sustainable solutions for training, remote collaboration, inspections and audits, field service, and more.
Next steps
We look forward to continuing this blog series with a deep dive spotlight on each of these leading industries. In the meantime, learn more about mixed reality applications on Microsoft HoloLens 2 and get started today:
- Learn more about more about Microsoft HoloLens 2 and mixed reality capabilities.
- Learn more about business benefits and cost savings of mixed reality solutions, read the Total Economic Impact Of Mixed Reality Using Microsoft HoloLens 2 report.
- Request a Dynamics 365 Mixed Reality demo on Microsoft HoloLens 2. Book an appointment with our Microsoft Stores team today. Select ‘Other’ under Choose topic and reference HoloLens 2 demo in “What can we help with”.
Sources:
- Worldwide Quarterly Wearable Device Tracker, IDC, 2022
- The Total Economic Impact Of Mixed Reality Using Microsoft HoloLens 2 Report, Forrester, 2022
The post Microsoft HoloLens 2 and mixed reality bridge physical reality and digital experiences appeared first on Microsoft Dynamics 365 Blog.
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.




Recent Comments