by Scott Muniz | Aug 4, 2022 | Security, Technology
This article is contributed. See the original author and article here.
F5 has released security updates to address vulnerabilities in multiple products. A privileged attacker could exploit some of these vulnerabilities to take control of an affected system.
CISA encourages users and administrators to review the F5 security advisories and apply the necessary updates.
by Scott Muniz | Aug 4, 2022 | Security
This article was originally posted by the FTC. See the original article here.
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.
by Contributed | Aug 3, 2022 | Technology
This article is contributed. See the original author and article here.
When performing an offensive security assessment, it’s common to find the assessment team attribute their actions to the MITRE ATT&CK knowledge base so that high-level stakeholders can visually see what techniques were successful and administrators & defenders can understand the techniques that were performed in order to remediate or defend against them in the future. However, the commonly utilized MITRE knowledge base lacks formal documentation of Azure or AzureAD-related tactics, techniques, or procedures (TTPs) that assessment teams can attribute to. Over the past year, Microsoft has worked with some of the top Azure security researchers to create the Azure Threat Research Matrix (ATRM), a matrix that provides details around the tactics & techniques a potential adversary may use to compromise an Azure Resource or Azure Active Directory.
The Azure Threat Research Matrix (ATRM), is a knowledge base built to document known TTPs within Azure and Azure AD. The goal of the ATRM is twofold:
- To give security professionals an easily viewable framework to better visualize TTPs within Azure & Azure AD.
- To educate professionals about the potential configuration risks that accompany Azure & Azure AD when not following best practices.
Scope & Intent
The ATRM is primarily focused on AzureAD and Azure Resource TTPs. Due to the nature of AzureAD being used by other products, such as M365, occasionally it is necessary to include techniques or technique details that also pertain to other products. An example is AZT303 – Managed Device Scripting, which documents abusing InTune, which is integrated with AzureAD, to execute scripts on devices. Additionally, there are some AzureAD techniques (specifically around hybrid-joined devices) that are not included due to that technique already being present in MITRE ATT&CK. The intent of the ATRM is not to replace MITRE ATT&CK, but to rather be an alternative for pure Azure Resource & AzureAD TTPs. However, we would like feedback on this decision from the community!
The additional purpose of the ATRM is to educate readers on the potential of Azure-based tactics, techniques, and procedures (TTPs). Commands that relate to a technique are added with the intention of defenders building alerts on those commands. While the commands are also listed to show how to abuse a given technique, certain parts are omitted or obfuscated to prevent malicious abuse.
Walkthrough of the ATRM Structure
In order for security professionals to find ATRM helpful in understanding potential risks, it is important to first understand the layout and content within the matrix.
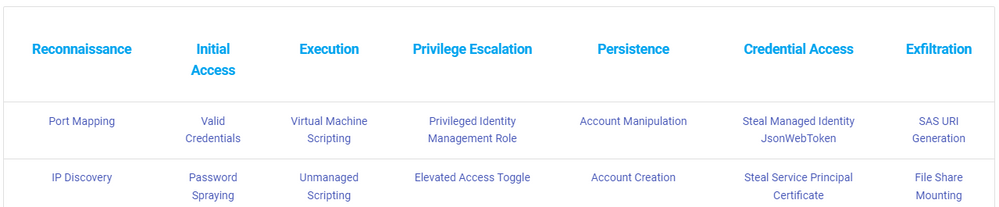
The top row designates the tactic, each sequentially having an ID starting with Reconnaissance at “AZT1”.
Figure 1: The top line represents the tactics and the columns represent the techniques that pertain to the tactic.
When clicking on a specific tactic, it will bring you to a list of techniques and sub-techniques associated with that tactic, with a short description.
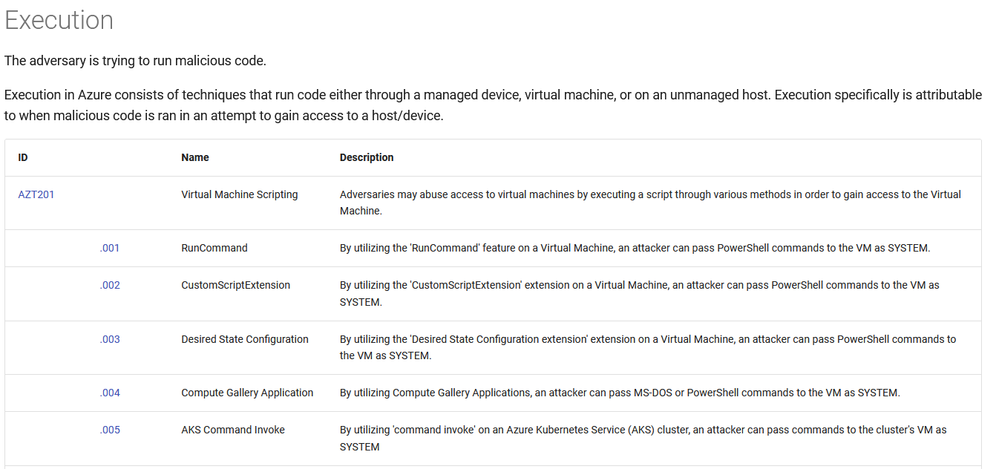
Figure 2: Part of the page for the ‘Execution’ tactic.
Clicking on the specific ID associated with the technique will bring you to the page on that technique or sub-technique.
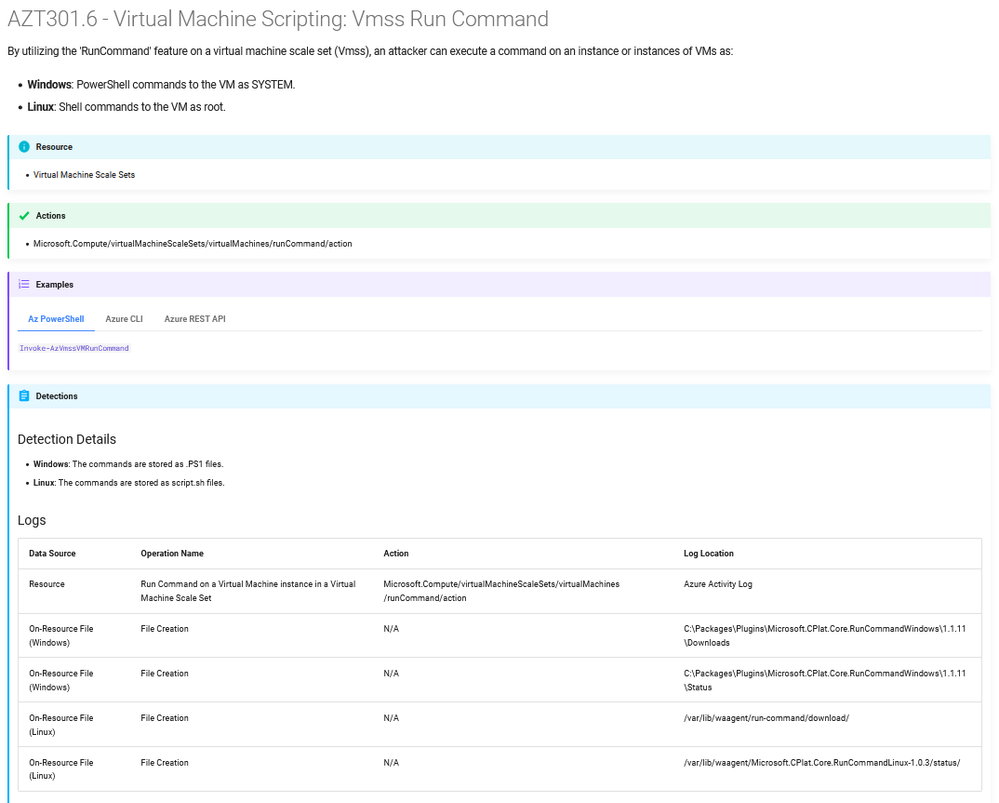
Figure 3: The page for a sub-technique, AZT301.6 – Virtual Machine Scripting: Vmss Run Command.
The technique/sub-technique specific pages have several key topics of information.
- Resource: The resource(s) that the technique effects
- Actions: What resource provider operation actions are required to utilize the technique
- Examples of commands to utilize the technique, including using the portal
- Any potential detections
- Additional Resources
The Azure Threat Research Matrix is meant to be product-agnostic, meaning specific detection queries are for technologies within Azure by default and not an additional, paid solution.
Community Collaboration
Over the past several months, we’ve collaborated with some of the top researchers in the Azure security community to put together the TTPs within the matrix as it is released today. Their contributions have been extremely helpful and are on the list of acknowledgments here. One of the intended goals of the ATRM is to be as comprehensive as possible. With the hundreds of services and offerings within Azure, it’s difficult for one person to know every potential TTP within Azure and Azure AD. While internally at Microsoft we have dedicated research teams whose jobs are to research the potential abuse scenarios within Azure & Azure AD, we recognize that the community also has a large contribution to the security of our products. With this in mind, we openly invite feedback on the ATRM, from new techniques to additional data added, we would love to hear the greater security community’s input. The Azure Threat Research Matrix is being released under the MIT license and hosted on GitHub, which will openly welcome pull requests and issues.
by Scott Muniz | Aug 3, 2022 | Security
This article was originally posted by the FTC. See the original article here.
Brought to you by Dr. Ware, Microsoft Office 365 Silver Partner, Charleston SC.
by Scott Muniz | Aug 3, 2022 | Security, Technology
This article is contributed. See the original author and article here.
VMware has released security updates to address multiple vulnerabilities in VMware’s Workspace ONE Access, Access Connector, Identity Manager, Identity Manager Connector, and vRealize Automation. A remote attacker could exploit some of these vulnerabilities to take control of an affected system.
CISA encourages users and administrators to review VMware Security Advisory VMSA-2022-0021 and apply the necessary updates.


Recent Comments